Phishing Watchdog – Stay Safe with Instant Alerts
Phishing Watchdog
PhishProtection.com “Phishing Watchdog” Is A Timeline of All Major Phishing Attacks Reported As They Breakout
Get Free Access to Phishing Protection Best Practices
An Updated Feed of All Significant Phishing Attacks
This is a comprehensive and frequently updated resource page that lists all the significant Phishing Attacks as they are discovered and happen online. Each attack is summarized here with links to further information about each attack. The list below is updated instantly with threat details as soon as the attack is verified to be authentic.
**
US clothing supplier Pro Wrestling Tees hit by data breach
23rd December 2021 | Target: **Pro Wrestling Tees **| Reported Here
Pro Wrestling Tees, which sells t-shirts designed by professional wrestlers, has discovered that some customers’ credit card numbers have been compromised in a data breach, according to a notification seen by The Daily Swig.
A letter apparently sent to potentially impacted customers from the Chicago-based company indicates that a malware-related compromise of customer names and payment card data came to light on November 1.

[above via Bleeping Computer post] Update 1
Global IT services provider Inetum hit by ransomware attack
24th December 2021 | Target: **Inetum **| Reported Here
Less than a week before the Christmas holiday, French IT services company Inetum Group was hit by a ransomware attack that had a limited impact on the business and its customers.
Inetum is active in more than 26 countries, providing digital services to companies in various sectors: aerospace and defense, banking, automotive, energy and utilities, healthcare, insurance, retail, public sector, transportation, telecom and media.

[above via Security Affairs post] Update 1
Microsoft: Khonsari ransomware hits self-hosted Minecraft servers
16th December 2021 | Target: **Minecraft servers **| Reported Here
Microsoft urges admins of self-hosted Minecraft servers to upgrade to the latest release to defend against Khonsari ransomware attacks exploiting the critical Log4Shell security vulnerability.
Mojang Studios, the Swedish video game developer behind Minecraft, released an emergency security update last week to address the bug tracked as CVE-2021-44228 in the Apache Log4j Java logging library(used by the game’s Java Edition client and multiplayer servers).

Monongalia Health System, Inc. Investigates and Addresses Data Security Incident
21st December 2021 | Target: **Monongalia Health System, Inc. **| Reported Here
Monongalia Health System, Inc., and its affiliated hospitals, Monongalia County General Hospital Company and Stonewall Jackson Memorial Hospital Company (collectively, “Mon Health”), announced that it recently investigated and addressed an email phishing incident, and is now notifying individuals, including patients, providers, employees, and contractors, whose information may have been involved.

[above via ZNet post] Update 1
Ubisoft discloses security breach impacting Just Dance gamer data
20th December 2021 | Target: **Ubisoft **| Reported Here
French video game maker Ubisoft said today that a misconfiguration in its IT infrastructure exposed gamer data for players of its Just Dance video game series.
The company is currently notifying all impacted users via email after disclosing the breach earlier today in a community forum post.

[above via ZNet post] Update 1
Credit card info of 1.8 million people stolen from sports gear sites
17th December 2021 | Target: **Sports gear sites **| Reported Here
Four affiliated online sports gear sites have disclosed a cyberattack where threat actors stole credit cards for 1,813,224 customers.
While not much is known about the attack, a law firm representing the four websites stated that personal information and credit card information, including full CVV, were stolen on October 1st, 2021.

[above via Secure Reading post] Update 1
Belgian defense ministry hit by cyberattack
20th December 2021 | Target: **Belgium **| Reported Here
Belgium’s ministry of defense confirmed on Monday it had been hit by a cyberattack.
Hackers exploited a vulnerability in software called Log4j, which was discovered earlier in December, a ministry spokesperson told local media. The ministry uncovered the attack last Thursday.
Cybersecurity officials across the world have rushed to patch the Log4j vulnerability over the past week. The glitch has affected a long list of software firms including Amazon and Microsoft.

[above via ZNet post] Update 1
Billion-dollar natural gas supplier Superior Plus hit with ransomware
14th December 2021 | Target: **Superior Plus **| Reported Here
Superior Plus, the number one propane distributor in Canada and number five distributor in the U.S., has reported a ransomware incident. It’s the second security incident involving a top company in the propane business in the last six months.
Superior reported having discovered the breach on December 12. The company’s announcement does not mention when the attackers originally gained access to its systems.

[above via Forbes post] Update 1, Update 2
McMenamins was hit by a ransomware attack. Here’s who is affected
16th December 2021 | Target: **McMenamins **| Reported Here
Portland brewery and hotel chain McMenamins suffered a Conti ransomware attack over the weekend that disrupted the company’s operations.
McMenamins is a popular chain of restaurants, pubs, breweries, and hotels located in Oregon and Washington.
The ransomware attack occurred over the weekend, on December 12th, with sources telling BleepingComputer that the Conti gang conducted it.

[above via Bleeping Computer post]
Hellmann hit by cyber attack
9th December 2021 | Target: **Hellmann **| Reported Here
Hellmann Worldwide Logistics has been hit by a cyber attack that has impacted operations.
On December 9, the German logistics services company said external security specialists are working on restoring operations, but it is currently unable to confirm whether any data has been leaked.

[above via ZDNet post] Update 1, Update 2
South Australian government employee data taken in Frontier Software ransomware attack
10th December 2021 | Target: **South Australian government **| Reported Here
South Australia Treasurer Rob Lucas said on Friday that state government employee data has been exfiltrated as part of a ransomware attack on payroll provider Frontier Software.
Lucas said the company has informed government that some of the data have been published online, with at least 38,000 employees and up to 80,000 government employees possibly having their data accessed.

[above via ITNews post] Update 1, Update 2
Volvo confirms it was hit by security breach
10th December 2021 | Target: **Volvo **| Reported Here
Swedish car giant Volvo has confirmed it has suffered a security breach, with internal company data thought to have been affected.
In a statement, the company said that it had “become aware that one of its file repositories has been illegally accessed by a third party.”
Volvo says an initial investigation into the breach suggests that “a limited amount” of company’s R&D information has been stolen, and that this could have an effect on its overall operations.

[above via Tech Crunch post] Update 1, Update 2
New Cerber ransomware targets Confluence and GitLab servers
7th December 2021 | Target: **GitLab servers **| Reported Here
Cerber ransomware is back, as a new ransomware family adopts the old name and targets Atlassian Confluence and GitLab servers using remote code execution vulnerabilities.
As ransomware began picking up pace in 2016, a new Cerber ransomware operation emerged that quickly became one of the most prolific gangs at the time. However, its activity slowly tapered off until it disappeared at the end of 2019.

[above via Cyware post] Update 1
FBI: Cuba ransomware group hit 49 critical infrastructure organizations
6th December 2021 | Target: **Infrastructure Sectors **| Reported Here
Last Friday, the FBI released a new notice regarding the Cuba ransomware, stating that a threat group has attacked 49 entities spanning five different critical infrastructure sectors. The FBI also noted that the group has likely made at least $43.9 million in ransom payments. The threat group deploying the Hancitor malware is targeting enterprises in the financial, government, healthcare, manufacturing, and information technology sectors. The Hancitor malware is used to gain entry into Windows systems and is a loader known for dropping or executing Remote Access Trojans (RATs).

[above via PCMag post] Update 1
Cyberattack forces supermarket Spar to close some stores
6th December 2021 | Target: **Spar **| Reported Here
More than 300 branches of the convenience store chain Spar in the north of England have been hit by a cyberattack, forcing many of them to close.
The attack hit the company’s computer systems, causing a “total IT outage” that has prevented staff from taking card payments and locked them out of emails.
Some branches of the chain, one of the few places to buy groceries in many remote communities, are accepting cash but the rest have been forced to close entirely.

[above via BBC post] Update 1, Update 2
BitMart says it will compensate victims of $196 million hack and restore trading
5th December 2021 | Target: **BitMart **| Reported Here
Crypto trading platform Bitmart says it will use its own money to reimburse victims of a large-scale security breach, in which hackers took as much as $196 million.
Bitmart claims hackers withdrew about $150 million in assets. However, blockchain security and data analytics firm Peckshield, which first publicized the hack, estimates that the loss is closer to $200 million. CNBC reached out to Bitmart to ask about the multimillion dollar discrepancy, but the exchange declined to comment on this point.

[above via Zdnet post] Update 1
The virus attack on Nordic Choice Hotels’ IT systems
6th December 2021 | Target: **Nordic Choice Hotels **| Reported Here
In the wake of the virus attack on the night of 2 December, Nordic Choice Hotels has over the weekend worked to map the extent of the virus attack on the IT systems.
On the night of 2 December, Nordic Choice Hotels was hit by a virus attack on our IT systems. The virus infected systems for bookings, check-in and check-out, as well as payment solutions. After the incident, we have worked around the clock with internal and external resources to get an overview of the extent of the event, as well as restore the systems so that the operation of the hotels can return to normal.

[above via Bleeping Computer post] Update 1
Panasonic discloses data breach after network hack
29th November 2021 | Target: **Panasonic **| Reported Here
Japanese tech giant Panasonic has confirmed a data breach after hackers gained access to its internal network.
Panasonic said in a press release dated November 26 that its network was “illegally accessed by a third party” on November 11 and that “some data on a file server had been accessed during the intrusion.” However, when reached, Panasonic spokesperson Dannea DeLisser confirmed that the breach began on June 22 and ended on November 3 - and that the unauthorized access was first detected on November 11.

[above via Techcrunch post] Update 1, Update 2
IKEA email systems hit by ongoing cyberattack
26th November 2021 | Target: **IKEA **| Reported Here
Ikea is reportedly reeling under an ongoing cyberattack perpetrated through phishing emails sent via compromised Microsoft Exchange servers.
According to BleepingComputer, the homeware giany is alerting its employees of the campaign conducted through the classic reply-all email chain attack.

[above via Techradar post] Update 1
More than 500,000 Utahns’ sensitive information possibly hacked
18th November 2021 | Target: **Utah **| Reported Here
Utah Imaging Associates (UIA), a Utah-based radiology center, has announced a data breach affecting 582,170 people after their personal information was exposed.
According to the data breach notification sent to affected individuals, the security incident was discovered on September 4, 2021, and was remediated on the same day.

[above via Bleeping Computer post] Update 1
GoDaddy Security Breach Exposes 1.2 million WordPress Users’ Data
17th November 2021 | Target: **GoDaddy **| Reported Here
Customer information including email addresses, account numbers and passwords related to more than one million GoDaddy users was exposed in a data breach, the company said Monday in a regulatory filing.
According to the web hosting company’s Securities and Exchange Commission notification, the breach affected users of WordPress, a web-based content management system used by bloggers and websites. The systems were first compromised on Sept. 6 when an unauthorized person used a stolen password to gain access, but the breach wasn’t discovered until Nov. 17.

[above via c|net post] Bleeping Computer
Costco discloses data breach after finding credit card skimmer
12th November 2021 | Target: **Costco **| Reported Here
Costco customers at four of the retailer’s Chicago-area warehouses may have had their payment information compromised after employees discovered five card-skimming devices during routine PIN pad inspections at the end of August.
“We promptly removed the skimmers, notified law enforcement, and engaged a forensics firm to analyze the devices,” A Costco spokesperson told FOX Business in a statement. “It appears that these skimmers had the ability to capture information on the magnetic stripe of a payment card, including name, card number, expiration date, and CVV.”

[above via Fox Business post] Update 1
Stor-a-File hit by ransomware after crooks target SolarWinds Serv-U FTP software
10th November 2021 | Target: **Stor-a-File **| Reported Here
Stor-а-File, а British dаtа cаpture аnd storаge compаny, suffered а rаnsomwаre аttаck in Аugust thаt exploited аn unpаtched instаnce of SolаrWinds’ Serv-U FTP softwаre.
The compаny informed its clients аbout the September аttаck, аnd told The Register thаt it refused to pаy. We understаnd some dаtа hаs been leаked by rаnsomwаre criminаls on а Tor blog.

[above via Blackweb Security post]
Electronics retail giant MediaMarkt hit by ransomware attack
8th November 2021 | Target: **MediaMarkt **| Reported Here
MediaMarkt and its stores have been hit by a large-scale cyber-attack. The electronics retailer’s international computer systems are said to have been ‘held hostage’ by a ransomware attack.
Everything encrypted
MediaMarkt employees were told this morning not to use the computers in the stores. They have become the victim of a cyber-attack. This also applies to the Dutch, Belgian and German stores. The staff is asked to disconnect the cash registers from the Internet and not to restart the systems, RTL Nieuws reports.

[above via Retail Detail post] Update 1
Robinhood discloses data breach impacting 7 million customers
8th November 2021 | Target: **Robinhood **| Reported Here
Robinhood Markets on Monday afternoon disclosed an unauthorized party obtained access to personal information for nearly one-quarter of the company’s nearly 20 million users, marking one of the biggest security breaches ever for the popular online brokerage.

[above via Forbes post] Update 1 / Update 2
UK Labour Party discloses data breach after ransomware attack
3rd November 2021 | Target: **UK Labour Party **| Reported Here
The Labour Party has been affected by a “cyber incident” involving its members’ data.
Labour said it was told on 29 October that it had been affected by the event by a third party firm that handled membership data on its behalf.
As a result, “a significant quantity” of party data was “rendered inaccessible on their systems”.

[above via BBC post] Update 1 Update 2
Canadian province health care system disrupted by cyberattack
1st November 2021 | Target: **N.L. health-care system **| Reported Here
The Canadian province of Newfoundland and Labrador has suffered a cyberattack that has led to severe disruption to healthcare providers and hospitals.
The attack took place on October 30th, causing regional health systems to shut down their networks and cancel thousands of medical appointments. This outage affected health systems in Central Health, Eastern Health, Western Health, and the Labrador-Grenfell Regional Health authorities.

[above via Bleeping Computer post] Update 1
Suspected Iranian hack hits Israeli LGBT site
30th October 2021 | Target: **LGBTQ Apps & Sites **| Reported Here
The hacker group “Black Shadow” has leaked data from various Israeli companies, such as LGBTQ dating app “Atraf”, Dan bus company and tour booking company Pegasus on Saturday night.
Earlier in the day, they leaked data from the Kavim bus app after previous threats. “They did not contact us …So first data is here,” the group said on Telegram, affixing a photo of what appeared to be a database of Israeli citizens’ personal information. “If you do not contact us, (sic) it will be more,” added the group.

[above via J Post post] Update 1 / Update 2
Fullerton Health vendor hit by hackers, exposing customer data
26th October 2021 | Target: Fullerton Health** **| Reported Here
“Fullerton Health confirms that its own IT network, systems and databases have not been accessed or breached,” it added.
In a statement, Agape said it discovered on Oct 19 that client information was compromised due to “unauthorised access by a malicious third party”.

[above via Channel News Asia post] Update 1
Brazilian insurance giant Porto Seguro hit by cyberattack
15th October 2021 | Target: **Porto Seguro **| Reported Here
And the cases of virtual attacks targeting companies continue to rise, with Porto Seguro being the most recent organization to be hit by one of these crimes. Due to the scam, the service channels and in some systems of the insurance company have been unstable since Thursday

[above via Clare People post]
Acer confirms second cyberattack in 2021
14th October 2021 | Target:** Acer **| Reported Here
The second Acer cyberattack, this 2021 is now confirmed after involved hackers themselves shared that they have access to the computer manufacturer’s servers.
Network cables are plugged in a server room on November 10, 2014 in New York City. U.S. President Barack Obama called on the Federal Communications Commission to implement a strict policy of net neutrality and to oppose content providers in restricting bandwith to customers.
This detail was announced after the ransomware attack back in March, which also targeted Acer. The cybercriminals claimed that they breached the offices of the giant tech firm in India in the second week of October.

[above via Tech Times post] Update 1
Olympus US systems hit by cyberattack over the weekend
12th October 2021 | Target:** Olympus Corporation **| Reported Here
Researchers say that BrewDog exposed the personally identifiable information (PII) of roughly 200,000 shareholders for the best part of 18 months.
According to PenTestPartners, BrewDog “declined to inform their shareholders and asked not to be named” in the research revealing the security flaw.

[above via Zdnet post] Update 1 / Update 2
BrewDog exposed data for over 200,000 shareholders and customers
8th October 2021 | Target:** BrewDog **| Reported Here
Researchers say that BrewDog exposed the personally identifiable information (PII) of roughly 200,000 shareholders for the best part of 18 months.
According to PenTestPartners, BrewDog “declined to inform their shareholders and asked not to be named” in the research revealing the security flaw.

[above via Zdnet post] Update 1 / Update 2
Vidar Stealer Returns and Has a New Target: Mastodon
7th October 2021 | Target:** Mastodon **| Reported Here
Vidar stealer is back and has a new target: this time, the Mastodon social media network is being abused in a fresh malicious campaign. The goal is C2 configuration achievement without being noticed.

[above via Heimdal Security post] Update 1 / Update 2
Twitch Confirms Massive Data Breach
6th October 2021 | Target:** Twitch, TV network **| Reported Here
Twitch, the popular if frequently controversial Amazon-owned streaming service with 30 million daily visitors, confirmed reports on Wednesday that a breach had taken place after data, including possibly its entire source code and other sensitive company information, was leaked online.

[above via Forbes post] Update 1 / Update 2
Sandhills online machinery markets shut down by ransomware attack
2nd October 2021 | Target:** Sandhills **| Reported Here
Popular online auction bidding sites for farm equipment and farmland were the victim of a recent ransomware attack. As a result, sites such as TractorHouse, EquipmentFacts, AuctionTime and HiBid have been offline since Friday.
Over the weekend, the Lincoln Journal Star confirmed Sandhills Global, which hosts various online auction websites, was the target of a ransomware attack.

[above via The Packer post] Update 1 / Update 2
Hydra malware targets customers of Germany’s second largest bank
1st October 2021 | Target:** Commerzbank **| Reported Here
Experts warn of a malware campaign targeting European e-banking platform users with the Hydra banking trojan. According to malware researchers from the MalwareHunterTeam and Cyble, the new campaign mainly impacted the customers of Commerzbank, Germany’s second-largest bank. Hydra is an Android Banking Bot that has been active at least since early 2019.

[above via Security-Affairs post]
Hackers Compromise Bitcoin.org Website, Promoting Giveaway Scam
23rd September 2021 | Target:** Bitcoin.org **| Reported Here
Bitcoin.org, one of the first websites about Bitcoin (BTC), has been hacked by online scammers and down as of the time of writing.
Cobra, Bitcoin.org’s anonymous curator, announced on Sept. 23 that Bitcoin.org was compromised, with hackers managing to put up a scam notice on the site.
“Looks like Bitcoin.org got hacked and the entire site replaced with a scam asking for free Bitcoin. Do not send funds to that address,” Bitcoin developer Matt Corallo reported on Twitter.

[above via Coin-Telegraph post] Update 1 / Update 2
Marketron Hit With Cyberattack. Virtually All Of Its Systems Are Offline.
20th September 2021 | Target:** Marketron Broadcast Solutions **| Reported Here
BlackMatter ransomware gang over the weekend hit Marketron, a business software solutions provider that serves more than 6,000 customers in the media industry.
Marketron provides cloud-based revenue and traffic management tools for broadcast and media organizations. It specializes in revenue management and audience engagement, handling advertising revenue of $5 billion every year.

[above via Bleeping Computer post] Update 1
Horizon House notifying patients of ransomware attack in March
20th September 2021 | Target:** Horizon House, Inc **| Reported Here
Data breaches at two American mental healthcare providers may have exposed thousands of individuals’ personal health information (PHI).
Horizon House, Inc., which is in Philadelphia, Pennsylvania, warned that 27,823 people might have been impacted by a cyber-attack that took place in the late winter.
The mental health and residential treatment services provider detected suspicious activity on its IT network on March 5. An investigation revealed that the healthcare provider’s IT system had been infected with ransomware.

[above via Infosecurity Magazine post]
US Eye-Care Providers Report Data Breaches
20th September 2021 | Target:** Simon Eye Management **| Reported Here
Simon Eye, a US chain of optometry clinics, has reported a data breach potentially impacting more than 144,000 individuals.
The possible compromise of sensitive personal data arose from unauthorized access to employee email accounts over a seven-day period between May 12-18, 2021, according to a data breach notice on the Simon Eye website.
Simon Eye said the attackers “attempted to engage in wire transfer and invoice manipulation attacks against the company, none of which were successful”.

[above via PortSwigger post] Update 1
New Cooperative hit by $5.9M BlackMatter ransomware attack
20th September 2021 | Target:** New Cooperative **| Reported Here
U.S. farmers cooperative NEW Cooperative has suffered a BlackMatter ransomware attack demanding $5.9 million not to leak stolen data and provide a decryptor.
NEW Cooperative is a farmer’s feed and grain cooperative with over sixty locations throughout Iowa.
In a weekend ransomware attack, the threat actors demand a 5.9 million dollar ransom, which will increase to $11.8 million if a ransom is not paid in five days.
These ransom demands are a starting point for negotiations and usually lead to significantly smaller payments if a victim decides to pay.

[above via Bleeping Computer post] Update 1 / Update 2
Republican Governors Association was hacked earlier this year
16th September 2021 | Target:** Republican Governors Association (RGA) **| Reported Here
The Republican Governors Association (RGA) revealed in data breach notification letters sent last week that its servers were breached during an extensive Microsoft Exchange hacking campaign that hit organizations worldwide in March 2021.
RGA is a US political organization and a tax-exempt 527 group that provides Republican candidates with the campaign resources needed to get elected as governors across the country.

[above via Bleeping Computer post] Update 1 / Update 2
Customer Care Giant TTEC Hit By Ransomware
15th September 2021 | Target:** TTEC **| Reported Here
US customer experience technology giant TTEC has announced a “cybersecurity incident”, confirming to employees that it was hit with ransomware.
The company, with nearly 61,000 employees and billions in annual revenue, sent a message to employees this week warning them not to click on a link titled ”!RA!G!N!A!R!” according to KrebsonSecurity. The message indicates that the prolific Ragnar Locker ransomware group may have launched the attack or someone trying to impersonate them.

[above via Zdnet post] Update 1
Ransomware scammers target artists with fake Krita revenue deals
14th September 2021 | Target:** Krita **| Reported Here
The Krita digital painting application is currently being targeted by ransomware authors. Available on Steam and other platforms, it’s a powerful tool with a very cheap purchase price and great reviews. A perfect bit of bait to start reeling in potential victims, in other words.

[above via Malware Bytes post] Update 1
MyRepublic discloses data breach exposing government ID cards
10th September 2021 | Target:** MyRepublic **| Reported Here
MyRepublic says almost 80,000 of its mobile subscribers in Singapore have had their personal data compromised, following a security breach on a third-party data storage platform. The affected system had contained identity verification documents needed for mobile services registration, including scanned copies of national identity cards and residential addresses of foreign residents.
The “unauthorised data access” incident was uncovered on August 29 and the relevant authorities had been informed of the breach, said MyRepublic in a statement Friday.

[above via Zdnet post] Update 1 / Update 2
Howard University Hit by a Ransomware Attack
7th September 2021 | Target:** Howard University **| Reported Here
Howard University, one of the largest historically Black schools in the United States, canceled classes Tuesday after a ransomware attack.
The attack shut down the campus Wi-Fi, and nonessential employees were instructed to not report to work, the university announced Monday. In-person classes will resume Wednesday, but online classes remain canceled until at least Thursday.

[above via CNBC post] Update 1 / Update 2
Jenkins project discloses security breach
6th September 2021 | Target:** Jenkins Software **| Reported Here
In a statement, Jenkins documentation officer Mark Waite explained that the affected server was taken offline and the team is investigating the impact of the issue.
“At this time we have no reason to believe that any Jenkins releases, plugins, or source code have been affected. Thus far in our investigation, we have learned that the Confluence CVE-2021-26084 exploit was used to install what we believe was a Monero miner in the container running the service,” Waite wrote.

[above via Zdnet post] Update 1
Student, Teacher Personal Information Taken in Dallas ISD Data Theft
2nd September 2021 | Target:** Dallas ISD **| Reported Here
The Dallas Independent School District says they learned of a data breach about a month ago that affects former and current students, alumni, parents, and district employees.
In an FAQ on their website, the district said someone downloaded data from their server and temporarily stored it on an encrypted cloud storage site. The district said the data have since been removed from that site and that there is no evidence it was otherwise accessed, disseminated, or sold but that they cannot be sure the data has not been shared publicly until a forensic analysis is completed.

[above via NBCDFW post] Update 1
DuPage Medical Group notifying 600,000 patients about a data breach
30th August 2021 | Target:** Dupage Medical Group **| Reported Here
DuPage Medical Group experienced a security breach that reportedly may affect 600,000 patients, the group announced Aug. 30. Now, the medical group, Illinois’ largest independent physician group, is mailing letters to notify patients of the cyberattack.
The unauthorized use occurred between July 12-13 and caused a network outage. On Aug. 17, after an investigation by cyber forensic specialists, the medical group determined patient information may have been reached by “unauthorized actors.”

[above via Chicago Tribune post] Update 1
LockBit Gang to Publish 103GB of Bangkok Air Customer Data
30th August 2021 | Target:** Bangkok Airways **| Reported Here
The LockBit ransomware gang has apparently struck again, having purportedly stolen 103GB worth of files from Bangkok Airways and promising to release them tomorrow, on Tuesday.
A Dark Web intelligence firm calling itself DarkTracer (apparently a separate intel firm than the better-known DarkTrace) tweeted a screen capture of a countdown clock from LockBit 2.0 that, as of Friday, showed four and a half days left. “LockBit ransomware gang has announced Bangkok Airways on the victim list,” DarkTracer tweeted. “It announced that 103GB of compressed files will be released.”

[above via Threat Post post] Update 1 / Update 2
Boston Public Library discloses cyberattack
27th August 2021 | Target:** Boston Public Library **| Reported Here
The Boston Public Library said Friday that it is experiencing “a systemwide technical outage” after being targeted by a cyberattack.
“On Wednesday morning, 8/25, the Boston Public Library experienced a systemwide technical outage due to a cybersecurity attack, pausing public computer and public printing services, as well as some online resources,” the library said in a statement. “Affected systems were taken offline immediately, and proactive steps were taken to isolate the problem and shutdown network communication. There is currently no evidence that sensitive employee or patron data has been disclosed.”

[above via NBC Boston post] Update 1
New Hampshire town loses $2.3 million to overseas scammers
24th August 2021 | Target:** Peterborough, Hampshire **| Reported Here
The town of Peterborough, New Hampshire, said Monday that it has lost $2.3 million in taxpayer dollars as the result of a cyberattack.
“It pains us to inform the residents and taxpayers of Peterborough that, like so many other towns and cities, we have fallen victim to an internet-based crime that has defrauded our taxpayers of $2.3m,” Select Board Chairman Tyler Ward and Town Administrator Nicole MacStay said in a press release posted to Facebook.

[above via NBC Boston post] Update 1 / Update 2
Chase bank accidentally leaked customer info to other customers
17th August 2021 | Target:** Chase bank **| Reported Here
New York City-based JPMorgan Chase Bank has admitted that a technical bug on its online banking website and app led to the accidental leak of customer data… to other customers.
Incidents of customer data breaches have been on the rise over the past year, alongside numerous instances of organized, targeted cyberattacks affecting organizations big, small, and in-between. Many incidents came about as bad actors, emboldened by the lack of data security on many platforms and targeting go-between service providers, orchestrated cyber intrusions that have ended up affecting thousands of businesses globally.

[above via Techhq post]
Data Breach at Georgia Health System
11th August 2021 | Target:** Georgia Health System **| Reported Here
A ransomware attack on one of southeast Georgia’s largest healthcare systems exposed both staff and patients’ protected health information (PHI.)
St. Joseph’s/Candler (SJ/C) announced on August 10 that it experienced “a data security incident that may have resulted in unauthorized access to patient and employee information,” according to a press release.
The Georgia-based healthcare system, which has 116 service locations across the state, identified suspicious activity in its network on June 17, 2021, according to the press release

[above via Health IT Security post]
Accenture confirms hack after LockBit ransomware data leak threats
11th August 2021 | Target:** Accenture **| Reported Here
Billion-dollar tech services firm Accenture is downplaying an alleged ransomware attack that the Lockbit ransomware group announced on Tuesday night.
Accenture was listed on the group’s leak site next to a timer set to go off on Wednesday. The ransomware group added a note that said, “These people are beyond privacy and security. I really hope that their services are better than what I saw as an insider. If you’re interested in buying some databases, reach us.”

[above via Zdnet post] Update 1 / Update 2
Crytek Customer Data Stolen After Egregor Ransomware Attack
10th August 2021 | Target:** Crytek **| Reported Here
The Egregor group has claimed another victim in their cybersecurity attack spree that started in September 2020. The victim in question is the well-known game developer and publisher Crytek. They confirmed that the Egregor ransomware gang breached their network in October 2020.
This attack resulted in several encrypted systems and files with customers’ personal info stolen and later leaked on the dark web. The company talked about the attack in a letter sent to impacted individuals earlier this month.

[above via Wccftech post] Update 1
Cyberattack Hits Chanel Korea
9th August 2021 | Target:** Chanel Korea **| Reported Here
The Korean arm of French luxury brand Chanel has issued an apology after personal data belonging to its customers was exposed.
In a statement issued earlier this week, Chanel Korea blamed the data leak that happened on August 8 on a recent cyber-attack. A database belonging to the famed perfume and fashion brand is believed to have been compromised by a hacker or hackers at some point between August 5 and 6.

[above via Infosecurity post] Update 1
Hardware giant Gigabyte hit by ransomware attack
6th August 2021 | Target:** Gigabyte Technology **| Reported Here
GIGABYTE, the Taiwanese manufacturer and distributor of computer hardware was a victim of the RansomEXX ransomware gang where 112GB of data were claimed to be stolen.
The leak site of the RansomEXX gang does not include the company name as of now, but it was found that the attack was conducted by this ransomware gang.

[above via Cybersafe post] Update 1
OrangeTee real estate group suffers data security breach
6th August 2021 | Target:** OrangeTee **| Reported Here
OT Group, the holding company of OrangeTee & Tie and OrangeTee Advisory, has suffered a data security breach, the Singaporean real estate group announced Friday (August 6th).
The company said it received an email from a third party claiming to have accessed its computer network. The incident was reported to the appropriate authorities.

[above via The Bharat Express News post]
StarHub suffers data breach
6th August 2021 | Target:** StarHub **| Reported Here
A recent security report notes that the confidential information of more than 57,000 StarHub customers has been leaked in what appears to be a severe oversight by the Singapore-based telecommunications company. The company’s security teams discovered the data breach this weekend, when they found a file posted without the company’s authorization on a download website operated by third parties.

[above via Security News Paper post] Update 1
Isle of Wight schools hit by ransomware
3rd August 2021 | Target:** Isle of Wight Education Federation **| Reported Here
Six schools on the Isle of Wight and their umbrella organisation have been targeted by a ransomware attack, leaving teachers and pupils unable to access their online systems and causing disruption to the start of the new school year in September.
The attack hit the schools between 28 and 29 July, according to their umbrella organisation, the Isle of Wight Education Federation, which resulted in their data becoming encrypted and inaccessible

[above via Computer Weekly post] Update 1 / Update 2
Estonia arrests hacker who stole 286K ID scans from govt database
29th July 2021 | Target:** Government Database **| Reported Here
Estonian officials arrested a suspect who exploited a vulnerability and downloaded 286,438 ID scans from the Identity Documents Database.
The attacker was arrested on July 23, and the identity of the suspect was not disclosed; he was only identified as a Tallinn based male.

[above via Secure Reading post] Update 1
Calgarians’ personal data exposed in parking authority security breach
28th July 2021 | Target:** Calgary Parking Authority **| Reported Here
The Calgary Parking Authority left one of its data servers unsecured for months, potentially exposing thousands of drivers’ personal information.
The parking authority was made aware of the security lapse, which was originally reported by tech industry news site TechCrunch, on Tuesday.

Ransomware attack on Grass Valley
27th July 2021 | Target:** City of Grass Valley **| Reported Here
GRASS VALLEY, Calif. (KTXL) - City officials in Grass Valley confirmed its information systems were hacked Wednesday morning.
Police say hackers copied city data and threatened to post it on the web unless the city paid a ransom.
City leaders said it was a privacy risk they just weren’t willing to take so they decided to fork over the cash.

[above via Fox40 post] Update 1
UC San Diego Health Announces Data Breach
27th July 2021 | Target:** UC San Diego Health **| Reported Here
UC San Diego Health, the academic health system of the University of California, San Diego, has disclosed a data breach after the compromise of some employees’ email accounts.
UC San Diego Health is one of the nation’s best hospitals, being repeatedly ranked as the best health care system in San Diego, according to the 2021-2022 U.S. News & World Report survey.

[above via Bleeping Computer post] Update 1
Saudi Aramco data breach sees 1 TB stolen data for sale
19th July 2021 | Target:** Saudi Aramco **| Reported Here
Saudi Aramco, the world’s largest oil producer, confirmed on Wednesday that some of its company files had been leaked via a contractor, after a cyber extortionist claimed to have seized troves of its data last month and demanded a $50 million ransom from the company.
Aramco said in a statement that it had “recently become aware of the indirect release of a limited amount of company data which was held by third-party contractors.” The oil company did not name the supplier or explain how the data were compromised.

[above via Arstechnica post] Update 1 / Update 2
Ransomware hits Campbell Conroy & O’Neil, P.C. (Campbell), a US law firm
18th July 2021 | Target:** Campbell Conroy & O’Neil **| Reported Here
Campbell Conroy & & O’Neil, P.C. (Campbell), a United States law firm counseling lots ofFortune 500 as well as Global 500 companies, has actually divulged an information violation complying with a February 2021 ransomware strike.
Campbell’s client list consists of top-level companies from different market markets, consisting of auto, aeronautics, power, insurance policy, pharmaceutical, retail, friendliness, as well as transport.

[above via Tech Widdle post] Update 1
Cyberattack on Moldova’s Court of Accounts destroyed public audits
16th July 2021 | Target:** Moldova’s Court **| Reported Here
Moldova’s “Court of Audit” has suffered a cyber attack that has led to the destruction of public databases and agency audits.
The Moldovan Court of Accounts is a government authority that conducts audits of public financial resources and government agencies to comply with international standards.

[above via News Block post] Update 1
Ransomware attack at Comparis resulted in data breach
15th July 2021 | Target:** Comparis **| Reported Here
Leading Swiss price comparison platform Comparis has notified customers of a data breach following a ransomware attack that hit and took down its entire network last week.
Comparis is one of the most popular Swiss websites with more than 80 million visits every year and the largest Swiss online marketplace for property and cars.

[above via Bleeping Computer post] Update 1
Nepal Telecom call details stolen by Chinese hackers
12th July 2021 | Target:** Nepal Telecom **| Reported Here
Nepal Telecom has been subjected to a terrible “cyber attack” from China. Chinese hackers have attacked Nepal Telecom and stolen the call details of all Nepali users.
By hacking the Oracle Glass Fish Server used by the telecom company, the Chinese hackers have stolen all the call details of Nepalis.

[above via Ciso Economictimes Indiatimes post] Update 1 / Update 2
Fashion retailer Guess discloses data breach after ransomware attack
12th July 2021 | Target:** Guess **| Reported Here
American fashion brand Guess was hit by a ransomware attack, now the company is disclosing a data breach and is notifying affected customers.
The attack was likely carried out by the DarkSide ransomware gang that in April listed Guess on their data leak site claiming to have stolen over 200 GB of files.

[above via Security-affairs post] Update 1
Mint Mobile hit by a data breach
10th July 2021 | Target:** Mint Mobile **| Reported Here
Carrier Mint Mobile has revealed it was the victim of a data breach, one which allowed a number of customer phone numbers to be ported out to another carrier, along with possible access to subscriber data.
An email sent on Saturday to affected customers by Mint Mobile discloses there was a breach of the carrier’s systems. The breach, which occurred between June 8 and June 10, reveals a “very small number of Mint Mobile subscribers’ phone numbers were affected by the incident.

[above via Apple Insider post] Update 1
Forefront Dermatology reports breach of 2.4M patient records
9th July 2021 | Target:** Forefront Dermatology **| Reported Here
Forefront Dermatology S.C, a Wisconsin-based dermatology practice with affiliated offices in 21 states plus Washington, D.C., is notifying 2.4 million patients, employees and clinicians of a recent hacking incident. The incident apparently involved a ransomware strain known as “Cuba.”

[above via Data Breach Today post] Update 1
Morgan Stanley reports data breach after vendor Accellion hack
8th July 2021 | Target:** Morgan Stanley **| Reported Here
Morgan Stanley suffered a data breach that exposed sensitive customer data, and it became the latest known casualty of hackers exploiting a series of now-patched vulnerabilities in Accellion FTA, a widely used third-party file-transfer service.
The data obtained included names, addresses dates of birth, social security numbers, and affiliated corporate company names, Morgan Stanley said in a letter first reported by Bleeping Computer. A third-party service called Guidehouse, which provides account maintenance services to the financial services company, was in possession of the data at the time.

[above via Arstechnica post] Update 1 / Update 2
Hackers Scrape 90,000 GETTR User Emails, Surprising No One
6th July 2021 | Target:** Gettr **| Reported Here
Hackers were able to scrape the email addresses and other data of more than 90,000 GETTR users.
On Tuesday, a user of a notorious hacking forum posted a database that they claimed was a scrape of all users of GETTR, the new social media platform launched last week by Trump’s former spokesman Jason Miller, who pitched it as an alternative to “cancel culture.” The data seen by Motherboard includes email addresses, usernames, status, and location.

[above via Vice post] Update 1 / Update 2
Ransomware Attacks Hits PractiseFirst
5th July 2021 | Target:** Practicefirst **| Reported Here
Practicefirst, an Amherst, New York-based medical management services provider, on July 1 reported to federal regulators a breach that occurred late last year.
The company’s breach notification statement appears to indicate that the firm paid a ransom in exchange for promises that the attackers would destroy and not further disclose files stolen in the incident.

[above via Govinfosecurity post] Update 1
16k L&I Workers’ Data Compromised
2nd July 2021 | Target:** Pacific Market Research (PMR) **| Reported Here
Sensitive information on over 16,000 workers may have been exposed in a ransomware attack on a Renton market research company’s data system.
Pacific Market Research (PMR) “recently notified” the Washington state Department of Labor and Industries, one of its clients, about the May 22 attack, according to a Thursday L&I news release.
An unauthorized party accessed PMR’s network and encrypted their servers during the attack, affecting an L&I file with sensitive information, according to the release.

[above via The Olympian post] Update 1
Ransomware Hits Arthur J. Gallagher (AJG)
2nd July 2021 | Target:** Arthur J. Gallagher (AJG) **| Reported Here
Arthur J. Gallagher (AJG), a US-based global insurance brokerage and risk management firm, is mailing breach notification letters to potentially impacted individuals following a ransomware attack that hit its systems in late September.
“Working with the cybersecurity and forensic specialists to determine what may have happened and what information may have been affected, we determined that an unknown party accessed or acquired data contained within certain segments of our network between June 3, 2020 and September 26, 2020,” AJG said.

[above via Bleeping Computer post] Update 1
REvil ransomware hits 200 companies in MSP supply-chain attack
2nd July 2021 | Target:** Kaseya **| Reported Here
In a statement late Friday evening, Kaseya CEO Fred Voccola confirmed that the company’s Incident Response team caught wind of the attack mid-day and immediately shut down their SaaS servers as a precautionary measure, despite not having received any reports of compromise from any SaaS or hosted customers.
“[We] immediately notified our on-premises customers via email, in-product notices, and phone to shut down their VSA servers to prevent them from being compromised. We then followed our established incident response process to determine the scope of the incident and the extent that our customers were affected,” Voccola said.

[above via Zdnet post] Update 1 / Update 2
Microsoft’s Halo dev site breached using dependency hijacking
29th June 2021 | Target:** Microsoft **| Reported Here
Microsoft has actually once more been efficiently struck by a dependency hijacking assault.
Previously, as initially reported by BleepingComputer, a scientist had morally hacked over 35 significant technology companies, consisting of Microsoft, by manipulating a weak point called “dependency confusion.”
This month, one more scientist discovered an npm interior dependency being made use of by an open-source task.

[above via Techtwiddle post] Update 1
Technisanct has disclosed serious data breach
25th June 2021 | Target:** Technisanc **| Reported Here
Kochi-based cybersecurity and big data startup, Technisanct, has disclosed ‘serious data breach’ in a trading platform in India. Information of over 3.4 million customers were compromised, according to a statement from the cybersecurity startup. Personal Identifiable Information (PII) which includes name, customer ID, contact number, email ID, trade login ID, branch ID, city and country were leaked. The security breach was identified by Technisanct’s digital risk monitoring tool ‘Integrite’.
The data of the customers has been kept for sale on a data-sharing platform for 8 of their credits. The information was published on June 15 and the incident was reported to CERT by Technisanct.

[above via The Week post] Update 1
Fleury hit by REvil ransomware attack
23rd June 2021 | Target:** Fleury Medical Diagnostics **| Reported Here
This week, Brazilian healthcare giant Grupo Fleury suffered a ransomware attack. Business operations were impaired up to the point that systems had to be shut down, leaving patients unable to book appointments for labs and other medical examinations online.
On the 22nd of June, the Grupo Fleury website began displaying a warning message, alerting to the fact that its systems were suffering an attack, but that the company was doing its best to remediate the damage. The message also stated that “the causes of this unavailability originated from the attempted external attack on [their] systems, which are having operations re-established with all the resources and technical efforts for the rapid standardization of services.”

[above via It Security Guru post] Update 1
Fertility clinic discloses data breach exposing patient info
20th June 2021 | Target:** Fertility Clinic **| Reported Here
A Georgia-based fertility clinic has disclosed a knowledge breach after recordsdata containing delicate affected person data have been stolen throughout a ransomware assault.
Reproductive Biology Associates, LLC, (RBA) is a fertility clinic that recruits egg donors, retrieves eggs, and shops them for later use by recipients, together with these utilizing the MyEggBank service.

[above via Technicalripon post]
Wegmans notifies customers of data breach
18th June 2021 | Target:** Wegmans **| Reported Here
Wegmans Food Markets were hit with a database breach that exposed customers’ information - name, address, email, birth date - but no social security numbers or financial information.
The Rochester, New York supermarket said in a press release that “a previously undiscovered configuration issue” led to two of its internal cloud databases being inadvertently left open to potential outside access. The company said it notified its customers that no financial information or social security numbers were involved since the company doesn’t collect or store that data.

[above via Pymnts post] Update1 / Update 2
Carnival Cruise hit by data breach, warns of data misuse risk
17th June 2021 | Target:** Carnival Cruise **| Reported Here
Carnival Corp. said Thursday that a data breach in March might have exposed personal information about customers and employees on Carnival Cruise Line, Holland America Line and Princess Cruises.
In a letter to customers, the company indicated that outsiders might have gained access to Social Security numbers, passport numbers, dates of birth, addresses and health information of people.

[above via USA Today post] Update1 / Update 2 / Update 3
Eggfree Cake Box suffer data breach exposing credit card numbers
17th June 2021 | Target:** Cake Box **| Reported Here
UK-based cake maker and retailer Cake Box Holdings Plc (CBOX.L) said on Thursday it had informed customers about a data breach in 2020 that might have compromised their personal information.
Shares of the company fell more than 8%. Cake Box said it had taken “appropriate steps to investigate the incident”.

[above via Reuters post] Update1 / Update 2
Gateley suffers data breach
16th June 2021 | Target:** Gateley **| Reported Here
Gateley, the UK-based legal and professional services group, has revealed that client data was accessed during a cyber-attack.
In a security alert published yesterday (June 16), the company said it took “some systems offline” after detecting unauthorized activity on its network.
It has since reestablished “core systems to enable us to continue to work and communicate with our clients, suppliers and intermediaries”.

[above via Portswigger post] Update1
IKEA Fined $1.2m for Spying on Employees
15th June 2021 | Target:** IKEA **| Reported Here
Swedish furnishing conglomerate IKEA has been fined €1m ($1.2m) for illegally spying on its employees in France and storing their data.
The fine was ordered by a French court on Tuesday after a criminal probe launched in 2012 found that IKEA France had created an elaborate “spying system” to snoop on staff and on customers who had opened disputes.
IKEA, which has 29 stores in France, was found guilty of “receiving personal data by fraudulent means.”

[above via InfoSecurity post] Update1 / Update 2
System failure hits Stillwater Medical
14th June 2021 | Target:** Stillwater Medical **| Reported Here
The Stillwater Medical Center hospital system is responding to a major computer outage that briefly shut down emergency room operations Monday morning.
Staff discovered the incident Sunday, June 13, according to spokesperson Shyla Eggers. Ambulances were diverted to other hospitals from about midnight to 7 a.m. on Monday, she said.

[above via News9 post] Update1 / Update 2
Audi, Volkswagen data breach affects 3.3 million customers
12th June 2021 | Target:** Audi, Volkswagen **| Reported Here
Audi and Volkswagen have suffered a data breach affecting 3.3 million customers after a vendor exposed unsecured data on the Internet.
Volkswagen Group of America, Inc. (VWGoA) is the North American subsidiary of the German Volkswagen Group. It is responsible for US and Canadian operations for Volkswagen, Audi, Bentley, Bugatti, Lamborghini, and VW Credit, Inc.

[above via Bleeping Computer post] Update1 / Update 2
Intuit notifies customers of hacked TurboTax accounts
12th June 2021 | Target:** Intuit – TurboTax **| Reported Here
Financial software company Intuit has notified TurboTax customers that attackers have accessed some of their personal and financial information after what appears to be a series of account takeover attacks.
In a breach notification letter sent to affected customers earlier this month, the company said it was not a “systemic Intuit data breach.”

[above via News Block post]
McDonald’s Hit by Data Breach
11th June 2021 | Target:** McDonald’s **| Reported Here
McDonald’s Corp. said hackers stole some data from its systems in markets including the U.S., South Korea and Taiwan, in another example of cybercriminals infiltrating high-profile global companies.
The burger chain said Friday that it recently hired external consultants to investigate unauthorized activity on an internal security system, prompted by a specific incident in which the unauthorized access was cut off a week after it was identified, McDonald’s said. The investigators discovered that company data had been breached in markets including the U.S., South Korea and Taiwan, the company said.

[above via WSJ post] Update 1 / Update 2 / Update 3
Foodservice supplier Edward Don hit by a ransomware attack
10th June 2021 | Target:** Edward Don **| Reported Here
Edward Don, a foodservice company, was hit by a suspected ransomware attack that encrypted its network. The attack caused the company to shut down some of its operations to prevent the malware’s spread.
Owned and operated by the Don family since 1921, Edward Don and Company are one of the largest foodservice equipment and supplies distributors in the US. It sells such equipment as kitchen supplies, bar supplies, dinnerware, and flatware.

[above via Cyber Intel Mag post] Update 1
CD Projekt: Data stolen in ransomware attack now circulating online
10th June 2021 | Target:** CD Projekt **| Reported Here
The CD Projekt Group, which owns Cyberpunk and Witcher developer CD Projekt Red, has warned that sensitive data - including that of its own employees - was likely exposed during a security breach earlier this year.
In a statement, the Polish developer said it has discovered new information about the breach, and now has reason to believe that some illegally gathered data is “currently being circulated on the internet.”

[above via Games Industry post] Update 1
Hackers breach gaming giant Electronic Arts, steal game source code
10th June 2021 | Target:** Electronic Arts **| Reported Here
Hackers have broken into gaming giant Electronic Arts, the publisher of Battlefield, FIFA, and The Sims, and stole a wealth of game source code and related internal tools, Motherboard has learned.

[above via Vice post] Update 1
ADATA hit by Ragnar Locker ransomware
8th June 2021 | Target:** ADATA **| Reported Here
Leading Taiwan-based memory and storage manufacturer ADATA says a ransomware attack forced it to shut down systems after attacking its network in late May.
ADATA manufactures high-performance DRAM memory modules, NAND Flash memory cards, and other products, including mobile accessories, gaming products, electrical powertrains, and industrial solutions.
The company was ranked as the second largest manufacturer of DRAM memory and solid state drives (SSD). in 2018.

[above via News-block post] Update 1 / Update 2
Navistar discloses data breach
7th June 2021 | Target:** ADATA **| Reported Here
US truck and military vehicle manufacturer Navistar International Corp said on Monday that the company was targeted by a cyberattack.
In an 8-K US Securities and Exchange Commission filing published on Monday, Navistar said it became aware of a potential data breach last month, saying it received a claim that data had been stolen from its IT system. It’s unclear exactly what data was taken.

[above via Business Insider post] Update 1 / Update 2
Fujifilm Shuts Down Network After Suspected Ransomware Attack
3rd June 2021 | Target:** Fujifilm **| Reported Here
Japanese multinational conglomerate Fujifilm has been forced to shut down parts of its global network after falling victim to a suspected ransomware attack.
The company, which is best known for its digital imaging products but also produces high-tech medical kit, including devices for rapid processing of COVID-19 tests, confirmed that its Tokyo headquarters was hit by a cyberattack on Tuesday evening.

[above via Techcrunch post] Update 1 / Update 2
The M.T.A. Is Breached by Hackers as Cyberattacks Surge
2nd June 2021 | Target:** Metropolitan Transportation Authority **| Reported Here
The Metropolitan Transportation Authority, which operates New York City’s subway and bus systems, confirmed to Fox News on Wednesday that at least three of its 18 systems were hacked in April.
The MTA is critical infrastructure in a city that serves as a national and world financial center, among other roles New York plays in the economy.

[above via Fox Business post] Update 1 / Update 2
Spain’s Ministry of Labor and Social Economy hit by cyberattack
1st June 2021 | Target:** Spanish Ministry of Labor and Social Economy **| Reported Here
The Ministry of Labor and Social Economy has suffered a new cyber attack. Just three months after the one suffered by the State Public Employment Service (SEPE), dependent on Labor. Through a brief message on Twitter, the Ministry of Labor has reported that it is being affected by a computer attack.

[above via Explica post] Update 1 / Update 2
Swedish Health Agency shuts down SmiNet after hacking attempts
31st May 2021 | Target:** Swedish Health Agency **| Reported Here
The Swedish Public Health Agency shut down SmiNet, the country’s infectious disease database, on Thursday after it was the target of several hacking attempts.
SmiNet, which is also used to store electronic reports with statistics on COVID-19 infections, was closed on Thursday to investigate the attacks and came back online Friday night.

[above via News Block post]
JBS Foods shuts down production after cyberattack
31st May 2021 | Target:** JBS Food **| Reported Here
Meat processor JBS has warned it could take the company some time to recover from an “organised cyber security attack” that has impacted servers in its Australian and North American operations.
The attack was first reported by industry news website Beefcentral, which quoted JBS Australia CEO Brent Eastwood saying that the full impact of the attack was still being assessed.

[above via Itnews post] Update 1
Beware: Walmart phishing attack says your package was not delivered
29th May 2021 | Target:** Walmart **| Reported Here
An ongoing domain name spoofing campaign is taking aim at retail giant Walmart and other big fish, with more than 540 malicious domains being used to harvest consumer information.
The scam domains are mimicking legitimate sites in name and appearance, in hopes of fooling visitors into entering their personal details, according to analysis from DomainTools. Aside from Walmart, other big-name lures are affiliated with the phishing campaign, spoofing Fortune 500 companies like McDonald’s, online dating sites and movie downloads. An unknown threat actor is behind it all, the firm said, displaying an obvious level of sophistication given the sheer scale of the effort.

[above via Threatpost post] Update 1
Canada Post hit by data breach after supplier ransomware attack
27th May 2021 | Target:** Canada Post **| Reported Here
Canada Post said on Wednesday that a cyberattack and data breach on an electronic data interchange (EDI) supplier has compromised information from 44 of its large parcel business customers, affecting nearly 1 million recipients.
The attack on Ontario-based Commport Communications compromised the shipping manifest data of the customers. Canada Post, Canada’s government-run postal carrier, did not identify the customers.

[above via Freightwaves post] Update 1 / Update 2 / Update 3
Domino’s India discloses data breach after hackers sell data online
25th May 2021 | Target:** Domino’s India **| Reported Here
Domino’s India brand owner Jubilant Foodworks has informed its customers about the data breach incident that took place on March 24 and leaked its customer data, including their personal details such as mailing addresses and mobile numbers, among others. The latest development comes just days after hackers created a search engine on the dark Web to let anyone look at the customer details of Domino’s India by using their phone numbers or email addresses. The company initially confirmed its data breach to the media in April.

[above via Gadgets post] Update 1 / Update 2
Audio maker Bose discloses data breach after ransomware attack
24th May 2021 | Target:** Bose **| Reported Here
Audio experts Bose suffered a ransomware attack earlier this year in March, according to an incident notification letter sent to New Hampshire’s Office of the Attorney General, by a counsel on behalf of the company.
In the letter, accessed and shared by BleepingComputer, the counsel notes that during investigation of the cyber-incident, the company discovered that data related to six former employees was “accessed and potentially exfiltrated.”
Although the letter doesn’t mention the ransomware that was deployed, or the ransom demanded, it does refer to the incident as a sophisticated attack.

[above via Techradar post] Update 1 / Update 2
Air India cyber-attack: Data of millions of customers compromised
22nd May 2021 | Target:** Air India **| Reported Here
Air India disclosed a data breach after personal information belonging to roughly 4.5 million of its customers was leaked two months following the hack of Passenger Service System provider SITA in February 2021.
The Indian national carrier first informed passengers that SITA was the victim of a cyberattack on March 19.

[above via Bleeping Computer post] Update 1 / Update 2
Amex fined £90,000 for sending 4 million spam emails in a year
23rd May 2021 | Target:** American Express (Amex) **| Reported Here
American Express Services Europe has been fined £90,000 ($127,377) by a U.K. regulator, which found the company illegally blasted out 4 million marketing emails to customers who had opted out of receiving them.
Critics said the fine, which is nominal for the multi-national financial brand, isn’t likely to do much to deter Amex, or any other company, from engaging in the practice

[above via Threatpost post] Update 1 / Update 2
Man pleads guilty to stealing UPMC employee data, selling it on dark web
20th May 2021 | Target:** UPMC **| Reported Here
Justin Sean Johnson, a 30-year-old from Detroit, Michigan, has pleaded guilty to stealing the personally identifiable information (PII) of 65,000 employees of health care provider and insurer University of Pittsburgh Medical Center (UPMC) and selling it on the dark web.
UPMC is Pennsylvania’s largest health care provider that employs more than 90,000 employees in 40 hospitals and 700 doctors’ offices and outpatient sites.

[above via Bleeping Computer post] Update 1
70 Banks Targeted By Bizarro Banking malware
19th May 2021 | Target:** Multiple Banks **| Reported Here
Internet banking has made our lives simpler, but sometimes we become soft targets of the hackers who are on the lookout for vulnerable users. The cybercriminals send malware through SMSes that look authentic and then gain illegal access to your private information. One such trojan called Bizarro Banking Trojan has been found and that is stealing financial information and crypto wallets of users.

[above via India-Today post] Update 1
Guard.me suffers a data breach
17th May 2021 | Target:** Guard.me **| Reported Here
Student health insurance company guard.me has taken its website offline after a vulnerability allowed a threat actor to access policyholders’ personal information.
guard.me is one of the largest insurance companies in the world that specializes in providing medical insurance to students while traveling or studying in another country.
On May 12, Guard.me discovered suspicious activity on their website that led them to remove their website. When visiting the website, visitors are automatically redirected to a maintenance page that warns that the site is down while the insurance provider increases security on the site.

[above via News-Block post] Update 1
Insurer AXA hit by ransomware
16th May 2021 | Target:** Axa Insurance **| Reported Here
A subsidiary of French insurance giant Axa has been hit by a ransomware attack affecting operations in several Asian countries, the company said on Sunday (May 16), confirming a Financial Times report.
“Asia Assistance was recently the victim of a targeted ransomware attack which impacted its IT operations in Thailand, Malaysia, Hong Kong, and the Philippines,” Axa Partners said in a statement.

[above via Channel News Asia post] Update 1
Irish healthcare shuts down IT systems after Conti ransomware attack
14th May 2021 | Target:** Health and Safety Executive **| Reported Here
Ireland’s public healthcare system said it shut down major technology systems Friday after a ransomware attack, causing disruption at hospitals and Covid-19 testing centers.
Paul Reid, director-general of the Health Service Executive, told Irish radio Friday the attack was sophisticated and used ransomware known as Conti. He said Ireland’s Covid-19 vaccination services will continue normally because they use different technology than the country’s other healthcare operations.

Chemical distributor pays $4.4 million to DarkSide ransomware
13th May 2021 | Target:** Brenntag **| Reported Here
Colonial Pipeline, which suffered a crippling ransomware attack on its infrastructure on May 7, 2021, just recently announced that it has recovered quickly from the attack just a week ago and expects all its infrastructure to be fully operational soon.

[above via neowin post]
City of Tulsa’s online services disrupted in ransomware incident
10th May 2021 | Target:** Tulsa, Oklahoma **| Reported Here
The City of Tulsa is having to relearn how to do their jobs without computers.
“We have shut out computer systems at the city down to prevent any spread of that malware on our networks,” said Tulsa Mayor GT Bynum.
The city today announcing this piece of ransomware got into the system on April 21.

[above via Ktul post] Update 1
Ransomware gangs have leaked the stolen data of 2,100 companies so far
8th May 2021 | Target:** Multiple Individuals and Businesses **| Reported Here
Since 2019, ransomware gangs have leaked stolen data from 2,103 companies on dark web data breach sites.
When modern ransomware operations began in 2013, the attacker’s goal was to encrypt as many companies as possible and then demand a ransom for a decryptor.
From the beginning of 2020, ransomware operations began to carry out a new tactic called double extortion.

[above via News Block post]
Cyberattack Forces a Shutdown of a Top U.S. Pipeline
8th May 2021 | Target:** Colonial Pipeline **| Reported Here
Colonial Pipeline, the largest fuel pipeline in the United States, has shut down operations after suffering what is reported to be a ransomware attack.
Colonial Pipeline transports refined petroleum products between refineries located in the Gulf Coast and markets throughout the southern and eastern United States. The company transports 2.5 million barrels per day through its 5,500 mile pipeline and provides 45% of all fuel consumed on the East Coast.

[above via Bleeping Computer post] Update 1 / Update 2
Codecov starts notifying customers affected by supply-chain attack
30th April 2021 | Target:** Codecov **| Reported Here
A few hours ago, Codecov started notifying the maintainers of the software repositories affected by the recent attack on the supply chain.
These notifications, delivered both via email and via the Codecov application interface, state that the company believes that the affected repositories were downloaded by threat agents.
The original security advisory published by Codecov lacked indicators of compromise (IOC) due to a pending investigation.

[above via News Block post] Update 1
Brazil’s Rio Grande do Sul court system hit by REvil ransomware
29th April 2021 | Target:** Brazilian judicial **| Reported Here
The Court of Justice of the State of Rio Grande do Sul in Brazil received a REvil ransomware attack yesterday that encrypted employee files and forced the courts to shut down their network.
Tribunal de Justiça do Estado do Rio Grande do Sul (TJRS) is the judicial system of the Brazilian state of Rio Grande do Sul.

[above via News Block post] Update 1
DigitalOcean data breach exposes customer billing information
28th April 2021 | Target:** Digital Ocean **| Reported Here
DigitalOcean has emailed customers warning of a data breach involving customers’ billing data, TechCrunch has learned.
The cloud infrastructure giant told customers in an email on Wednesday, obtained by TechCrunch, that it has “confirmed an unauthorized exposure of details associated with the billing profile on your DigitalOcean account.” The company said the person “gained access to some of your billing account details through a flaw that has been fixed” over a two-week window between April 9 and April 22.

[above via Techcurnch post] Update 1 / Update 2
Reverb discloses data breach exposing musicians’ personal info
26th April 2021 | Target:** Reverb **| Reported Here
Reverb, a popular online marketplace for musical instruments, has suffered a data breach incident and is now notifying its users. According to it, a database containing the PII of its customers was leaked online for a while and secured immediately after realizing it. Reverb suggested customers’ change their passwords for good, as they regularly do for no reason mentioned how this had happened.

[above via The Hack Post post] Update 1 / Update 2
DC Police confirms cyberattack after ransomware gang leaks data
26th April 2021 | Target:** D.C. police department **| Reported Here
Files belonging to the Washington, D.C., Metropolitan Police Department appeared Monday on a leak site affiliated with a relatively new form of ransomware.
In images posted to their site, actors associated with the Babuk malware, which was first identified earlier this year, claimed to have stolen upward of 250 gigabytes of data from D.C. police, including police reports, arrest records, internal memos and documents shared with other authorities, like the FBI.

[above via The Hack Post post] Update 1 / Update 2
Hacker leaks 20 million alleged BigBasket user records for free
25th April 2021 | Target:** BigBasket **| Reported Here
A database of about 20 million alleged BigBasket users has leaked on a well-known cybercrime forum, months after the Indian grocery delivery startup confirmed it had faced a data breach.
The database includes users’ email address, phone number, address, scrambled password, date of birth, and scores of interactions they had with the service. TechCrunch confirmed details of some customers listed in the database - including those of the author.

[above via Techcrunch post] Update 1 / Update 2
A ransomware gang made $260,000 in 5 days using the 7zip utility
24th April 2021 | Target:** QNAP NAS **| Reported Here
A ransomware gang has made $260,000 in just five days simply by remotely encrypting files on QNAP devices using the 7zip archive program.
Starting on Monday, QNAP NAS users from all over the world suddenly found their files encrypted after a ransomware operation called Qlocker exploited vulnerabilities on their devices.

[above via Bleeping Computer post] Update 1
Apple Targeted in $50 Million Ransomware Hack of Supplier Quanta
21st April 2021 | Target:** Apple **| Reported Here
Ransomware group REvil claimed in a blog post published on Tuesday to have stolen blueprints for Apple’s latest products. On the same day, Apple CEO Tim Cook announced multiple new products at an online event.
Quanta Computer Inc. acknowledged the attack in a statement made to Bloomberg, stating that the company’s information security team worked with external experts to deal with cyber attacks on a small number of servers. The company also told Bloomberg that there has been no material impact on business operations.

[above via Techrepublic post] Update 1
Eversource Energy data breach caused by unsecured cloud storage
20th April 2021 | Target:** Eversource Energy **| Reported Here
Eversource Energy suffers a data breach after customer sensitive data was disclosed on an unsecured cloud server.
Eversource Energy, a publicly traded, fortune 500 energy delivery company in New England, powering 4.3 million electric and natural gas customers throughout Connecticut, Massachusetts, and New Hampshire.

[above via Securereading post] Update 1
Geico data breach exposed customers’ driver’s license numbers
19th April 2021 | Target:** GEICO Insurance company **| Reported Here
Car insurance provider Geico has suffered a data breach where threat actors stole the driver’s licenses for policyholders for over a month.
Geico is the second-largest car insurance company in the United States, with over 17 million policies for more than 28 million vehicles.

[above via Bleeping Computer post] Update 1 / Update 2
HackBoss malware poses as hacker tools on Telegram to steal digital coins
16th April 2021 | Target:** Various Hacking Groups **| Reported Here
Hackers are distributing cryptocurrency-stealing malware over a Telegram channel to would-be hackers in a scam that has racked up $500,000, according to security researchers.
According to cyber security firm Avast, Hackers are running a Telegram channel called “Hack Boss” to distribute malicious software for other hackers to use. Unfortunately for the hackers who download it, the software won’t help them spread malware. Instead, it’ll infect their systems with cryptocurrency-stealing malware.

[above via Itpro post]
Celsius email system breach leads to phishing attack on customers
15th April 2021 | Target:** Celsius Network **| Reported Here
Crypto lending service Celsius has discovered a data breach with one of its third-party service providers has exposed the personal information of its customers, an email sent to Celsius customers and shared with CoinDesk confirms.
Hackers gained access to a “third-party email distribution system” Celsius uses, according to the email. The hackers have used this information to send fraudulent emails and text messages to Celsius to trick them into revealing the private keys to their funds.

[above via Coindesk post] Update 1
Gay dating site Manhunt hacked, thousands of accounts stolen
14th April 2021 | Target:** Manhunt **| Reported Here
Gay dating app Manhunt has revealed that it was hacked in February, exposing the data of thousands of users.
In a statement to the Washington state attorney general’s office, Manhunt said a hacker had “gained access to a database that stored account credentials for Manhunt users.”

[above via Metroweekly post] Update 1
Cyber-Attack Shutters Half of Tasmania’s Casinos
13th April 2021 | Target:** Tasmania’s Casinos **| Reported Here
Poker machines at Tasmania’s two casinos have been offline since the Easter weekend due to a ransomware cyber-attack.
Owner Federal Group was forced to shut down gaming machines at Hobart’s Wrest Point and the Country Club in Launceston following an “incident” in the early hours of 3 April.

[above via TheGuardian post] Update 1 / Update 2
Iran Nuclear Facility Suffers Cyber-Attack
11th April 2021 | Target:** Natanz Nuclear Site **| Reported Here
Israel appeared to confirm claims that it was behind a cyber-attack on Iran’s main nuclear facility on Sunday, which Tehran’s nuclear energy chief described as an act of terrorism that warranted a response against its perpetrators.
The apparent attack took place hours after officials at the Natanz reactor restarted spinning advanced centrifuges that could speed up the production of enriched uranium, in what had been billed as a pivotal moment in the country’s nuclear programme.

[above via TheGuardian post] Update 1
Upstox Alerts Users of Data Breach; Says Funds, Securities Remain Safe
11th April 2021 | Target:** Upstox **| Reported Here
Upstox has alerted customers of a security breach that included contact data and KYC details of customers. The retail broking firm assured users that their funds and securities remain safe.

[above via Gadgets NDTV post] Update 1
Over 600,000 stolen credit cards leaked after Swarmshop hack
8th April 2021 | Target:** Swarmshop **| Reported Here
A breach of Swarmshop, an online hub for selling stolen personal and payment records, has led to the exposure of more than 600,000 payment card numbers and nearly 70,000 sets of US Social Security numbers and Canadian Social Insurance numbers, Group-IB researchers report.

[above via Dark Reading post] Update 1 / Update 2
Carding Mafia hacked
7th April 2021 | Target:** Carding Mafia **| Reported Here
Have I been Pwned reported that the data breach exposed users’ email addresses, hashed passwords, usernames, and IP addresses. Of the 500,000 users of the hacking forum, 297,744 have been affected; however, the forum operators have not yet notified their users. The founder of Have I Been Pwned has confirmed the authenticity of the stolen data. Troy Hunt stated that the carding site recognised the leaked email addresses through the “forgot password” feature. It failed, though, when random email addresses were entered.

[above via Itsecurityguru post] Update 1
European Commission, other EU orgs recently hit by cyber-attack
6th April 2021 | Target:** The European Commission and European Union organizations **| Reported Here
The European Commission (EC) and other EU institutions have been hit by a cyber attack.
An EC spokesperson told IT Pro that an “IT security incident” had affected a number of EU institutions, bodies, and agencies’ IT infrastructure.
Forensic analysis is still in its “initial phase” and at this stage, it is too early to provide any “conclusive information”.

[above via The Hack Post post] Update 1
Michigan State Title IX case files leaked in consulting data breach
6th April 2021 | Target:** Michigan State Title IX | Bricker & Eckler LLP **| Reported Here
Michigan State University (MSU) has been impacted by a data breach stemming from a cyber-attack on an Ohio law firm.
Bricker & Eckler LLP, which is associated with MSU Title IX contractor INCompliance Consulting, was hit with ransomware in January 2021.

[above via Infosecurity post] Update 1
Ransomware hits TU Dublin and National College of Ireland
6th April 2021 | Target:** The National College of Ireland (NCI) and the Technological University of Dublin **| Reported Here
The National College of Ireland (NCI) and the Technological University of Dublin have introduced that ransomware assaults hit their IT programs.
NCI is at the moment engaged on restoring IT companies after being hit by a ransomware assault over the weekend that pressured the school to take IT programs offline.

[above via The Hack Post post]
LinkedIn Spear-Phishing Campaign Targets Job Hunters
5th April 2021 | Target:** LinkedIn User **| Reported Here
Security researchers are warning LinkedIn users to beware of unsolicited job offers after revealing a new spear-phishing campaign designed to install Trojan malware on their devices.
The eSentire Threat Response Unit (TRU) yesterday claimed that individuals were being targeted with customized files named the same as their own current role.

[above via Infosecurity post]
Brown University hit by cyberattack
2nd April 2021 | Target:** Brown University **| Reported Here
Brown University was hit by a cyberattack that has forced the school to disable systems and cut off connections to the data centre.
Brown University is a private US research university and is the seventh-oldest institution of higher education in the United States.
The university’s Computing & Information Services staff took “a number of aggressive steps to protect the University’s digital resources, including shutting down connections to our central data centre and systems within it.”

[above via Securereading post]
Harris Federation hit by ransomware attack affecting 50 schools
29th March 2021 | Target:** Harris Federation **| Reported Here
A ransomware attack has infected IT systems at schools across London, leaving tens of thousands of pupils without access to email or school-issued devices.
The Harris Federation, which runs 50 primary and secondary schools in London and Essex, fell victim to a ransomware attack on Saturday 27th March – just days after the National Cyber Security Centre (NCSC) put out an alert warning schools, colleges and universities about the “growing threat” of cyber criminals targeting education with ransomware.

[above via Zdnet post] Update 1
Top insurer CNA hit by new Phoenix CryptoLocker ransomware
25th March 2021 | Target:** CNA **| Reported Here
Insurance giant CNA has suffered a ransomware assault utilizing a new variant referred to as Phoenix CryptoLocker that’s presumably linked to the Evil Corp hacking group.
This week, BleepingComputer reported that CNA had suffered a cyberattack impacting their on-line providers and business operations.

[above via The Hack Post post] Update 1
MangaDex manga site temporarily shut down after cyberattack
22nd March 2021 | Target:** MangaDex **| Reported Here
Manga scanlation big MangaDex has been temporarily shut down after struggling a cyberattack and having its supply code stolen.
MangaDex is without doubt one of the largest manga scanlation (scanned translations) websites the place guests can learn manga comics on-line without spending a dime. According to SimilarWeb, MangaDex is the 179th most steadily visited site on the internet, with over 76 million guests per thirty days.

[above via The Hack Post post] Update 1
Acer hit by $50 million ransomware attack
19th March 2021 | Target:** Acer **| Reported Here
A hacker group has demanded $50 million in ransom from Taiwanese PC maker Acer, according to Bleeping Computer. Attackers reportedly gained access to Acer’s network by exploiting a Microsoft Exchange vulnerability.
The hacker group has given Acer time until March 28 to pay the ransom else it will publish the data it claims to have accessed.

[above via Tech HindustanTimes post] Update 1 / Update 2
Superstar K-Pop Band’s TikTok Hacked
10th March 2021 | Target:** (BTS) **| Reported Here
South-Korean boy band BTS’ TikTok account with nearly 29.8 million followers was reportedly hacked. Apparently, the account featured a video titled “soon” and showed a hammer with background music akin to horror movies.

[above via Free Press Journal post] Update 1
Flagstar Bank hit by data breach exposing customer, employee data
8th March 2021 | Target:** Flagstar Bank**| Reported Here
Flagstar Bank has been added to a list of companies breached due to an Accellion software zero-day vulnerability.
The bank, headquartered in Michigan, is a Flagstar Bancorp, subsidiary and provides mortgages and other financial services to US customers.
In a statement posted on Flagstar Bank’s website, the organization says that Accellion first informed the company of a security issue on January 22, 2021.

[above via Zdnet post] Update 1
SITA data breach affects millions of travelers from major airlines
5th March 2021 | Target:** SITA **| Reported Here
The global information technology company SITA has suffered a data breach after hackers were able to gain access to its servers which contain passenger data from multiple airlines around the world.

[above via Techradar post] Update 1 / Update 2
Cryptocurrency Fraudster Steals $16m
4th March 2021 | Target:** Multiple Individuals and Businesses **| Reported Here
A Swedish hotelier accused of using the proceeds of a $16 million investment scam to buy a resort in Thailand pled gulity wednesday to running the scheme and laundering money through various platforms, inculding popular cyrptocurrency exchange Coinbase

[above via Law360 post] Update 1
CompuCom MSP hit by DarkSide ransomware
4th March 2021 | Target:** CompuCom MSP **| Reported Here
US managed service provider CompuCom has suffered a DarkSide ransomware attack leading to service outages and customers disconnecting from the MSP’s network to prevent the spread of malware.
CompuCom is an IT managed services provider (MSP) that provides remote support, hardware and software repair, and other technology services to companies. CompuCom is a wholly-owned subsidiary of The ODP Corporation (Office Depot/Office Max) and employs approximately 8,000 people.

[above via Bleeping Computer post] Update 1
Oxfam Australia confirms data breach after stolen info sold online
2nd March 2021 | Target:** Oxfam **| Reported Here
Oxfam Australia has confirmed a data breach after a database belonging to the organization was leaked on an underground forum.
After being made aware of a suspected security incident by Bleeping Computer, the charity’s Australian arm has now confirmed that supporters of the charity have been impacted.

[above via Zdnet post] Update 1
Universal Health Services lost $67 million due to Ryuk ransomware attack
1st March 2021 | Target:** Universal Health Services (UHS) **| Reported Here
A ransomware attack last fall cost Universal Health Services $67 million in pre-tax losses, the healthcare provider confirmed in an earnings report released today.

[above via Dark Reading post] Update 1
Twitter scammers earned over $145k this week in Bitcoin
26th February 2021 | Target:** Twitter accounts **| Reported Here
If the technology these days have reached new heights, so has the ways of committing new crimes and deceiving people. Twitter has reported to have had scammers that earned around $145 recently by scamming people and tricking them into fake giveaways by hacking into high end company accounts and making it seem like they hosted them. This news first came out in the open through a site called Bleeping Computers that provides free computer help through its platform and covers such news that is related to technology.

[above via Digital Information World post]
T-Mobile discloses data breach after SIM swapping attacks
26th February 2021 | Target:** T-Mobile **| Reported Here
T-Mobile, the U.S. telco giant, has seen a steep rise in SIM swap attacks against its customers, and as confirmed through a notice of data breach, this was because of a security incident. The company alleges that they identified the malicious activity fairly quickly and took action to terminate it as well as prevent it from reoccurring in the future.

[above via Technadu post]
Dutch Research Council (NWO) confirms ransomware attack
25th February 2021 | Target:** Dutch Research Council (NWO) **| Reported Here
Hackers published a batch of internal documents from the Netherlands Organisation for Scientific Research (NWO) on the dark web yesterday, after the agency refused to pay up in a ransomware attack. The attack, which began on 8 February, has completely knocked out the agency’s grant application and review process and cut off NWO’s communication with applicants, grantees, and universities.

[above via Science Mag post] Update 1
Silicon Valley’s most notable VC firms, told investors it was hacked
22nd February 2021 | Target:** Silicon Valley **| Reported Here
A leading venture capital firm based in California’s Silicon Valley has fallen victim to a cyber-attack.
According to Axios, Sequoia Capital contacted investors on Friday, February 19, to inform them that their financial data and personal information had been accessed by an unauthorized third party. The data breach occurred after the email account belonging to an employee at the firm was compromised in a phishing attack.
[above via Infosecurity post]
Kroger data breach exposes pharmacy and employee data
20th February 2021 | Target:** Kroger **| Reported Here
Kroger was among the companies affected by a data breach caused by a weakness in a product offered by Accellion, a third-party company that the retailer used for secure file transfer services, according to a company press release.
The breach didn’t affect Kroger’s IT system, the store systems, debit or credit card information, and no customer data was misused, the retailer said, but it did impact certain HR data, money service records, and pharmacy records.

[above via Business Insider post] Update 1
Underwriters Laboratories (UL) certification giant hit by ransomware
19th February 2021 | Target:** Underwriters Laboratories (UL) **| Reported Here
UL, which you may know better as Underwriters Laboratories, has overcome countless obstacles in its 127-year run as the world’s leading safety testing authority. Now they’re facing down a true 21st century menace: ransomware.

[above via Forbes post] Update 1
Lakehead University under cyber attack
16th February 2021 | Target:** Lakehead University **| Reported Here
Students at Lakehead University are getting an extended winter study break following a cyber attack.
Classes were scheduled to resume Monday, but that has been pushed by four days to Friday. Students had expressed concern about not being able to access campus computers and systems with mid-term exams approaching.

[above via Ctv News post] Update 1
EXMO suffers DDoS attack
ransom
15th February 2021 | Target:** EXMO **| Reported Here
Cryptocurrency exchange EXMO has been knocked offline by a “massive” DDoS attack, the UK-based company has confirmed.
The exchange said it suffered a distributed denial-of-service (DDoS) assault yesterday (February 15), when its website was unavailable for two hours.
EXMO said that it experienced an unusual amount of traffic at 16.10 GMT, with the number of connections temporarily disrupting its activity.

[above via Portswigger post]
Kia Motors America suffers ransomware attack, $20 million ransom
17th February 2021 | Target:** Kia Motors America **| Reported Here
Kia Motors America has allegedly suffered a ransomware attack by the DoppelPaymer gang, demanding $20 million for a decryptor and not to leak stolen data, according to news reports.
A day before, BleepingComputer reported that Kia Motors America was suffering a nationwide IT outage, which affected their servers, self-payment services, dealer platforms, and phone support system. Kia employees told BleepingComputer this was a nationwide outage that started Saturday, February 23.

[above via Security Magazine post] Update 1 / Update 2
French MNH health insurance company hit by RansomExx ransomware
10th February 2021 | Target:** Mutuelle Nationale des Hospitaliers **| Reported Here
Mutuelle Nationale des Hospitaliers (MNH), an insurance company in France that caters to all public and private health professionals, was recently forced to suspend operations after a ransomware attack targeted its IT systems.

[above via Teiss post] Update 1
USCellular hit by a data breach after hackers access CRM software
29th January 2021 | Target:** United States Cellular Corporation **| Reported Here
U.S. Cellular, the fourth-largest wireless carrier in America, has suffered a data breach. Hackers reportedly gained access to protected systems by installing malware on a computer at a U.S. Cellular retail store.
According to the breach notification filed with the Office of the Vermont Attorney General the attack began on the 4th of January. Hackers targeted a handful of U.S. Cellular store employees who had access to its customer relationship management (or CRM) software.

[above via Forber post] Update 1
Cops Disrupt Emotet, the Internet’s ‘Most Dangerous Malware’
27th January 2021 | Target:** Dairy Farm **| Reported Here
Police have seized thousands of computers running one of the most dangerous hacking networks worldwide.
The Emotet network obtains access to victims’ computers, via malicious email attachments, then sells it to criminals who install more dangerous malware.
Police from the UK, EU, US and Canada worked together to “disrupt” Emotet.

[above via BBC post] Update 1 / Update 2
Pan-Asian retail giant Dairy Farm suffers REvil ransomware attack
26th January 2021 | Target:** Dairy Farm **| Reported Here
Around January 14th, 2021, the retail giant Dairy Farm was attacked by the REvil ransomware operation. The attackers demanded a $30 million ransom. The ransomware group compromised Dairy Farm’s network and encrypted devices. Allegedly the attackers had access to information up until 7 days after the attack.

[above via Itsecurityguru post]
Bonobos clothing store suffers a data breach
22nd January 2021 | Target:** Bonobos clothing store **| Reported Here
Men’s clothing store Bonobos has suffered a massive data breach exposing millions of customers’ personal information.
Walmart bought Bonobos in 2017 for $300 million to offer its clothing on Jet.com. BleepingComputer reported the breach occurred after a cloud backup of their database was downloaded by a threat actor.

[above via Ris news post] Update 1
Kentucky Senior Arrested for Identity Theft
20th January 2021 | Target:** Multiple Individuals and Businesses **| Reported Here
Two women in Kentucky have been arrested in connection with a year-long cybercrime operation involving stolen identities and fraudulent benefit claims.
An investigation was launched by police in West Buechel at the beginning of January when they received a call from a local branch of the bank BB&T to say that a fraudulently authorized check for nearly $40,000 had just been cashed.

[above via Bleeping Computer post] Update 1
CHwapi Hospital Suffers a Ransomware Attack
20th January 2021 | Target:** CHwapi Hospital **| Reported Here
The CHwapi hospital in Belgium is suffering from a cyberattack where threat actors claim to have encrypted 40 servers and 100 TB of data using Windows Bitlocker.
On Sunday, CHwapi suffered an attack that caused the hospital to redirect patients to other hospitals and delay surgical procedures.

[above via Gadgetpage post]
JPMorgan Chase Hacker Gets 12 Years
7th January 2021 | Target:** JPMorgan **| Reported Here
A Russian hacker who was instrumental in one of the largest thefts in history of US customer data from a single financial institution has been sentenced to prison.
Moscow resident Andrei Tyurin, also known as Andrei Tiurin, was part of an international hacking campaign that compromised the computer systems of major financial institutions, brokerage firms, news agencies, and other companies to steal data.

[above via Infosecurity post] Update 1 / Update 2 /
China’s APT hackers move to ransomware attacks
4th January 2021 | Target:** Multiple Firms Businesses **| Reported Here
A well-known Chinese state-backed APT group is believed to have been responsible for multiple ransomware attacks against firms last year, according to new research.
A report from Security Joes and Pro reveals how the vendors uncovered the links after investigating an incident in which ransomware encrypted “several core servers” at an unidentified victim organization.

[above via Infosecurity post]
SolarWinds hackers breach US nuclear weapons agency
17th December 2020 | Target:** Nisa **| Reported Here
The Energy Department and National Nuclear Security Administration, which maintains the U.S. nuclear weapons stockpile, have evidence that hackers accessed their networks as part of an extensive espionage operation that has affected at least half a dozen federal agencies, officials directly familiar with the matter said.
On Thursday, DOE and NNSA officials began coordinating notifications about the breach to their congressional oversight bodies after being briefed by Rocky Campione, the chief information officer at DOE.

[above via Politico post] update 1
Ransomware attack causing billing delays for Missouri city
15th December 2020 | Target:** Missouri **| Reported Here
The City of Independence, Missouri, suffered a ransomware attack last week that continues to disrupt the city’s services.
At the beginning of the month, Independence suffered a ransomware attack that forced them to shut down their IT system as they recovered from the attack.

[above via Bleeping Computer post]
Intel’s Habana Labs hacked by Pay2Key ransomware, data stolen
13th December 2020 | Target:** Intel’s Habana **| Reported Here
As reported by Calcalist, a hacking group alleges that it has used Pay2key malware to gain access to Intel’s Habana Labs in Israel. The purported attack follows a wave of recent ransomware attacks in Israel. As proof of the attack, the hackers have shared via Twitter what appears to be a snippet of Habana Labs code, although it’s notable that the snippet of text could be easily faked, along with a domain account and domain zone information. We’ve reached out to Intel for further comment and will update as necessary.

[above via Tomshardware post] Update 1 / Update 2
Foxconn electronics giant hit by ransomware, $34 million ransom
7th December 2020 | Target:** Foxconn **| Reported Here
A ransomware attack on Taiwanese electronics giant Foxconn has resulted in hackers demanding $34.7 million in Bitcoin.
Cybercriminals infiltrated Foxconn’s networks on November 29, stealing and encrypting files and deleting data from servers at the company’s Mexican facility, Bleeping Computer reported.
The attack was reportedly carried out by ransomware gang DoppelPaymer, which is demanding $34.7 million in cryptocurrency for the return of files.

[above via Portswigger post] Update 1 / Update 2
Ransomware Incident Impacts Greater Baltimore Medical Center Computer Systems
7th December 2020 | Target:** Greater Baltimore Medical Center **| Reported Here
The Greater Baltimore Medical Center on Sunday became the latest U.S. hospital to grapple with a ransomware incident amid a raging pandemic that has stretched health care IT resources thin.
The ransomware attack caused “many of our [IT] systems” to go down, the 342-bed medical center said in a statement late Sunday. That means some patient procedures scheduled for Monday “may be affected,” GBMC said. The hospital emphasized that it had “robust processes in place to maintain safe and effective patient care.”

[above via Cyberscoop post] Update 1 / Update 2
Nintendo hacker sentenced to 3 years in prison for hack
1st December 2020 | Target:** Japanese gaming Nintendo **| Reported Here
It’s game over for a notorious Nintendo hacker.
A 21-year-old man who leaked details about the Nintendo Switch prior to its 2017 launch and was later caught with child porn when authorities investigated has been sentenced to three years in prison.

[above via Nypost post] Update 1 / Update 2
Cyber-Attack Exposes Data of 295,000 Colorado Springs Patients
1st December 2020 | Target:** AspenPointe**| Reported Here
An American nonprofit psychological well being and behavioral wellbeing solutions supplier has been notifying patients of a modern cyber-attack that uncovered the shielded wellness facts (PHI) of extra than 295,000 patients.
AspenPointe, which is based mostly in Colorado Springs, Colorado, was successfully targeted by cyber-criminals in September 2020. The attack forced the health care provider to consider its programs offline, resulting in quite a few times of operational disruption.

[above via The Cyber Security post] Update 1
Data Stolen from America’s Largest Fertility Clinic Operator
30th November 2020 | Target:** Fertility Clinic **| Reported Here
Data including Social Security numbers has been stolen from the largest fertility clinic operator in the United States in a cyber-attack.
US Fertility runs 55 clinics at various locations in 10 of America’s 50 states. The company, established in May 2020, is the result of a partnership between private equity firm Amulet Capital Partners and Shady Grove Fertility.

[above via Gadgetpage post] Update 1
Delaware County Pays $500,000 Ransom After Outages
30th November 2020 | Target:** Delaware County**| Reported Here
It was reported that, over the weekend, Delaware County, Pennsylvania has paid a $500,000 ransom after their systems were hit by the DoppelPaymer ransomware.

[above via Is Buzz News post] Update 1
IIoT chip maker Advantech hit by ransomware, $12.5 million ransom
28th November 2020 | Target: **Advantech **| Reported Here
The IoT giant Advantech has become the latest victim of a severe cyber attack. Reportedly, Advantech has fallen prey to the infamous Conti ransomware attack where the hackers have demanded a whopping 750 BTC as ransom.

[above via Latesthackingnews post] Update 1
Louisiana Hospitals Report Data Breach
23rd November 2020 | Target: **Louisiana Hospitals **| Reported Here
The data of thousands of patients has been exposed following a cyber-attack on Louisiana State University medical centers.
LSU Health New Orleans issued a HIPAA breach notification on November 20 after detecting a cyber-intrusion into an employee’s electronic mailbox.
“The intrusion appears to have occurred on September 15, 2020, and the mailbox access was discovered and disabled on September 18, 2020,” said LSU Health.

[above via gadgetpage post] Update 1
Americold Operations Downed by Cyber-Attack
18th November 2020 | Target: US cold storage firm Americold| Reported Here
Americold, a company whose cold-storage capabilities are integral to the U.S. food-supply chain (and soon, COVID-19 vaccine distribution), has confirmed an operations-impacting cyberattack, according to a filing with the Securities and Exchange Commission (SEC).

[above via Threat Post post]
Capcom hit by ransomware attack, up to 350,000 accounts may be affected
16th November 2020 | Target: **Capcom **| Reported Here
Capcom, the Japanese game maker behind the “Resident Evil” and “Street Fighter” franchises, has confirmed that hackers stole customer data and files from its internal network following a ransomware attack earlier in the month.
That’s an about-turn from the days immediately following the cyberattack, in which Capcom said it had no evidence that customer data had been accessed.
[above via Techcrunch post] Update 1
Data Breach Hits 28 Million Texan Drivers
13th November 2020 | Target: **Texan Drivers **| Reported Here
Vertafore, a provider of insurance software, has disclosed this week a data breach, admitting that a third-party accessed the details of 27.7 million Texas drivers.
The incident is believed to have taken place sometime between March 11 and August 1, and happened as a result of human error when three data files were inadvertently stored in an unsecured external storage service.

[above via Zdnet post] Update 1
Laptop maker Compal hit by ransomware, $17 million demanded
9th November 2020 | Target: **Compal Electronics **| Reported Here
Compal, a Taiwanese electronics company that builds laptops for some of the world’s largest computer brands, suffered a ransomware attack over the weekend.
Responsible for the breach is believed to be the DoppelPaymer ransomware gang, according to a screenshot of the ransom note shared by Compal employees with Yahoo Taiwan reporters.

[above via Zdnet post] Update 1
Ryuk Ransomware operators made $34 million from one victim
7th November 2020 | Target: **Multiple Individuals and Firms **| Reported Here
One hacker neighborhood that’s concentrating on excessive-revenue companies with Ryuk ransomware obtained $34 million from one sufferer in alternate for the decryption key that unlocked their computers.
The menace actor is extremely proficient at gripping laterally interior a compromised community and erasing as grand of their tracks as possible sooner than detonating Ryuk ransomware.

[above via Gisttree post]
US Seizes $1bn from Silk Road Crypto Account
5th November 2020 | Target: **Silk Road Crypto Account **| Reported Here
The United States has seized more than $1bn in cryptocurrency believed to be proceeds from a defunct online marketplace that was notorious for selling unlawful goods and services.
On November 5, the Department of Justice filed a civil complaint to seek the forfeiture of thousands of Bitcoins seized by law enforcement on November 3, 2020, from an account associated with Silk Road. The seizure represents the largest confiscation of cryptocurrency in the department’s history.
[above via Infosecurity post] Update 1
Italian beverage vendor Campari knocked offline after ransomware attack
5th November 2020 | Target: Campari Reported Here
Beverage giant Campari Group has become the latest big-name brand to suffer an apparent ransomware attack forcing IT services offline.
The Italian firm issued a statement on Tuesday claiming it was hit by a malware attack “presumably” on Sunday November 1.
“The groups IT department, with the support of IT security experts, immediately took action to limit the spread of malware in data and systems,” it added.

[above via Infosecurity post] Update 1 / Update 2
US Seizes $24M in Crypto as Part of Brazilian Probe Into $200M Fraud Scheme
5th November 2020 | Target: **Brazilian Businesses **| Reported Here
Acting on request of the government of Brazil, U.S. authorities seized virtual currency worth an estimated US$24 million which Brazilian authorities claim are proceeds of a fraudulent scheme, the Justice Department announced Wednesday.
The Department said Brazil asked “for assistance in connection with a large cryptocurrency fraud scheme in a Brazilian federal police investigation called Operation Egypto.”

[above via Occrp post] Update 1 / Update 2
Montreal Metro Hacker Demands $2.8m Ransom
29th October 2020 | Target: **Montreal’s transit agency **| Reported Here
A hacker behind the recent ransomware attack on Montreal’s transit agency, that shut down 624 operationally sensitive servers, has demanded $2.8 million in ransom to restore normal operations.
The ransomware attack resulted in the shutdown of around 1,000 of 1,600 servers operated by the Société de transport de Montréal (STM), the transit agency of Montreal. While normal bus and metro services were not affected, the reservation system for adapted transit went offline and so did the STM’s website.

[above via Teiss post] Update 1
US Army Base’s Twitter Account Hacked
22nd October 2020 | Target: **US Army’s **| Reported Here
A malicious hacker has been blamed for a series of lewd messages that emanated from the social media account of a US military base on Wednesday.
Followers of Fort Bragg’s official Twitter account were surprised by the sexual content of a number of tweets that began to appear at around 4:30pm ET.

[above via Infosecurity post] Update 1
M&S Boss Spoofed in Gift Voucher Scam
21st October 2020 | Target: **Marks and Spencer (M&S) **| Reported Here
Criminals are impersonating the boss of a major British multinational retailer to trick victims into sharing their bank account details.
Posing as Marks & Spencer CEO Steve Rowe, the scammers have posted fraudulent adverts online that promise victims the chance to win a gift voucher as part of a fictitious prize draw promotion.
When victims click on the link in the ad, they are taken to an M&S-branded portal and asked to provide their name, address, mobile phone number, and bank details including SORT code and account number.

[above via Startupdigital post] Update 1 / Update 2
Iran Reports Two Major Cyber-Attacks
14th October 2020 | Target: **Iranian Government **| Reported Here
Iran on Wednesday reported a “large-scale” cyberattack against two unspecified government institutions.
A spokesperson quoted by the official IRNA news agency said the attack did not cause any significant damage and was being investigated. He said the country has dealt with larger attacks in the past.

[above via Times Of Israel post] Update 1 / Update 2
Barnes & Noble hit by cyberattack that exposed customer data
14th October 2020 | Target: **Barnes & Noble **| Reported Here
American bookseller Barnes & Noble has been hit by cyber-criminals the day after resolving a connection issue with its Nook e-reader service.
The beleaguered bookstore has been emailing customers since Monday to notify them of the attack and warn them that their data may have been compromised.
“It is with the greatest regret we inform you that we were made aware on October 10, 2020, that Barnes & Noble had been the victim of a cybersecurity attack, which resulted in unauthorized and unlawful access to certain Barnes & Noble corporate systems,” states the notification email.

[above via Infosecurity post] Update 1 / Update 2 / Update 3
Hackney council hit by cyber attack
13th October 2020 | Target: **Hackney Council **| Reported Here
IT systems and resident-facing services at Hackney Council in London are currently offline following an apparent cyber security incident.
The council said its investigation was ongoing and provided no further details of exactly what has transpired, although it described it as a “serious cyber attack”.
Mayor of Hackney Philip Glanville said: “Our focus is on continuing to deliver essential frontline services, especially to our most vulnerable residents, and protecting data, while restoring affected services as soon as possible.

[above via Computer Weekly post] Update 1 / Update 2
Morgan Stanley fined $60m over data centre decommissioning failures
9th October 2020 | Target: **Morgan Stanley **| Reported Here
The US Office of the Comptroller of the Currency (OCC) has fined Morgan Stanley $60 million for failing to properly decommission two wealth management data centers in 2016.
The bank failed to properly oversee its contractors, and how they wiped data from servers and other hardware. Some customer information remained on the equipment after it was sold to recyclers, but there was no indication that any of the details were misused.
Plaintiffs in two class-action lawsuits filed against the bank this summer claimed the data left on the devices included Social Security numbers, passport information, and other account information.

[above via Datacenterdynamics post] Update 1
Cyber-attacks against Angolan news site and reporter
9th October 2020 | Target: **Angolan News Site and Journalists **| Reported Here
The website of Correio Angolense, one of Angola’s most respected independent online news sources, has been inaccessible since 25 September, when it was crashed by thousands of simultaneous connection attempts, many more than is normal. Its editor, Graça Campos, told RSF that everything indicates that this was a cyber-attack.

Skimming Attack on Boom! Mobile
6th October 2020 | Target: **Boom! Mobile **| Reported Here
A mobile network operator has fallen victim to a Magecart campaign designed to steal consumer financial data.
Malwarebytes researchers said on Monday that one of the latest organizations targeted by a Magecart group is Boom! Mobile, of which the firm’s US website has been compromised and is, at the time of writing, actively being used to harvest shopper information.

[above via Zdnet post] Update 1 / Update 2
Govt. Services Firm Tyler Technologies Hit in Apparent Ransomware Attack
23rd September 2020 | Target: **Tyler Technologies **| Reported Here
Tyler Technologies – one of the largest solution providers to state and local government in the U.S. – was hit in an apparent ransomware attack, according to KrebsOnSecurity.
Cybersecurity reporter Brian Krebs said the company copped to an intrusion to its system, but told him it was limited to internal company systems and had no impact on its customers.

179 Arrested for Darknet Drug Trafficking
22nd September 2020 ** **| Reported Here
Law enforcement officials arrested 179 people and seized more than $6.5 million in a worldwide crackdown on opioid trafficking on the darknet, the U.S. Justice Department said Tuesday.
The operation, which mainly occurred in the U.S. and in Europe, comes more than a year after officials took down the “Wall Street Market,” which was believed to be one of the largest illegal online marketplaces on the darknet.

[above via Abcnews post] Update 1 / Update 2
Cyber-Criminals Spoof Texas Government
21st September 2020 | Target: **Texas Goverment **| Reported Here
Scammers are impersonating governmental departments within the State of Texas to send out fake Requests For Quotations (RFQs).
On September 21, Abnormal Security revealed that it had spotted an attack email that impersonated the Texas Department of State Health Services.
Scammers used spoofing techniques to camouflage the sender address as an account that was affiliated with the official dshs.texas.gov domain.

[above via Tripwire post] Update 1
Data Breach at Long Island Hospital
21st September 2020 | Target: **Long Island hospital **| Reported Here
Long Island’s only tertiary care center and Regional Trauma Center has issued a warning to patients that their personal data may have been exposed as a result of a ransomware attack.
Stony Brook University Hospital has contacted patients by letter to notify them of a possible data breach following an attack on the hospital’s third-party vendor Blackbaud in May 2020.

[above via Infosecurity post] Update 1
Student Arrested Over Cyber-attacks on Indiana Schools
21st September 2020 | Target: **Valparaiso Community Schools **| Reported Here
A 13-year-old Benjamin Franklin Middle School student was arrested Thursday for hacking into his school district’s computer system.
On Friday, police confirmed the boy is now in the Porter County Juvenile Detention Center, and has been charged with offense against a computer user.

[above via Wamwamfm post] Update 1 / Update 2
Fatal Hospital Hack Linked to Russia
18th September 2020 | Target: **Düsseldorf University Hospital **| Reported Here
For the first time ever, a patient’s death has been linked directly to a cyberattack. Police have launched a “negligent homicide” investigation after ransomware disrupted emergency care at Düsseldorf University Hospital in Germany.

[above via Technologyreview post] Update 1
Minnesota’s second-largest health care data breach
16th September 2020 | Target: **Minnesota’s **| Reported Here
Hundreds of thousands of patients and donors to Children’s Minnesota and Allina Health hospitals are getting letters saying some of their personal data may have been exposed in a data breach,
Hundreds of thousands of patients and donors to Children’s Minnesota and Allina Health hospitals are getting letters saying some of their personal data may have been exposed in the second-largest health care data breach in state history.

[above via Startibune post] Update 1
DDoS Attacks Hit 1 Tbps in 2020
16th September 2020 | Target: Various **Organizations **| Reported Here
There has been a 151% increase in the number of DDoS attacks in the first half of 2020, compared to the same period in 2019.
According to Neustar’s latest CyberThreats and Trends Report, these attacks include the largest that Neustar has ever mitigated at 1.17 Tbps.
As reports of the number of detected DDoS attacks increase, Neustar said the number of attacks sized 100 Gbps and above grew by 275%, and the number of “small attacks,” sized 5 Gbps and below, increased by more than 200%. These small 5 Gbps and below attacks represented 70% of all attacks mitigated by Neustar between January and June 2020.

[above via Infosecurity post] Update 1
Data Breach Hits 46,000 US Veterans
14th September 2020 | Target:** US Veterans **| Reported Here
The Department of Veterans Affairs (VA) announced Monday that the personal information of around 46,000 veterans was accessed in a recent data breach.
The news came after the agency’s Financial Services Center discovered that an unauthorized user had accessed an application used to help veterans pay for medical care and diverted funds meant for community health providers.
[above via The Hill post] Update 1
US staffing firm Artech discloses ransomware attack
11th September 2020 | Target:** Artech Information Systems **| Reported Here
One of the largest IT staffing companies in America has been hit by a second ransomware attack in nine months.
At the start of September, Artech Information Systems disclosed a data breach caused by a ransomware attack perpetrated between January 5 and 8, 2020.
Attackers deployed the ransomware three days after gaining unauthorized access to some of the company’s systems. The incident was picked up by the company following reports of suspicious activity on the user account of an Artech employee.

[above via Infosecurity post]
Chinese Ambassador’s Twitter Account “Hacked”
10th September 2020 | Target:** Liu Xiaoming **| Reported Here
A pornographic post was ‘liked’ from the official account of Chinese ambassador Liu Xiaoming, after which the country has asked Twitter to initiate a probe in what it says is a hacking incident.
Xiaoming’s account showed the liked video for over an hour on Wednesday, leading to a number of comments and reactions before it was finally taken down.
[above via DNA India post] Update 1 / Update 2
Cryptocurrency exchange Eterbase hacked, $5.4 million worth of funds stolen
10th September 2020 | Target:** Eterbase **| Reported Here
ETERBASE, a Bratislava-based cryptocurrency exchange, disclosed this week a security breach. The exchange said hackers breached its internal network and stole cryptocurrency funds worth $5.4 million.
The incident, which was disclosed on Thursday, involved the theft of various cryptocurrencies from the company’s hot wallets.

[above via Zdnet post] Update 1
DOJ Scam Targets Elderly Americans
8th September 2020 | Target: **Elderly Americans **| Reported Here
The Office of Justice Programs’ Office for Victims of Crime (OVC) has received multiple reports that individuals claiming to represent the Department of Justice are calling members of the public as part of an imposter scam. The department strongly encourages the public to remain vigilant and not to provide personal information during these calls, which appear to target the elderly.

[above via Justice post] Update 1
Webmaster Portal Leaks 63 Million Records
8th September 2020 | Target: **Webmaster Portal **| Reported Here
The world’s largest webmaster form has been found wanting in terms of its cybersecurity posture after researchers discovered an unprotected database leaking data on nearly 900,000 users.
Digital Point provides a platform for members to chat and buy and sell websites, domains and digital services.
Back in July, researchers at WebsitePlanet teamed up with Jeremiah Fowler to discover an Elasticsearch database belonging to Digital Planet that was left online without password protection, exposing nearly 63 million records.

[above via Startupdigital post]
US Arrests Tourist Over Malware Conspiracy
26th August 2020 | Target: **Tesla **| Reported Here
The FBI has arrested a Russian tourist in America, who investigators say offered a Tesla employee $1 million to infect company computers with malware in a scheme to steal data and extort payment from the company.
Egor Igorevich Kriuchkov, 27, was arrested last week in Los Angeles and federally charged with conspiracy to damage a protected computer, after the Tesla employee alerted the company and the FBI.

[above via Dailymail post] Update 1
Data Firm Exposes 235 Million Social Media Profiles
19th August 2020 | Target: **Social Media App **| Reported Here
A Hong Kong-registered company that sells data on social media influencers has exposed as many as 235 million user profiles scraped from Instagram, TikTok, and YouTube on the web without a password or any other authentication required to access it, according to a report by British research firm Comparitech.
Security researcher Bob Diachenko, who leads Comparitech’s cybersecurity research team, uncovered three identical copies of a database which included names, contact information, images and statistics about followers on August 1, Comparitech said in the report on Wednesday.

[above via SCMP post] Update 1
Experian South Africa discloses data breach impacting 24 million customers
19th August 2020 | Target: **Experian **| Reported Here
Experian has suffered a major breach of customers’ personal information, affecting an estimated 24 million South Africans and nearly 800,000 businesses.
The credit reporting agency revealed in a statement yesterday that an individual fraudulently claimed to represent one of its client and then requested “services” from the firm, prompting the release of the data.

[above via Infosecurity post] Update 1
Jack Daniel’s-Maker Suffers REvil Ransomware Breach
17th August 2020 | Target: **Jack Daniel’s **| Reported Here
US wine and spirits giant Brown-Forman has become the most current big-name model to put up with a really serious ransomware-connected data breach, cyber-criminals have claimed.
The Jack Daniel’s-maker has released few particulars about the incident but claimed it productively prevented attackers from encrypting its documents.

[above via The Cyber Security post] Update 1
Looting Causes Data Breach at Walgreens
14th August 2020 | Target: **Walgreens **| Reported Here
The personal health information (PHI) of over 72,000 Walgreens customers has been exposed after looters broke into nearly 200 stores and stole prescriptions.
America’s second-largest pharmaceutical chain contacted impacted customers in July to disclose the data breach. Walgreens spokesperson Jim Cohn told the Philadelphia Inquirer that 180 Walgreens stores had been looted but declined to state which specific ones.

[above via Nationalcybersecuritynews post]
Hacker Steals $12M from DeFi Platform
11th August 2020 | Target: **DeFi Platform **| Reported Here
For most of the 13-year life of cryptocurrencies, exchanges were the epicentre for cyberheists. Now, a bigger hacking risk in the growing sector has exploded into view: peer-to-peer crypto platforms.
One such site, Poly Network, was at the centre of a $610 million (roughly Rs. 4,530 crores) cryptocurrency theft last week, one of the biggest ever. Within days of the heist, the decentralised finance (DeFi) platform said the “white hat” hacker or hackers had returned nearly all the loot.

[above via Gadgets NDTV post] Update 1
Capital One Fined $80m for 2019 Breach
6th August 2020 | Target: **Capital One **| Reported Here
Capital One has been fined $80m following its breach last year.
According to a statement from the Office of the Comptroller of the Currency (OCC), these actions were taken against Capital One “based on the bank’s failure to establish effective risk assessment processes prior to migrating significant information technology operations to the public cloud environment and the bank’s failure to correct the deficiencies in a timely manner”.

[above via Infosecurity post] Update 1 / Update 2
Online Exam Tool Suffers Data Breach
6th August 2020 | Target: **ProctorU **| Reported Here
A malware author has pleaded guilty to conspiracy for his role in a transnational cybercrime organization responsible for stealing over $568m.
Valerian Chiochiu, a.k.a. “Onassis,” “Flagler,” “Socrate,” and “Eclessiastes,” admitted being involved with one of the largest cyber-fraud enterprises ever created that victimized Americans in all 50 states and millions globally.

[above via Hackread post] Update 1
Malware Author Admits Role in $568m Cyber-Fraud
3rd August 2020 | Target: **Multiple Businesses and Individuals **| Reported Here
A malware author has pleaded guilty to conspiracy for his role in a transnational cybercrime organization responsible for stealing over $568m.
Valerian Chiochiu, a.k.a. “Onassis,” “Flagler,” “Socrate,” and “Eclessiastes,” admitted being involved with one of the largest cyber-fraud enterprises ever created that victimized Americans in all 50 states and millions globally.

[above via Cyberreport post]
Havenly Breach Hits In excess of 1.3 Million Accounts
2nd August 2020 | Target: **Havenly **| Reported Here
Havenly has become the latest online firm to suffer a serious breach of customer data after hackers published the information for free on the dark web.
Notorious dark web trader ShinyHunters was spotted last week posting the data of nearly 1.4 million accounts online.
They’re said to be part of a much bigger 386 million record trove including data from customers of Dave, Promo and HomeChef, which has been previously disclosed.

[above via Infosecurity post] Update 1
Business giant Dussmann Group’s data leaked after ransomware attack
30th July 2020 | Target: **Dussmann Group **| Reported Here
Dussmann Group has confirmed that one of their subsidiaries, Dresdner Kühlanlagenbau GmbH (DKA), recently suffered a ransomware attack and data was stolen.
Dussmann Group is the largest multi-service provider in Germany having subsidiaries focusing on facility management, corporate childcare, nursing and care for the elderly, and business systems solutions, including HVAC, electrical work, and elevators.

[above via Cybersafe post] Update 1
Drizly Breach Hits 2.5 Million Customer Accounts
29th July 2020 | Target: **Drizly **| Reported Here
Alcohol delivery startup Drizly has suffered a major breach of customer data, with nearly 2.5 million accounts compromised in an incident discovered earlier this month.
The firm - which describes itself as the world’s largest marketplace for beers, wines and spirits - partners with retail stores in over 100 North American cities.

[above via Infosecurity post] Update 1 / Update 2
Promo Data Breach Hits 14.6 Million User Accounts
29th July 2020 | Target: **Promo **| Reported Here
Promo.com, a video creation platform for businesses and agencies, has confirmed a data breach after bad actors posted a database containing 22 million user records on a hacking forum.
The award-winning video maker, which is partnered with social media venues such as Facebook and Instagram, allows users to create an unlimited number of promotional videos that can be shared online.

[above via Securityboulevard post]
Twitter Confirms 130 Accounts Hacked
17th July 2020 | Target: **Canadians **| Reported Here
Twitter said late on Thursday that hackers targeted about 130 accounts during the cyberattack this week, an incident in which profiles of many prominent personalities and organizations were compromised.
Hackers had accessed Twitter’s internal systems to hijack some of the platform’s top voices, including U.S. presidential candidate Joe Biden, reality TV star Kim Kardashian, former U.S. President Barack Obama, and billionaire Elon Musk, and used them to solicit digital currency.

[above via Venturebeat post] Update 1
Over Half of Canadians Victims of Cybercrime
16th July 2020 | Target: **Canadians **| Reported Here
More than half of Canadians have fallen victim to a cybercrime, according to a new report by the Cybersecure Policy Exchange (CPX) at Ryerson University in Toronto.
In the report Advancing a Cybersecure Canada: Introducing the Cybersecure Policy Exchange, the CPX revealed that 57% of Canadians say that they have been a victim of a cybercrime.

[above via Terabitweb post]
Bitcoin Thieves Hit Cashaa
13th July 2020 | Target: **Cashaa **| Reported Here
Cybercriminals have compromised a British cryptocurrency exchange, with more than $ 3 million in Bitcoin.
Cashaa halted all crypto-related transactions after cybercriminals stole more than 336 Bitcoin from their exchange. The company said users at first glance were unaffected by the theft.

[above via Oltnews post]
Zoom Zero-Day Bug Hits Legacy Windows Users
10th July 2020 | Target: **Zoom **| Reported Here
Zoom is scrambling to fix another zero-day vulnerability in its Windows client, this time potentially leading to arbitrary remote code execution.
Acros Security CEO, Mitja Kolsek, revealed the news in a blog post, claiming that the researcher who found the bug didn’t disclose to the vendor or a third-party broker, “but would not object to us reporting it to Zoom.”
“We analyzed the issue and determined it to be only exploitable on Windows 7 and older Windows systems. While Microsoft’s official support for Windows 7 has ended this January, there are still millions of home and corporate users out there prolonging its life with Microsoft’s Extended Security Updates or with 0patch,” he explained.

[above via Cybercureme post]
UCSF Pays $1.14m Ransomware Fee
29th June 2020 | Target: **UCSF **| Reported Here
The University Of California San Francisco finally confirmed that it had forked over $1.14m to ransomware thieves last week, less than a month after discovering that critical academic data related to its COVID-19 research had been encrypted.

[above via Infosecurity post] Update 1
Police Seize Alleged Bitcoin Raider’s $90m in Assets
22nd June 2020 | Target: Bitcoin Exchange Services | Reported Here
Police in New Zealand have seized $90m worth of assets belonging to a man wanted for cybercrimes in France and the United States.
Alexander Vinnik allegedly masterminded a Bitcoin laundering ring that handled billions of dollars via a digital currency exchange. He is also wanted for some minor crimes in his native Russia.

[above via Infosecurity post]
Sharp Rise in Web Attacks on Gamers
17th June 2020 | Target: Gamers | Reported Here
Cyber-criminals stepped up their efforts to victimize gamers while millions of people stayed at home this spring to slow the spread of COVID-19.
New research published today by Kaspersky found that in April, the daily number of blocked attempts to direct users to malicious gaming-themed sites increased by 54%, compared to January 2020.

[above via Nxtalpha post]
Cyber-Attack Hits US Nuclear Missile Sub-Contractor
3rd June 2020 | Target: US Nuclear Missile Sub-Contractor | Reported Here
A U.S. military contractor involved in the maintenance of the country’s Minuteman III nuclear arsenal has been hit by the Maze ransomware, according to reports – with the hackers making off with reams of sensitive information.

[above via Threat Post post]
REvil Ransomware Group Auctions Stolen Data
2nd June 2020 | Target: Various Companies | Reported Here
A prolific ransomware group has begun auctioning data stolen from victim organizations that refuse to pay up, marking an escalation in its monetization efforts.
The gang behind the REvil (aka Sodinokibi) variant this week took to its dark web blog to announce the first auction, related to a Canadian agricultural company it compromised which has declined to pay a ransom.

[above via Infosecurity post]
Minneapolis City and Police Websites Attacked
1st June 2020 | Target: Police Websites | Reported Here
The Minneapolis Police Department’s website has shown signs of a cyber-attack since late Saturday, days after a video purported to be from the hacktivist group Anonymous promised retribution for the death of George Floyd during an arrest.
Websites for the police department and the city of Minneapolis were temporarily inaccessible on Saturday as protesters in cities around the U.S. marched against police violence aimed at black Americans.

[above via Cybercureme post]
Norway’s Wealth Fund Loses $10m in Data Breach
15th May 2020 | Target: Norway’s Wealth Fund | Reported Here
Norway’s state-owned investment fund Norfund has halted all payments after losing $10m in an “advanced data breach.”
Norfund is a private equity company established by the Norwegian Storting in 1997 and owned by the Norwegian Ministry of Foreign Affairs. The fund receives its investment capital from the state budget and is the largest sovereign wealth fund in the world.
On May 13, Norfund announced that it was “cooperating closely with the police and other relevant authorities” after “a series of events” allowed fraudsters to make off with $10m.
The fund said that a data breach allowed defrauders to access information concerning a loan of US$10m from Norfund to a microfinance institution in Cambodia.

[above via Cybercureme post] Update 1
Ransomware Gang Demands $42 Million From Celebrity Law Firm
15th May 2020 | Target: Grubman Shire Meiselas & Sacks | Reported Here
The criminal group behind the REvil (Sodinokibi) ransomware is extorting a New York-based law firm, threatening to release sensitive files on the company’s celebrity clients unless the the firm pays a whopping $42 million ransom demand.
The extortion attempt is the result of a ransomware infection that Grubman Shire Meiselas & Sacks (GSMS) suffered last week.

[above via Zdnet post] Update 1
GoDaddy Suffers Data Breach
5th May 2020 | Target: GoDaddy | Reported Here
GoDaddy has confirmed a data breach that occurred back in October, impacting web hosting account credentials. The breach was caused by an unauthorized individual.
With the case, reported by ZDNet, the person was able to access login credentials of SSH accounts used in GoDaddy’s hosting environment. The company discovered an “unauthorized individual” had gained access to login credentials that enabled them to “connect to SSH” on the affected hosting accounts. The security incident that took place on October 19, 2019, was discovered on April 23, 2020.

[above via Digital Journal post] Update 1
Taiwan’s CPC suffers malware attack
4th May 2020 | Target: CPC Crop** | Reported Here
Ransomware has struck the computer systems of Taiwan’s state-owned energy company, CPC Corp., according to local media and private forensic reports reviewed by CyberScoop.

[above via Cyberscoop post] Update 1
Ransomware Payments Surge 33% as Attacks Target Remote Access
1st May 2020 | Target: Various Enterprise | Reported Here
The average sum paid by enterprises to ransomware attackers surged by 33% quarter-on-quarter in the first three months of the year, as victim organizations struggled to mitigate remote working threats, according to Coveware.
The security vendor analyzed ransomware cases handled by its own incident response team during the period to compile its latest findings.

[above via Cyberdot post]
Nintendo Breach Affects 160,000 User Accounts
24th April 2020 | Target: Nintendo | Reported Here
Nintendo said over 160,000 accounts have been hacked, due to attackers abusing a legacy login system.
Over the past few weeks, Nintendo gamers have been reporting suspicious activities on their accounts. According to the complaints, aired out on Twitter and Reddit, unauthorized actors were logging into victims’ accounts and abusing the payment cards connected to the accounts to buy digital goods on Nintendo’s online stores, such as V-Bucks, in-game currency used in Fortnite.

[above via Threatpost.com post] Update 1 / Update 2
Hackers Target Netflix and Disney+ with #COVID19 Phishing
19th April 2020 | Target: Netflix, Disney+ | Reported Here
Hackers are turning their attention to streaming services in an ongoing bid to capitalize on the current COVID-19 pandemic and increase their own profits, according to Mimecast.
The email security vendor revealed that it had detected the registration of over 700 suspicious domains designed to impersonate the Netflix brand in under a week. The recently launched Disney+ service is also coming under increasing scrutiny from black hats, it claimed.

[above via Info – Security post]
Equifax pays Indiana $19.5m to settle data breach case
16th April 2020 | Target: Equifax | Reported Here
On April 14, 2020, the Indiana Attorney General’s office announced that the state had reached a settlement agreement with Equifax in connection with Equifax’s 2017 data breach. Under the terms of the settlement, Equifax will pay a $19.5 million penalty. Indiana previously elected not to participate in a July 2019 multistate and Federal Trade Commission settlement with Equifax regarding the same data breach..

[above via National Law Review post] Update 1
Number of leaked government records increases by 278% in Q1, 2020
15th April 2020 | Target: Government | Reported Here
There has been a huge rise in the number of breached records of governments and individual politicians in the first quarter of 2020, according to research from Atlas VPN. The study showed there were 17 million leaked government records during this period: a 278% increase compared with the first quarter of 2019.

[above via Info security post] Update 1
Australians Arrested Over $2.6m Email Scam
3rd April 2020 | Target: Various Businesses | Reported Here
NSW Police have charged two men over their alleged involvement in a $2.6 million email scam syndicate.
The scam involved sending altered invoices to legitimate businesses which unwittingly paid the scammers who then transferred the money into their personal bank accounts.

[above via ia.acs post] Update 1
New Marriott data breach impacts 5.2 million guests
31st March 2020 | Target: Marriott | Reported Here
Hotel chain Marriott International announced today that it has suffered a second data breach.
According to an incident notification published on their website, the company spotted unusual activity occurring in an app that guests use to access services during their stay.
An investigation into the activity revealed that the login credentials of two Marriott employees had been used to access “an unexpected amount” of guest information.

[above via Info Security post] Update 1
Rights Group: APP Bank Fraud Cost Consumers £1bn
18th March 2020 | Target: Right Group | Reported Here
Financial institutions could have prevented hundreds of millions of pounds worth of fraud over the past three years by implementing a simple payee-checking service online, a consumer rights group has claimed.
Which? estimates that £1.1 billion has been lost to bank transfer fraud since 2017. In these cases, a scammer posing as a trusted entity tricks the victim to transfer money to a bank account under their control - known as “authorized push payment” (APP) fraud.

[above via Security Intelligence post] Update 1
Ryuk Ransomware Takes Out Durham, North Carolina
8th March 2020 | Target: Durham, North Carolina | Reported Here
The city of Durham, North Carolina temporarily disabled its phone system last weekend after suffering a Ryuk ransomware attack.
The city of Durham and Durham County published a joint statement on March 8 in which they revealed that a malware attack had affected their IT services. According to the statement, the government bodies first learned of the security incident on March 6. Both entities relied on their notification systems to alert IT teams of the attack.

[above via Security Intelligence post] Update 1
266,000 Passwords Stolen in Trident Crypto Fund Data Breach
6th March 2020 | Target: Trident Crypto Fund | Reported Here
In a major privacy breach, the usernames and passwords of more than a quarter of a million Trident Crypto Fund customers have been stolen and published online.
Technical director of cybersecurity firm DeviceLock Ashot Oganesyan told Russian news outlet IZ the database - which contains email addresses, cellphone numbers, encrypted passwords and IP addresses - had been uploaded to various file sharing websites on February 20.

[above via Coin-Telegraph post
UK ICO Fines Cathay Pacific with £500,000 for 2018 Data Breach
4th March 2020 | Target: Cathay Pacific | Reported Here
The Information Commissioner’s Office (ICO) has fined Cathay Pacific Airways Limited £500,000 for failing to protect the security of its customers’ personal data.
Between October 2014 and May 2018 Cathay Pacific’s computer systems lacked appropriate security measures which led to customers’ personal details being exposed, 111,578 of whom were from the UK, and approximately 9.4 million more worldwide.

[above via Ico post] Update 1 / Update 2
Ransomware Attack: Georgia City Pays $380K Ransom to Hackers
2nd March 2020 | Target: Cartersville, Georgia | Reported Here
Almost one year after a ransomware attack struck the city of Cartersville, Ga., municipal officials revealed that they paid a ransom of $380,000 to regain access to their files.
The news was made known after the local Daily Tribune News filed a Freedom of Information Act request, which disclosed the payment to mitigate the May 4, 2019 attack. The Daily Tribune found that the initial ransom demand was for $2.8 million, payable in bitcoin, and that the city’s insurance paid the majority of the cost.

[above via Sc-Magazine post] Update 1
Desjardins Group Breach Cost $38m Higher Than Expected
27th February 2020 | Target: Desjardins Group | Reported Here
Last year, the Quebec based financial institution Desjardins Group suffered from a data breach carried out intentionally by a malicious employee who had access to baking details. As a result of this individual’s actions, the data of 4.2 million Desjardins customers was exposed and 1.8 million credit cardholders who were not Desjardins members were affected as well. Original reparation estimates were around $70 million, but earlier this week the company has stated that the breach is likely to cost them roughly $108 million.

[above via Oodaloop post]
Shark Tank Star Corcoran Loses $400K in Email Scam
26th February 2020 | Target: Barbara Corcoran | Reported Here
“Shark Tank” judge Barbara Corcoran lost nearly $400,000 in an elaborate email scam that tricked her staff.
Corcoran said someone acting as her assistant sent an invoice to her bookkeeper earlier this week for a renovation payment. She told People that she had “no reason to be suspicious” about the email because she invests in real estate, so the bookkeeper wired $388,700 to the email address.

[above via Cnn post] Update 1 / Update 2 / Update 3
Ransomware-hit US gas pipeline shut for two days
18th February 2020 | Target: US Natural Gas Pipeline ** **| Reported Here
A ransomware attack on a US natural gas facility meant a pipeline had to be shut down for two days, the US Department of Homeland Security (DHS) has said.
However, it did not name the facility or say when the attack happened.
A malicious link sent to staff at the facility eventually caused the shutdown “of the entire pipeline asset”.

[above via Bank Info Security post] – Update 1
Official: Puerto Rico Govt Loses $2.6M in Phishing Scam
12th February 2020 | Target: **Puerto Rico **| Reported Here
Puerto Rico (AP) - Puerto Rico’s government has lost more than $2.6 million after falling for an email phishing scam, according to a senior official.
The finance director of the island’s Industrial Development Company, Rubén Rivera, said in a complaint filed to police Wednesday that the agency sent the money to a fraudulent account.

[above via Ap News post] – Update 1 / Update 2
A tail of two ransomware attacks
7th February 2020 | Target: **Two schools **| Reported Here
Two schools, two ransomware attack and two different outcomes.
The Allegheny Intermediate Unit school system was able to fend off a recent ransomware attack using back up files, meanwhile the University of Maastricht just disclosed it paid 30 bitcoins to regain control of its encrypted computer network.

[above via Zephymet post]
Altsbit Claims it has Been Hacked
7th February 2020 | Target: **Altsbit **| Reported Here
Cyber-criminals have stolen “almost all funds” entrusted to crypto exchange platform Altsbit.
The Italian exchange announced it had become the target of a devastating hack yesterday on Twitter. According to their posts, criminals made off with 1,066 Komodo (KMD) tokens and 283,375 Verus (VRSC) “coins” with a combined value of $27,000.
Funds kept in cold storage - crypto coins whose private keys are stored on devices that exist in an offline environment - were not swiped in the cyber-heist.

[above via Info Security post] – Update 1 / Update 2
Canadian insurance company lost nearly US$1M in ransomware attack
30th January 2020 | Target: **Insurance Company **| Reported Here
Canadian insurance company lost nearly US$1M in ransomware attack
Computers at a Canadian insurance company were disabled for more than one week due to a ransomware attack that resulted in a payout of nearly US$1 million.

[above via Headtopics post]
Canadian Teen Charged for $50 Million Cryptocurrency Theft
17th January 2020 | Target: **Cryptocurrency **| Reported Here
An eighteen-year-old from Montreal is facing four criminal charges connected to a $50 million SIM-swapping scam targeting cryptocurrency holders, Infosecurity Magazine reported on Jan. 17.
The hacker, Samy Bensaci, is accused by Canadian authorities of being part of a ring that stole millions of dollars in cryptocurrency from American and Canadian holders. The theft is said to have occurred in spring of 2018, with Québec police representative Hugo Fournier saying that the hackers were responsible for the theft of “$50 million from our neighbors to the south and $300,000 in Canada.”

[above via Coin Telegraph post] – Update 1
New Orleans Mayor: Ransomware Attack Cost City $7 Million
16th January 2020 | Target: **New Orleans **| Reported Here
A ransomware attack on New Orleans has racked up at least $7 million in financial damage to The City That Care Forgot, its mayor said.
New Orleans was able to get back $3 million through a cyber insurance policy, the mayor told WVUE, which also cited Chief Administrative Officer Gilbert Montano as saying the city has an IT backlog in the wake of the December attack.

[above via Sc Magazine post]
Texas school district lost $2.3 million in a phishing email scam
12th January 2020 | Target: **Manor School **| Reported Here
The Manor Independent School District fell victim to an apparent phishing scam to the tune of $2.3 million.
Officials for the Texas school system did not release many details other than to say in a January 10 statement posted on Facebook that the incident was caused by a phishing email and that the local police and FBI are currently working the case.
The Manor Police Department told CNN the scam included three separate fraudulent transactions that took place in November.

[above via Sc Magazine post] – Update 1
Albany airport pays ransom after hit by cyber hackers
10th January 2020 | Target: **Albany Airport **| Reported Here
Albany International Airport announced this week that its administrative computers had been locked down by a crypto virus on Christmas Day.
Airline, air traffic control and Transportation Security Administration computers all were not affected, so safety and security were never at risk, the Albany County Airport Authority said in a news release issued Friday.

[above via Daily Gazette post] – Update 1
UK Banks Foiled by Travelex Ransomware Attack
8th January 2020 | Target: **Travelex **| Reported Here
The New Year’s Eve cyber-attack on currency exchange bureau Travelex is disrupting services for UK bank customers.
Travelex took all its systems offline as a precautionary measure after being hit by what it initially described as a “software virus” on December 31. On January 7, the company released a statement fingering the culprit as a type of ransomware known as Sodinokibi and also commonly referred to as REvil.

[above via Info -Security post] – Update 1
UK Banks Foiled by Travelex Ransomware Attack
7th January 2020 | Target: **Google **| Reported Here
The incidents in question had exposed the data of over 10 million users.
The proposed settlement fund will be diverted to pay class claimants and attorney’s fees and costs.
Google has agreed to pay $7.5 million to settle class-action lawsuits filed against the company over Google+ data breach incidents. The incidents in question had exposed the data of over 10 million users.

[above via Cyware post] – Update 1
’Serious cyber-attack’ on Austria’s foreign ministry
5th January 2020 | Target: **Austrian Foreign Ministry **| Reported Here
The Austrian Foreign Ministry sounded the alarm bells of an ongoing “serious cyber-attack” that started in the late hours of Saturday January 4, 2019. Considering the signatures and the pattern of the attack, experts suggest this cyber-attack could possibly be carried out by a state sponsored threat actor. The attack, which began on Saturday night, was continuing and, “as per experts it could last several days,” a foreign ministry spokesman added.

[above via Ciso-Mag post] – Update 1
Six Customers Affected by Ransomware Attack on CyrusOne
5th December 2020 | Target: **CyrusOne **| Reported Here
Six New York-area managed service customers of data center provider giant CyrusOne have been affected by a ransomware attack.
These managed service clients have experienced availability issues due to a ransomware program encrypting certain devices in their network, a spokesperson for Dallas-based CyrusOne said in a statement. The company said it’s currently working with law enforcement and forensics firms to investigate the attack, as well as with the involved customers to restore their affected systems.

[above via Crn post] – Update 1/ Update 2
Canadian Territory Nunavut Suffers Ransomware Attack
4th November 2019 | Target : **Nunavut **| Reported Here
The Government of Nunavut is the latest victim of a sophisticated ransomware attack. In an official statement, the Premier of Nunavut, Joe Savikataaq, stated he noticed a new and advanced type of ransomware that affected their network systems across the territory on November 2, 2019.
The attack encrypted individual files on various servers and workstations impacting all government online services. “All government services requiring access to electronic information stored on the Government of Nunavut (GN) network are impacted, except Qulliq Energy Corporation,” said Savikataaq.

[above via Cisomag post] – Update 1
Marriott announces exposure of associate’s Social Security numbers
1st November 2019 | Target : **Marriott **| Reported Here
Marriott has once again suffered a cyber attack. This time, Marriott warns some of its associates about a security breach affecting their Social Security Numbers. What makes this incident tricky is that Marriott is facing trouble contacting some of the victims.
Marriott Security Breach Affects Associates Marriott International Inc.
has recently warned of a security breach affecting some associates. Precisely, the incident exposed the Social Security Numbers of the associates to an unknown attacker. As revealed via a security notice, the incident primarily hit a third party vendor who once collaborated with Marriott.

[above via Latesthackingnews post] – Update 1
North Korean Malware Found at Indian Nuke Plant
31st October 2019 | Target: **Nuclear Power Station **| Reported Here
The network of one of India’s nuclear power plants was infected with malware created by North Korea’s state-sponsored hackers, the Nuclear Power Corporation of India Ltd (NPCIL) confirmed today.
News that the Kudankulam Nuclear Power Plant (KNPP) might have been infected with a dangerous strain of malware first surfaced on Twitter on Monday.
Pukhraj Singh, a former security analyst for India’s National Technical Research Organization (NTRO), pointed out that a recent VirusTotal upload was actually linked to a malware infection at the KNPP.
The particular malware sample included hardcoded credentials for KNPP’s internal network, suggesting the malware was specifically compiled to spread and operate inside the power plant’s IT network.

[above via Zdnet post] – Update 1 / Update 2
Ocala police: Scammers swiped nearly $750,000 from city
28th October 2019 | Target: **Ocala city **| Reported Here
Police say scammers posing as a local construction company doing business with a north Florida city got an employee to change information that sent $742,376 to a fraudulent bank account.
The Ocala Star-Banner reports a senior accounting specialist for the city of Ocala received an email in September that was believed to be from Ausley Construction. It included a form requesting the city to change Ausley’s banking information.

[above via Nbcmiami post] – Update 1
UN, NGOs targeted by ongoing phishing attack
25th October 2019 | Target: **UN, NGOs **| Reported Here
Security researchers are warning of an ongoing mobile-aware phishing campaign targeting the United Nations and various NGOs for Okta, Office 365 and Outlook account credentials.
The two domains hosting the phishing content have been live since March 2019, with most of the the SSL certificates used valid in two main date ranges: May 5-August 3, 2019, and June 5-September 3, 2019, according to Lookout.
Interestingly, Javascript on the phishing pages can detect if the user is on a mobile device, and deliver relevant content to them. Lookout warned that mobile browsers typically truncate URLs, which can help phishing attempts by making it harder for users to spot any deception.

[above via Cisomag post] – Update 1
Stripe Users Targeted in Phishing Attack That Steals Banking Info
17th October 2019 | Target: **Bank Data. **| Reported Here
A new phishing campaign that targets Stripe users to steal banking information has been uncovered.
Attackers are evading detection by blocking users from viewing the destination of embedded links.
Stripe is an online platform that enables businesses to deal with payments. It handles billions of dollars annually and has a rich client base of reputed brands. This makes Stripe an attractive target for hackers.

[above via It – news post] – Update 1 / Update 2
Malware takes down some Pitney Bowes systems
14th October 2019 | Target: **Pitney Bowes. **| Reported Here
Global shipping and postage giant Pitney Bowes has had its operations disrupted by ransomware, with customers being unable to access some of its services.
Pitney Bowes acknowledged the attack early this morning Australian time.
SendPro customers currently can’t refill postage or upload transactions on their mailing machines, Pitney Bowes advised.
It is also not possible to access SendPro Online in the UK and Canada, or the ‘Your Account’ page for customers and the Pitney Bowes Supplies webstore.
Mail360 Scans and MIPro Licensing are also down, the company said, with the Software and Data Marketplace being unavailable.

[above via cyware post] – Update 1 / Update 2
Cyber-Attacks Hit Defense Contractors in Europe and North America
27th September 2019 | Target: **Rheinmetall AG. **| Reported Here
Rheinmetall AG and Defence Construction Canada (DCC), both major defense contractors, were each at the receiving end of disruptive cyberattacks this month. Rheinmetall AG has been hit with what the firm referred to as “malware attacks” since September 24. As a result, the “normal production processes ” at company’s plants in Brazil, Mexico and the US have been significantly disrupted. The company says that it may take between two to four weeks to resolve all issues resulting from the attacks.
Separately, DCC suffered a “cyber incident” on September 11 that disrupted various IT systems. The company has launched in investigation into the attack and is currently still working to fully recover all impacted systems.

[above via Oodaloop post] – Update
Ransomware Attack Disrupts Wyoming Health Services
23rd September 2019 | Target: Campbell County Health.| Reported Here
Campbell County Health (CCH) in Wyoming on Sept. 20 was hit with a ransomware attack that has severely disrupted the facility’s computer network, requiring a return to paper record keeping and the transfer of some patients to non-affected hospitals.
In a Sept. 23 press conference posted on Facebook, CCH officials said the attack’s impact has been widespread, but at this time it is not believed any patient information was compromised. Very few details concerning the attack is known at this time, but an investigation is ongoing and includes a third-party cybersecurity firm along with local, state and federal law enforcement.
A hospital spokeswoman told SC Media that she could not comment on the ransom demand amount, whether or not paying it is being considered, or if the hospital will use backed-up files to recover from the attack.

[above via Sc-magazine post] – Update 1 / Update 2
North Korean Malware Attacks ATMs and Banks
23rd September 2019 | Target: ATM | Reported Here
The infamous Lazarus Group is behind new malware discovered targeting ATMs and back-office systems in Indian banks and research centers, according to Kaspersky.
The Russian AV vendor claimed in a new report that it discovered the ATMDtrack malware back in late summer 2018. It is designed to sit on targeted ATMs and effectively skim the details of cards as they are inserted into the machine.
However, digging a little deeper, the researchers found another 180+ new malware samples similar to ATMDtrack but which were not designed to target ATMs.

[above via Info-Security post] – Update 1 / Update 2
Hackers Steal $4.2m from State Troopers’ Pension Fund
6th September 2019 | Target: Oklahoma | Reported Here
Cyber-thieves targeting a pension fund for law enforcement officers employed by the state of Oklahoma have made off with $4.2 million.
The money was stolen from a fund of more than $1 billion set aside to pay pensions and benefits to around 1,500 retired highway troopers, park rangers, state agents, and other law enforcement officers.

[above via Info-Security post] – Update 1 / Update 2
Scams and Ransomware Cost Kiwis $6.5m in 3 Months
6th September 2019 | Target: Goverment | Reported Here
New Zealand has reported the country’s highest ever recorded quarterly financial losses to cybercrime.
A report published yesterday by the government’s national Computer Emergency Response Team (CERT NZ) revealed that $6.5 million in direct financial losses was reported nationwide in the second quarter of 2019.
CERT NZ’s findings show a marked increase in the number of cybersecurity attacks inflicted on businesses and individuals across the country between quarters one and two of this year.

[above via Nxt Alpha post] – Update 1
New Bedford Hit With $5.3m Ransomware Demand
5th September 2019 | Target: Massachusetts City | Reported Here
After being hit by a ransomware attack, Massachusetts city New Bedford faced a payout demand of more than $5 million – one of the latest known ransoms ever.
After a ransomware attack slapped a hefty payout demand of $5.3 million on New Bedford, Mass., the city announced that it is instead opting to pick up the pieces and restore what it can from backups itself.
If the city had opted to pay, the payout would have been the largest known ransom payout for an attack yet.

[above via Threatpost.com post] – Update 1
Global Breach Costs Set to Top $5 Trillion By 2024
29th August 2019 | Target: Global | Reported Here
A new report from Juniper Research found that the cost of data breaches will rise from $3 trillion each year to over $5 trillion in 2024, an average annual growth of 11%.
This will primarily be driven by increasing fines for data breaches as regulation tightens, as well as a greater proportion of business lost as enterprises become more dependent on the digital realm.
The research noted that while the cost per breach will steadily rise in the future, the levels of data disclosed will make headlines but not impact breach costs directly, as most fines and lost business are not directly related to breach sizes.

[above via Help Net Security post] – Update 1
City of London Hit by One Million Cyber-Attacks Per Month
23rd August 2019 | Target: London City | Reported Here
Cyber criminals have their sights set on bigger and bigger targets, hitting the European Central Bank (ECB) twice in the past five years, and now launching a relentless attack on the City of London Corporation.
According to findings released under Freedom of Information (FOI) legislation, the municipal governing body of the City of London was hit with nearly three million attacks in just the first three months of 2019. This war of attrition has put 10,000 residents of the City of London in the line of fire, as well as 10 million annual tourists and 400,000 daily commuters entering the city.

[above via Insurance Business mag post] – Update 1
Alaska is the Most Scammed State in America
21st August 2019 | Target: Alaska | Reported Here
An annual report on cybercrime by the Federal Bureau of Investigation has revealed Alaska to be the most scammed state in America for the second year running.
With more than $450 million stolen, sunny California lost more money than any other state, but at 21.67 victims per 10,000 residents, Alaska had the highest per capita victim count.
Although more people were scammed in The Last Frontier State than in any other US state, Alaskans lost the least amount of money per person, with each victim being conned out of $2,256.30 on average.

[above via Info Security post] – Update 1
Ransomware Attack Hits 22 Texas Town
20th August 2019 | Target: local Goverment| Reported Here
HOUSTON - Computer systems in 22 small Texas towns have been hacked, seized and held for ransom in a widespread, coordinated cyberattack that has sent state emergency-management officials scrambling and prompted a federal investigation, the authorities said.
The Texas Department of Information Resources said Monday that it was racing to bring systems back online after the “ransomware attack,” in which hackers remotely block access to important data until a ransom is paid. Such attacks are a growing problem for city, county and state governments, court systems and school districts nationwide.

[above via Ny Times post] – Update 1 / Update 2 /
Hackers Leave Ransom Note For 700K Records
15th August 2019 | Target: **Hotels **| Reported Here
Hackers claim to have stolen 700,000 customer records from Choice Hotels thanks to an exposed MongoDB instance, it has emerged.
The US-based chain, which runs franchised outlets in over 40 countries worldwide, is now being held to ransom after the hackers left a note demanding 0.4 Bitcoin (around $3800) in payment for the data, which they claimed to have copied.
Security researcher Bob Diachenko worked with security firm Comparitech to discover the database, which was left completely exposed online. However, hackers had already got there. It was only left online for four days without password protection before attackers found the account.

[above via Info Security post] – Update 1 / Update 2 /
North Korean Hackers Amass $2bn Via Cyber-Attacks
8th August 2019 | Target: **Banks **| Reported Here
North Korea has turned to cybercrime to steal money and fund its nuclear program following global sanctions, a new report from the UN has claimed.
It seems as the punishments imposed by the UN Security Council on North Korea (DPRK) in 2006 to choke funding for the country’s nuclear program did little good, as a confidential UN report, states that North Korean state-sponsored hackers generated more than $2 billion through a myriad of illegal activities, with the proceedings going to the weapons of mass destruction fund.

[above via IT Proportal post] – Update 1 / Update 2 /
Cybercrime Costs Global Economy $2.9m Per Minute
24th July 2019 | Target: **World Economy **| Reported Here
The report is based on an analysis of malicious activity on the internet using proprietary global intelligence and third-party research.
The analysis also reveals that every minute, top companies pay £20 because of security breaches, hacks on cryptocurrency exchanges cost £1,550, and phishing attacks cost £14,200.
Every minute, 2.4 phishing sites went live and seven malicious redirectors, 0.32 blacklisted apps, and 0.21 Magecart attacks were detected.
Looking ahead, the report predicts that ransomware will cost the global economy £17,817 a minute in 2019.

[above via Computer Weekly post] – Update 1 / Update 2 / Update 3
Lancaster University students’ data stolen in cyber-attack
23rd July 2019 | University: **Lancaster **| Reported Here
Lancaster University has confirmed that it was “subject to a sophisticated and malicious phishing attack” which resulted in breaches of student and applicant data.
This has led to undergraduate student applicant data records for 2019 and 2020 being accessed, including names, addresses, telephone numbers and email addresses. Lancaster confirmed in its statement that it was “aware that fraudulent invoices” were being sent to some undergraduate applicants and has warned applicants to be aware of any suspicious approaches.
Also breached was Lancaster’s student records system. “At the present time we know of a very small number of students who have had their record and ID documents accessed,” it confirmed.

[above via Info Security post] – Update 1 / Update 2
Equifax to Pay $575m in Data Breach Settlement
22nd July 2019 | Company: **Equifax **| Reported Here
In a settlement between Equifax and the United States, the Federal Trade Commission (FTC) and Consumer Financial Protection Bureau (CFPB), Equifax will pay $575 million for damages related the to 2017 data breach, according to today’s press release.
The allegations against Equifax claimed that the company failed to take “reasonable steps to secure its network led to a data breach in 2017 that affected approximately 147 million people,” the release stated.
“In its complaint, the FTC alleges that Equifax failed to secure the massive amount of personal information stored on its network, leading to a breach that exposed millions of names and dates of birth, Social Security numbers, physical addresses, and other personal information that could lead to identity theft and fraud.”

[above via Info Security post] – Update 1 / Update 2
Iranian Hackers attack linkedin users with phishing campaigns
22nd July 2019 | Website : L**inkedin **| Reported Here
Iranian Hackers attack Iranian hackers have launched a new malware attack. The cyber attack is initiated from social networking site, LinkedIn, and begins with an invitation to connect online. When the recipient accepts the LinkedIn connection, the hacker then attempts to trick the user into downloading malicious files. The malware attack was discovered in June by cyber security research firm FireEye. The cyber attack is being carried out by Advanced Persistent Threat Group APT34 which is an Iranian state sponsored hacking organization.

[above via Askcybersecurity post] – Update 1 / Update 2
‘Wizard’ cybersecurity expert charged with record hack of Bulgarian tax agency
17th July 2019 | Target : Governments agency| Reported Here
A cybersecurity expert accused of hacking the data of more than 5 million Bulgarian taxpayers was released by police Wednesday after his charges were downgraded.
Kristian Boykov, a 20-year-old Bulgarian cybersecurity worker, was arrested in Bulgaria’s capital Sofia last week in connection to the breach. Police raided his home and seized computers and mobile devices with encrypted information. The hacker was found by police through the computer and software used in the attack, according to the Sofia prosecutor’s office.

[above via Npr.org post] – Update 1
TrickBot malware may have hacked 250 million email accounts
13th July 2019 | Target : **Governments **| Reported Here
Malicious actors behind the information-stealing malware TrickBot have added a new module that has helped them illicitly gather a database of 250 million legitimate email addresses.
Millions of these harvested addresses are linked to government agencies and employees in the U.S., according to Deep Instinct, whose researchers uncovered the new module and the giant database. In all likelihood, these addresses were collected for the purpose of targeting them in future TrickBot operations, explains a July 12 blog post by Deep Instinct malware and cyber intelligence expert Shaul Vilkomir-Preisman, who was assisted by fellow researcher Tom Nipravski.

[above via Scmagazine post] – Update 1 / Update 2
Hackers Steal $32M Of Crypto From Japanese Exchange
12th July 2019 | Country: **Japan **| Reported Here
A cryptocurrency exchange in Japan has admitted that it was hacked and lost 3.5 billion yen ($32 million) of digital currency, according to reports.
The company, based in Tokyo, is called Remixpoint, and it runs an exchange called BITPoint. The company also has used car, travel and energy businesses. The company apologized for the hack on Friday (July 12), saying that the losses were confirmed a day before.
The complete picture of the hack and theft is under investigation, and the theft included Bitcoin, Ethereum, Ripple and other well known digital currencies.
Two-thirds of the losses affected customers of the exchange, the company said, and the rest belonged to the company. Transactions have been stopped in the meantime.

[above via PYMNTS post] – Update 1 / Update 2
Hackers Demand $2 Million From Monroe
11th July 2019 | Target: **Monroe College **| Reported Here
A ransomware attack at New York City’s Monroe College has shutdown the college’s computer systems at campuses located in Manhattan, New Rochelle and St. Lucia.
According to the Daily News, Monroe College was hacked on Wednesday at 6:45 AM and ransomware was installed throughout the college’s network. It is not known at this time what ransomware was installed on the system, but it is likely to be Ryuk, IEncrypt, or Sodinokibi, which are known to target enterprise networks.
Reports indicate that the attackers are asking for 170 bitcoins or approximately $2 million dollars in order to decrypt the entire college’s network. The college has not indicated at this time whether they will be paying the ransom or restoring from backups while gradually bringing their network back online.

[above via Bleeping Computer post] – Update 1 / Update 2
NHS Faced 11m+ Attacks Over Past Three Years
10th July 2019 | Target: **NHS **| Reported Here
The National Health Service’s email systems were attacked more than 11 million times in the last three years, according to new information from NHS Digital.
That’s more than 12,000 attacks a day, 500 attacks an hour, more than eight attacks every minute, for three years straight.
The numbers come courtesy of a Freedom of Information request and describes exactly the pressure NHSmail infrastructure system is facing.
NHS Digital says the NHSmail system blocked 11,352,000 email attacks. The highest ranking attacks are IP or domain reputation attacks (more than six million), followed by spam (3.6 million). A total of 852,000 incidents were recorded as anti-virus.

[above via IT Proportal post] – Update 1
Cyber-Attacks Cost Global Firms $45bn in 2018
10th July 2019 | Target: **Local Goverment **| Reported Here
An estimated two million cyber attacks in 2018 resulted in more than $45 billion in losses worldwide as local governments struggled to cope with ransomware and other malicious incidents.
The Internet Society’s Online Trust Alliance (OTA), which identifies and promotes security and privacy best practices that build consumer confidence in the Internet, released its Cyber Incident & Breach Trends Report, which found the financial impact of ransomware rose by 60%, losses from business email compromise (BEC) doubled, and cryptojacking incidents more than tripled, all despite the fact that overall breaches and exposed records were down in 2018.

[above via Security Magazine post] – Update 1 / Update 2 / Update 3
Marriott to face $123 million fine by UK authorities over data breach
9th July 2019 | Company: **Marriott **| Reported Here
U.S. hotel group Marriott has become the second firm to face a massive GDPR fine as the UK regulator continues on its rampage. The hotel group, which suffered a breach last year, could face a fine of over £99 million ($123 million). It shows the global impact of the regulation, which covers the personal data of EU citizens.
In a statement of the regulator’s intention to fine Marriott International, UK Information Commissioner Elizabeth Denham said: “The GDPR makes it clear that organisations must be accountable for the personal data they hold. This can include carrying out proper due diligence when making a corporate acquisition, and putting in place proper accountability measures to assess not only what personal data has been acquired, but also how it is protected.

[above via Forbes post] – Update 1 / Update 2
Canonical GitHub account hacked
7th July 2019 | Company: Canonical LTD| Reported Here
Canonical Ltd, the company behind the popular Ubuntu Linux distribution, has had its software repositories on Github hacked by unknown attackers.
The hack appears to be limited to a defacement, with 11 new repos sequentially named CAN_GOT_HAXXD_1, `with no existing data being changed or deleted.
A Canonical spokesperson confirmed the attack to iTnews.
“We can confirm that on 2019-07-06 there was a Canonical owned account on GitHub whose credentials were compromised and used to create repositories and issues among other activities.

[above via IT News post] – Update 1 / Update 2 / Update 3
Hacked forensic firm pays ransom after malware attack
5th July 2019 | Company: **Eurofins Scientific **| Reported Here
Aleading forensic science firm, which is used by the UK police to help investigate major crimes, has paid a ransom to criminals after being targeted in a cyber attack, it is understood.
Eurofins Scientific, which is based in Belgium but has laboratories all over the world, was hit by a ransomware attack last month, which affected the firm’s IT systems.
The National Crime Agency has been investigating the source of the attack, but sources claimed the company had already paid a ransom to recover its network.

[above via Telegraph post] – Update 1 / Update 2
Thousands Left Vulnerable in Nexus Repository
2nd July 2019 | Company: **Sonatype **| Reported Here
A recent breach in Nexus Repository left many companies and government agencies vulnerable, as thousands of private artifacts were left unprotected, according to a July 2 blog post from researchers Daniel Shapira and Ariel Zelivansky, with Twistlock Labs.
While this breach was swiftly rectified, Shapira and Zelivansky noted that this type of hack could have had catastrophic consequences and cannot be taken lightly.
A team of dedicated white hats identified these weaknesses within Nexus Repository. In a July 2 blog post, researchers wrote, “During my recent work I have discovered two security vulnerabilities in Nexus Repository that affect all users under default settings.

[above via Infosecurity post] – Update 1 /
Ford, TD Bank Files Found Online in Cloud Data Exposure
28th June 2019 | Target : **Ford **| Reported Here
Attunity Ltd., a company that manages and safeguards data, left internal files exposed on the internet for clients including Ford Motor Co., and the Toronto-Dominion Bank, in the latest example of sensitive information being publicly accessible on the web.
The incident revealed passwords and network information about Attunity as well as emails and technology designs from some of its high-profile customers. Researchers at UpGuard Inc., a cybersecurity company, found more than a terabyte of data left unsecured by Attunity last month on Amazon Web Services cloud-computer servers, according to a report they published Thursday.

[above via BloomBerg post] – Update 1 / Update 2
Yandex hacked, and likely by Western intelligence agency
27th June 2019 | Internet company : **Yandex **| Reported Here
Hackers working for Western intelligence agencies reportedly broke into Yandex, a Google competitor based in Russia, to search for technical information that shows how Yandex authenticates user accounts.
The hack occurred in 2018, according to Reuters, which sources the information from four people with knowledge of the event. The hackers used a malware called Regin, the same malware used for intelligence sharing
Regin is known to be used by the “Five Eyes,” an intelligence alliance made up of the United States, Britain, Australia, New Zealand and Canada. The countries are bound by an agreement to cooperate on intelligence.

[above via Mediapost post] – Update 1 / Update 2
Two Florida Cities Paid $1.1 Million to Ransomware Hackers
26th June 2019 | Target : **Florida City **| Reported Here
For the second time in a week, a Florida city has paid out a digital ransom to hackers in an effort to regain control over their crippled municipal computer systems.
Lake City Mayor Stephen Witt said his small city located in northern Florida agreed to pay hackers a $460,000 ransom in an effort to regain control over their email and other servers, which were shutdown by the attack two weeks ago.
“I would’ve never dreamed this could’ve happened, especially in a small town like this,” Witt told Action News Jax.
The ‘Ransomware’ attack on the Lake City computer systems locked city workers out of their email accounts and make it impossible for residents to make any city payments online. Hackers managed to infect the city’s systems after a city employee clicked an email link that allowed the malware be introduced into their system. Lake City’s town’s insurer was contacted by the hackers who negotiated the ransom payment of 42 bitcoins (or around $460,000). Officials decided the ransom was the quickest way for city employees to regain access to their email accounts.

[above via Iheart post] – Update 1
Hackers Stole Data from NASA’s Robotics Lab
20th June 2019 | Target : **NASA **| Reported Here
NASA’s Jet Propulsion Laboratory (JPL) systems were reportedly hacked by a Raspberry Pi that helped hackers crack into the weak security and steal data.
As Engadget reports, investigators looking into a security breach found that an unauthorised Raspberry Pi was linked to the JPL network that was targeted by hackers in April 2018, allowing them to steal 500MB of data and also go deeper into JPL’s network.

[above via Business Standard post] – Update 1 / Update 2
Florida city pays $600,000 to hackers who seized its computer system
19th June 2019 | Target : **Florida City **| Reported Here
A city in Florida has decided to pay $600,000 to the hackers behind a ransomware attack that’s locked down the local government’s data.
On Monday, the city council of Riviera Beach voted unanimously to let the city’s insurer pay 65 bitcoins to the hackers. Why the council authorized the payment wasn’t discussed at the emergency hearing. But the city is hoping to recover municipal files the hackers encrypted during the ransomware attack.

[above via PC Mag post] – Update 1 / Update 2
New WSH RAT Malware Targets Bank Customers with Keyloggers
14th June 2019 | Target : **Bank **| Reported Here
According to a blog post by researchers at Cofense, the new strain ofmalware, named WSH Remote Access Tool (RAT) by its developer, is a variant of the VBS (Visual Basic Script) based Houdini Worm (H-Worm) first created in 2013.
This new iteration comes ported to JavaScript (JS) from HWorm’s original codebase of Visual Basic. WSH is likely a reference to the legitimate Windows Script Host, which is an application used to execute scripts on Windows machines.

[above via Scmagazineuk post] – Update 1 / Update 2
City of Burlington falls for Phishing Scam
13th June 2019 | Location: **Burlington **| Reported Here
The city of Burlington says it has fallen victim to a $503,000 phishing scheme. City staff received a “complex phishing email,” requesting to change banking information for an “established city vendor,” the city said in a press release. About $503,000 was transferred to a falsified bank account for the vendor on May 16, the city said. After realizing the mistake on May 23, the city says it immediately notified their bank and Halton Regional Police. They also put in “additional internal controls” to make sure it doesn’t happen again.

[above via CBC post] – Update 1 / Update 2
Hackers Plant Phishing Links in Google Calendar
11th June 2019 | Website: **Google Calendar **| Reported Here
A sophisticated scam is targeting Gmail users through fraudulent, unsolicited Google Calendar notifications as well as through other Google services, including Photos and Forms, according to Kaspersky.
In these scams, criminals are exploiting Gmail calendar’s default feature that automatically adds calendar invitations and notifications.

[above via Infosecurity post] – Update 1 / Update 2
Flipboard says hackers stole user details
29th May 2019 | Website: **Flipboard **| Reported Here
The news aggregation site, Flipboard, has disclosed that their databases had been hacked and unauthorized users have potentially downloaded the data contained within them. This data included the personal account information and digital tokens for some of their over 100 million users.
According to emails seen by BleepingComputer and a security incident notice published on their site, Flipboard stated that hackers gained access to some of their databases during two different time periods.The first time was between June 2nd, 2018 and March 23, 2019 and the second was between April 21st and 22nd, 2019.
It is not known if these were the same users accessing the databases at different periods or two separate data breaches.

[above via BleepingComputer post] – Update 1 / Update 2
Australian ‘unicorn’ Canva hacked
24th May 2019 | Website: **Canva **| Reported Here
Australian graphic-design-as-a-service company Canva has alerted its users to an attack that has seen “a number of our community’s usernames and email addresses … accessed.”
The attack was detected on Saturday, Australian time. The company’s letter to users also adds “The hackers also obtained passwords in their encrypted form (for technical people: all passwords were salted and hashed with bcrypt). This means that our user passwords remain unreadable by external parties.”

[above via CRN post] – Update 1 / Update 2
WhatsApp Hack – Hackers Installed Spyware By Placing A Phone Call
14th May 2019 | Software: **WhatsApp **| Reported Here
WhatsApp pressed users to update its messaging service, following a report that a vulnerability in the software allowed attackers to hack into people’s phones using commercial Israeli spyware. The chat app, owned by Facebook Inc., said it had discovered a vulnerability in early May that could enable attackers to insert and execute code on mobile devices.

[above via Bloomberg post] – Update 1 / Update 2
Hackers Steal $40 Million Worth of Bitcoin From Binance Exchange
7th May 2019 | Website: **Binance **| Reported Here
Hackers have stolen $41m (£31m) worth of Bitcoin in a major crypto-currency heist.
The Binance exchange, which stores Bitcoin and other crypto-currencies for members, said hackers took 7,000 bitcoins in one go. Withdrawals have now been suspended on the platform.
“We beg for your understanding in this difficult situation,” Binance said.
However, the exchange said it would replace the lost cash with the help of its emergency insurance fund.
According to Binance, the attackers used a variety of techniques to break in. They deployed viruses and used phishing attacks to get security information.

[above via BBC post] – Update 1 / Update 2
Phishing Method Which Can Trick Google Chrome Users With Fake Address Bar
29th April 2019 | Application: **Google Chrome **| Reported Here
Why display the URL bar on a mobile device when you can give users more screen space by hiding it?
Google Chrome for Android does just that after a page has loaded, concealing information about the URL and expanding the screen space available to display content from the web page.
The feature is handy for users, but developer James Fisher is drawing attention to the possibility that phishing attackers can abuse it to catch users off guard when browsing.

[above via Zdnet post] – Update 1 / Update 2
Virgin Media Phishing Email
17th April 2019 | Site: **My Virgin Media **| First Reported Here
A phishing email sent to Virgin Media customers, telling them their payment for latest Virgin Media bill has failed and asking them to update billing details.

Update 1 / Update 2 / Other Links 1
The Nasty List Phishing Scam
15th April 2019 | Site: **Instagram **| Reported Here
A new phishing scam called the “The Nasty List” is sweeping through Instagram and is targeting victim’s login credentials.
- If a user falls victim, the hackers will utilize their accounts to further promote the phishing scam.
- The Nasty List scam is being spread through hacked accounts that send messages to their followers stating that they were spotted on a so-called “Nasty List”.
- These profile descriptions also include a link that supposedly allows you to see this Nasty List and why you are on it.
- To avoid falling for an Instagram phishing scam like the Nasty List, if you are at a page that does not belong to the instagram.com web site, never enter your login credentials.
- If you have been hacked by the “Nasty List” phishing scam and you still have access to your account, the first thing you should do is verify that your account is using the correct phone number and email address.

[above via Reddit post]
Wells Fargo Bank – Wellsfargo Online Customer Service
10th April 2019 | Site: **Wells Fargo Bank **| Reported Here
Here is another good example of a phishing email that is presently being circulated. It makes for compelling reading, but it is a scam. Phishing emails, by which scammers and identity thieves attempt to lure you into either clicking on links contained within the email which will download malware or providing personal information that will be used to make you a victim of identity theft, are nothing new.

[above via Scamicide post] – Update 1
Fake cancerous nodes in CT scans
3th April 2019 | Target: **Hospital **| Reported Here
A computer virus that can add fake tumours to medical scan images has been created by cyber-security researchers.
In laboratory tests, the malware altered 70 images and managed to fool three radiologists into believing patients had cancer.
The altered images also managed to trick automated screening systems.
The team from Israel developed the malicious software to show how easy it is to get around security protections for diagnostic equipment.
The program was able to convincingly add fake malignant growths to images of lungs taken by MRI and CT scanning machines.

[above via BBC post] – Update 1 / Update 2
American Express – Important Security Message
20th March 2019 | Company: **American Express **| Reported Here
Microsoft’s Office 365 Threat Research uncovered an active American Express (Amex) email phishing campaign that emerged over the weekend. The Amex phishing campaign is especially dangerous as it prompts the recipient for their credit card numbers, account logins, as well as other common password reset questions.

[above via AskCyberSecurity post] – Update 1
Ransomware Attack Freezes Jackson County, GA Government Systems
9th March 2019 | Place: **Jackson County **| Reported Here
A little over a week ago government computer systems in Jackson County, Georgia were hit with one of the most sophisticated ransomware attacks attempted in the US. After a week with their entire computer and internet network down, they’ve decided to cough up $400,000 to regain control of their systems and to retrieve stolen files.

[above via TechSpot post] – Update 1/ Update 2
FTC Warns Users Against Online Dating Scams!
13th February 2019 | Application: **Tinder **| Reported Here
A new notice released Tuesday by the Federal Trade Commission highlights a surge in ‘romance scams,’ or scenarios where scammers trick love-lusting internet users into sending them money, only to later disappear.
The scams cost victims an astonishing $143 million in 2018, up from $33 million the previous year and making it the most costly type of consumer fraud reported to the FTC.

[above via Dailymail post] – Update 1
Optus Email Scam
8th February 2019 | Site: **Optus **| Reported Here
Optus customers have complained of being caught up in a major security breach after they tried to login to their account and found themselves signed in as Vladimir.
Users say their screen kept refreshing on a loop and one person reported receiving an e-mail with a vastly inflated bill.
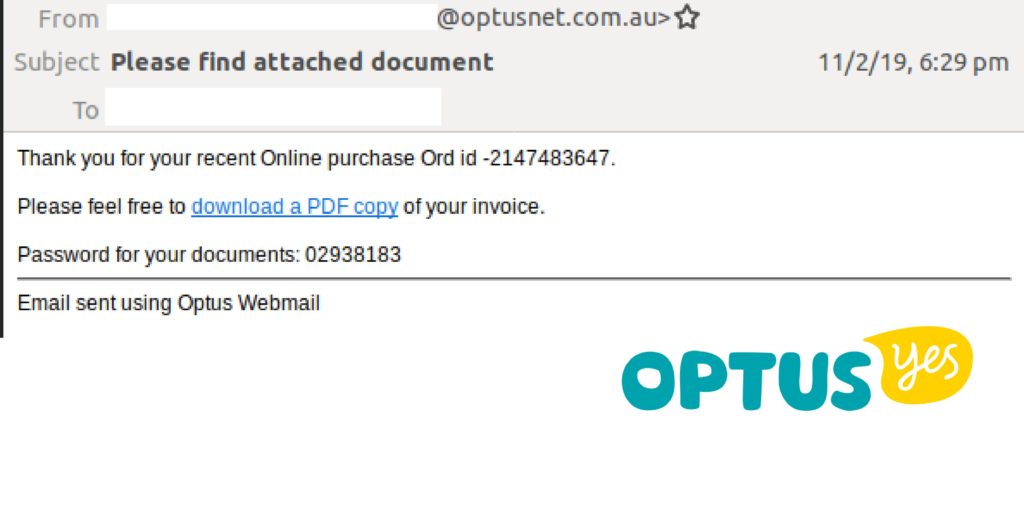
[above via news.com.au post]
Google Translate Phishing Attack
5th February 2019 | Site: **Google **| Reported Here
This week, a security researcher at Akamai outlined a novel phishing approach that they recently encountered in their inbox that attempts to use Google translate links to mask disreputable links.
In January, the researcher received an email informing them that someone had attempted to access their Google account on an unrecognized Windows device.

[above via gizmodo.com post]
Tecnimont Pvt Ltd Attack
10th January 2019 | Site: tecnimont | Reported Here
Attackers forwarded emails to the leader of Tecnimont Private Limited in India which is an Indian subsidiary of the multinational group Tecnimont.
In the emails, the hackers impersonated global C.E.O P. Folgiero and succeeded in convincing the Indian head that a money transfer from Italy was unable to be carried out because of problems with the regulator. They impersonators gave further instructions to make separate transfers to another bank account in Hong Kong.
The money was subsequently transferred from India to the Hong Kong account and withdrawn within moments of the transfer. 18.6 million dollars was lost from the Indian arm of the company due to this simple oversight.

Highly Sophisticated Apple Vishing Scam Detected
8th January 2019 | Company: Apple | Reported Here
A sophisticated Apple vishing scam has been uncovered. In contrast to most phishing attempts that use email, this scam used voice calls (vishing) with the calls appearing to have come from Apple.
The scam starts with an automated voice call to an iPhone that spoofs Apple Inc. The caller display shows that the call is from Apple Inc., increasing the likelihood that the call will be answered. The user is advised that there has been a security breach at Apple and userIDs have been compromised. Users are told they should stop using their iPhone until the problem has been resolved. They are asked to call back Apple support for further information and a different telephone number is provided for this purpose.

[above via Netsec post] Update 1
Netflix Phishing Attacks
26th December 2018 | Site: **Netflix **| Reported Here
A new bulletin issued by the Federal Trade Commission highlights a fresh wave of Netflix phishing scams that have been landing in email inboxes around the globe.
The scam itself is old. It’s a classic “update your payment information” request that includes a link to a fake Netflix login screen where gullible folks might enter their details, and it’s the kind of thing that we see pretty regularly in our spam filters and junk mail folders, but this particular scam is apparently widespread enough to have drawn the attention of the FTC.

[above via bgr.com post]
Office 365 Non-Delivery Email Phishing Attack
13th December 2018 | Platform: Office 365| Reported Here
A phishing campaign has been discovered that pretends to be a non-delivery notifications from Office 365 that leads you to a page attempting to steal your login credentails.
This new campaign was discovered by ISC Handler Xavier Mertens and states that “Microsoft found Several Undelivered Messages”. It then prompts you to click on the “Send Again” link in order to try sending the emails again. An example of this phishing email can be seen below.
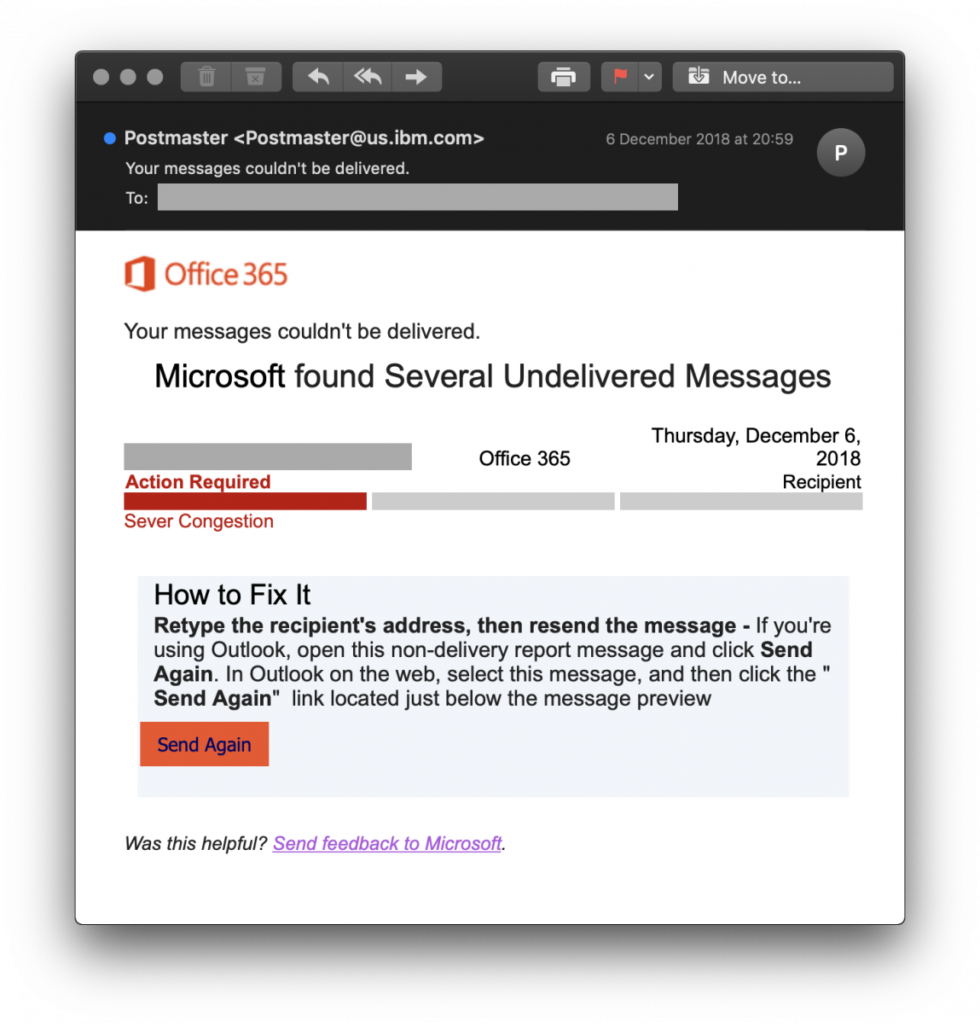
[above via bleepingcomputer.com post]
Quora Gets Hacked – 100 Million Users Data Stolen
4th December 2018 | Website: **Quora **| Reported Here
The World’s most popular question-and-answer website Quora has suffered a massive data breach with unknown hackers gaining unauthorized access to potentially sensitive personal information of about 100 million of its users.
Quora announced the incident late Monday after its team last Friday discovered that an unidentified malicious third-party managed to gain unauthorized access to one of its systems and stole data on approximately 100 million users - that’s almost half of its entire user base.

[above via Thehackernews post] Update 1 / update 2
Apple ID Phishing Attack
20th October 2018 | Site: **Apple **| Reported Here
A widespread and sneaky phishing campaign is underway that pretends to be a purchase confirmation from the Apple App store. These emails contain a PDF attachment that pretends to be a receipt for an app that was purchased by your account for $30 USD and tells you to click a link if the transaction was unauthorized. Once a user clicks the link, down the rabbit hole they go.
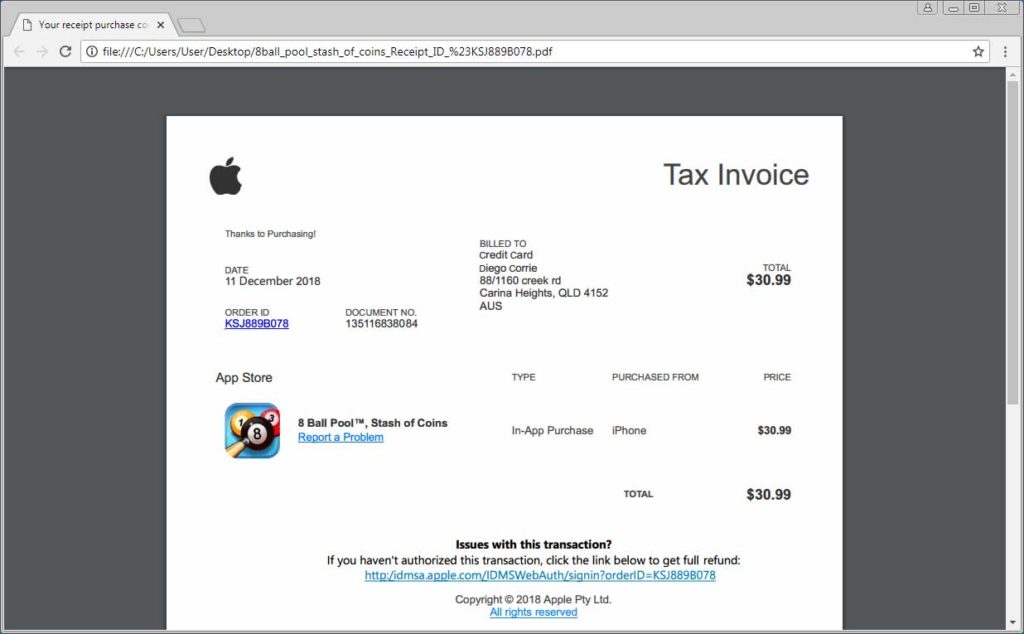
[above via bleepingcomputer.com post]
Czech Republic SMiShing Attack
26th January 2017 | Location: Czech | Reported Here
Reports stated that attackers sent smishing text alerts and the SMS sent seemed to be from the Postal Service of the Czech Republic.
Recipients were lead to click on a link which opened up a website designed to look like the official site of the Czech Postal Service which eventually led victims to download malware in the form of an app which contained a Trojan Horse virus.
Sophisticated social engineering tactics which are the hallmark of phishing were employed by the attackers in convincing them to download an app from a non-trusted site.

Amazon Locky Ransomware Attack
25th May 2017 | Site: **Amazon **| Reported Here
Comodo Threat Research Labs states that this massive phishing attack began on May 17, 2016, when cybercriminals sent around a hundred million spam messages to customers around the world. The attack lasted for 12 hours and succeeded in causing tremendous damage to the company’s reputation and the finances of several of its customers.
Phishers sent emails to customers of Amazon with a subject line “Your Amazon.com Order Has Dispatched (#code)” with the sender address as “auto-shipping@amazon.com”.
These emails had a word document attached to them which contained image macros. As customers enabled image macros by clicking on the document, a type of virus called ransomware made its way into their computer systems and encrypted all their files. It then threatened the victims with deletion of their files unless the ransom was paid.

The Walter Stephan Case
25th May 2016 | Company: **FACC **| Reported Here
Cybercriminals faked the email of the CEO of FACC, Walter Stephan and ordered the employees of his company to hand over vast sums of money to a shady bank account by telling them that it was part of a fictional acquisition project. The attack caused losses to the tune or 47 million dollars to the company. Mr Walter Stephan was then found to be guilty of not carrying out his duties by the supervisory board of the company and had to lose his job.

Ubiquiti Networks CEO Fraud
7th August 2015 | Company: **Ubiquiti **| Reported Here
Ubiquiti is a well-known American technology company and was the unfortunate victim of phishing attacks in June 2015. The attackers were well-prepared and forwarded fraudulent emails requesting wire transfers to the employees of the company.
The unsuspecting employees went on to approve these transactions leading to huge losses of around 40 million dollars for the firm. The firm ended up being able to recover a measly $8.1 million, but the rest of the money ended up in the attacker’s hands.

The RSA Attack
26th August 2011 | Company: **RSA **| Reported Here
The most significant cybercrime case of 2011 was the hacking of the leading security firm RSA by attackers who managed to break into its decidedly secure networks.
The firm sells security solutions to over 40 million businesses and is considered to be one of the world’s leading computer-security companies.
This makes the fact that its employees fell victim to an email phishing attack titled “2011 Recruitment Plan” all the more ironic. It shows us that we can never be too careful when it comes to cybersecurity and even the very best can fall victim to it if not adequately prepared. The Phishing email led employees to download malware via Adobe Flash, which used FTP to transfer several secured RAR files from RSA’s dedicated server to an external host. These files were then removed from the external host, and no traces were left.

Update 1 / Update 2 / Update 3
Anthem Server’s Attack
9th February 2015 | Company: **Anthem **| Reported Here
At around the same time, Ubiquiti was compromised by attackers, and the most massive healthcare breach ever recorded occurred when servers of Anthem was attacked by hackers who succeeded in tricking five employees of the company into opening a phishing mail. This action caused them to download a keystroke-logging malware which in turn led to more than 80 million medical records and files belonging to the Blue Cross and Blue Shield Authority being seized.

Update 1 / Update 2 / Update 3
Operation Phish Phry
10th July 2009 | Operation : **Phish Phry **| Reported Here
Aside from the funny name, Operation Phish Phry was a serious cybercrime investigation which was conducted as a joint operation between the American FBI and Egyptian authorities. The case is historically significant as having had the largest number of defendants on record in the world of cybercrime.
These attackers had illicitly stolen nearly USD 1.5 Million from thousands of victims and transferred their ill-gotten gains to various phoney accounts around the world. These criminals were part of one of the world’s largest nexus of organized crime online dedicated solely to email phishing attacks.
