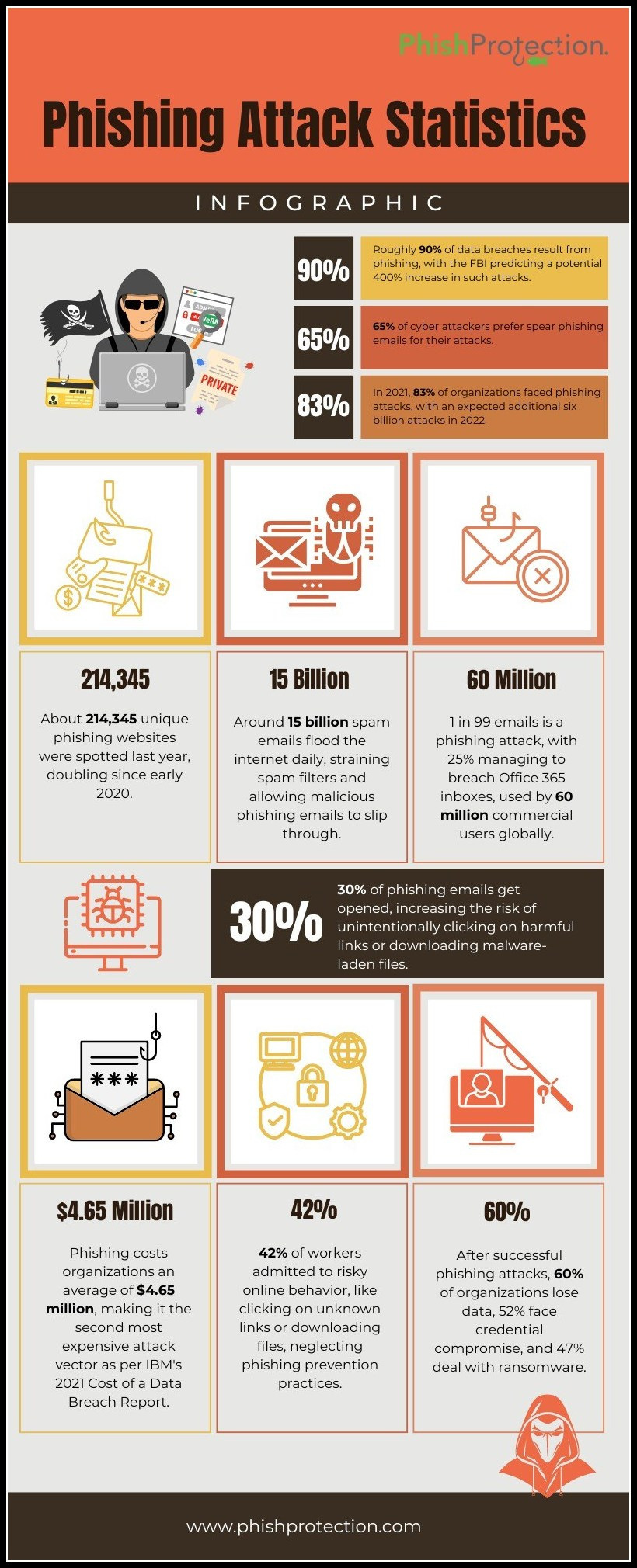
Threat actors deploy multiple vectors to launch their cyberattack campaigns. Learn about recent attacks involving email phishing, server compromise, and credential-stealing malware.
Cybersecurity experts have identified several malicious campaigns recently, including sophisticated email attacks that target cryptocurrency wallets. They discovered the campaign was designed for hot and cold wallets, the most popular cryptocurrency storage tools.
Other recent cyberattack campaigns include SharePoint phishing and Bandit credential-stealing malware. With online attacks looking menacing, global organizations must seek adequate email phishing protection to prevent such threats.
Sophisticated Email Attacks Target Cryptocurrency Wallets
Globally, more than 400 million users use crypto wallets. Online malicious actors are targeting these wallets as they have consistent internet connectivity. They primarily deploy phishing emails that impersonate reputed crypto exchanges. It lures technically incompetent individuals into verifying transactions, who unknowingly become victims.
Cold wallets are offline storage systems not easily accessible over the internet, but they have also come under attack. Researchers have discovered a targeted phishing campaign that tricks cold wallet owners with a deceptive blog post whose design resembles that of the Ripple website. It entices them by promising participation in an XRP token giveaway scheme.
Threat actors lead them from the post to a fake Ripple page, which prompts them to connect it to their respective hardware wallets. Thus, scammers can gain access to their accounts and initiate fraudulent transactions.
Regarding hardware wallet safety, cybersecurity experts recommend purchasing them only from trusted sources. They ask users to inspect them for signs of tampering and verify their legitimacy, besides updating firmware. Users must also store the seed phrase securely and use unique passwords to protect their wallets from infiltration.
Ransomware Attacks on Healthcare Organizations Surge:
In recent times, there has been a significant surge in ransomware attacks targeting healthcare organizations worldwide. These attacks not only disrupt critical healthcare services but also put patient lives at risk. Cybercriminals exploit vulnerabilities in healthcare systems, gaining unauthorized access and encrypting sensitive data. To combat this rising threat, healthcare organizations must invest in robust cybersecurity measures, including advanced threat detection and prevention mechanisms, regular data backups, and employee training on identifying and mitigating ransomware threats
SharePoint Phishing Scam Targets 1,600 Across US and Europe
In yet another phishing scam, online attackers have targeted at least 1,600 individuals across Europe, the US, and other countries. The sophisticated attack mechanism involves using legitimate servers from SharePoint, the collaborative platform of Microsoft.
The attackers exploit the platform’s native notification feature. Thus, they gain unauthorized access to credentials of various email accounts, including Yahoo!, AOL, Outlook, and Office 365.
The scammers send an authentic-looking notification to potential victims about sharing a file. Clicking on the file leads the target to a SharePoint server hosting a OneNote file that contains a malicious link. This link directs them to a phishing site camouflaged as the OneDrive login page, where malicious actors steal their email service credentials.
Cybersecurity experts recommend organizations invest in employee training to strengthen their stand against phishing emails and other online threats.
Artificial Intelligence and Machine Learning in Cybersecurity:
Artificial intelligence (AI) and machine learning (ML) are increasingly being leveraged in cybersecurity to enhance threat detection and response capabilities. These technologies enable organizations to analyze vast amounts of data, detect anomalies, and identify potential security incidents in real-time. AI and ML also aid in automating security processes, reducing response times, and improving overall cyber defense. As cyber threats evolve, integrating AI and ML into security strategies becomes essential for staying one step ahead of attackers. Additionally, AI-powered document automation can streamline the management of security reports, compliance records, and incident documentation, improving efficiency and accuracy. For organizations managing procurement and vendor processes, RFP AI can simplify and accelerate the creation, analysis, and evaluation of requests for proposals.
ImmuniWeb Introduces Email Security Test for Privacy and Compliance Verification
ImmuniWeb has developed a free email security test to bolster email protection to address the evolving cyber threat landscape. This test is the latest addition to the ImmuniWeb Community Edition. Thus, users now have a simple tool to assess their email server security and comply with the best practices.
While prioritizing email security, the test empowers organizations to check email server encryption compliance. They can also identify DNS misconfigurations that tend to weaken email security. The tool also enables them to detect compromised credentials that might grant threat actors unauthorized access to their email accounts.
The new tool further reinforces email phishing protection by detecting malicious campaigns targeting users. It can even identify the presence of email servers in blacklists and spam lists. This initiative from ImmuniWeb is a welcome move amidst rising instances of email security breaches through phishing.
The Role of Employee Awareness in Cybersecurity:
Employee awareness and education play a critical role in strengthening cybersecurity defenses. Human error remains a significant factor in many successful cyberattacks. Organizations must provide comprehensive training programs to educate employees about common cyber threats, phishing techniques, and best practices for secure behavior. By promoting a culture of cybersecurity awareness, organizations empower their workforce to become the first line of defense against cyber threats, reducing the likelihood of successful attacks.
Bandit Malware Targets Browsers, FTP, and Email Clients to Steal Credentials
In another development, cybersecurity experts have identified a new info-stealing malware called “Bandit” that steals credentials by targeting different browsers, FTP clients, and email accounts. It is sophisticated malware written in Go programming language to gain unauthorized access to cookies, logins, and credit card information. It even targets desktop crypto wallets of potential victims.
Bandit can evade both automated and manual analysis by using several anti-analysis techniques. It terminates execution on detecting virtual environments or analysis tools. The malware has been designed to capture information such as hardware IDs, screen dimensions, IP addresses, and MAC addresses.
It steals credentials by fetching the system’s external IP and comparing it to a list of blacklisted IP addresses. Thus it obtains MAC addresses before checking them against a blacklist. It also captures process snapshots to scan for blacklisted processes.
Emerging Threats in IoT Security:
With the proliferation of Internet of Things (IoT) devices, ensuring their security has become a pressing concern. IoT devices are susceptible to exploitation, and compromised devices can serve as entry points for cybercriminals. Organizations and individuals must prioritize IoT security by implementing strong authentication mechanisms, regular firmware updates, network segmentation, and monitoring for suspicious activities. Proactive security measures are vital to protect sensitive data and prevent IoT devices from becoming vulnerabilities in interconnected environments.
Final Words
Organizations must maintain robust security safeguards to draw their lines of defense. Besides strengthening email security, updating their antivirus software and patching security loopholes is imperative.
The cybersecurity landscape is evolving and looks increasingly menacing, with the attack mechanisms gaining further sophistication. At this juncture, a proactive stance and constant vigilance are vital to help organizations stay protected from phishing and other cybersecurity threats.