Encrypted RPMSG Exploited In Microsoft 365 Phishing – Cybersecurity News

Quick Answer
Online attacks continue to become more sophisticated, and malicious players are deploying more innovative tactics than ever to launch [phishing attacks](/resources/7-most-common-phishing-attacks-and-learning-to-protect-against-them). One of the latest tactics is using **RPMSG files** to extract users’ Microsoft login credentials.
Online attacks continue to become more sophisticated, and malicious players are deploying more innovative tactics than ever to launch phishing attacks. One of the latest tactics is using RPMSG files to extract users’ Microsoft login credentials.
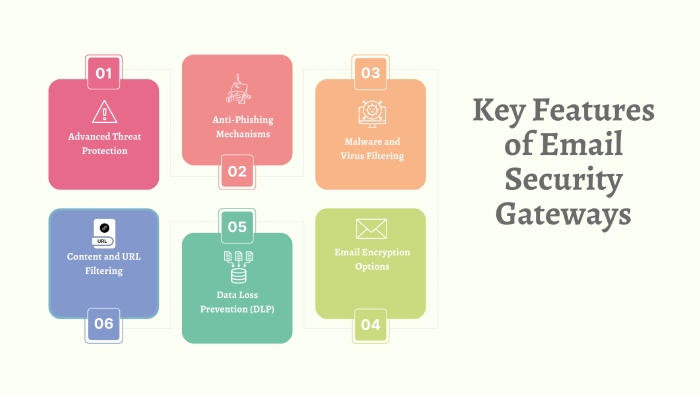
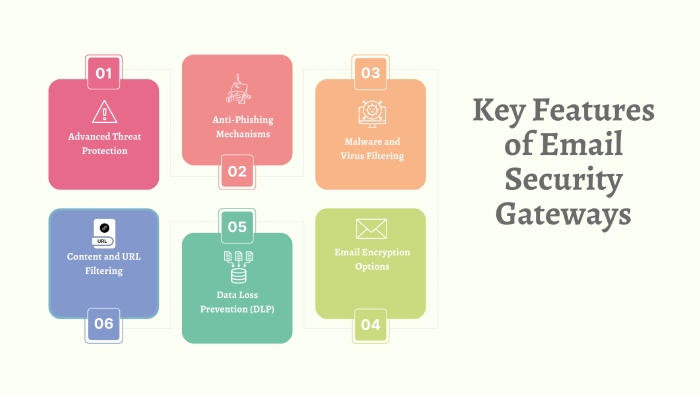
In recent development, threat actors have adopted a new attack mechanism in the phishing world. They are utilizing encrypted RPMSG attachments delivered through compromised Microsoft 365 accounts. The attack vectors have been designed to steal the Microsoft credentials of users and are specifically crafted to evade detection by email security gateways.
RPMSG (restricted permission message) files use Microsoft’s Rights Management Services (RMS) for encrypting email message attachments. It delivers an additional layer of protection to sensitive information as they restrict access only to authorized recipients.
In a recent discovery by Trustwave, a platform known for its rapid threat detection and response, attackers have successfully tricked victims into divulging their Microsoft credentials using fake login forms. The online attackers have managed to leverage the authentication requirements of RPMSG to exploit the vulnerabilities.
How Does the New Phishing Attack Model Work?
The new wave of online attacks begins with an email from a compromised Microsoft 365 account. These emails often impersonate legitimate organizations, replicating a typical phishing attack mechanism. Trustwave identified Talus Pay, a payment processing organization, as a compromised account.
The phishing emails prompt recipients to click a “Read the message” button to decrypt and access the protected message. Usually, these recipients are targeted members of the billing department. Once they click the button, they are redirected to an Office 365 webpage. This page requests them to sign into their Microsoft account for authentication.
Once they receive authentication through this MS service, the attackers present their phishing emails to them. That leads them to a counterfeit SharePoint document hosted on Adobe’s InDesign service. A “Click here to Continue” button within the document redirects victims to a final destination. They find an empty page displaying a “Loading…Wait” message that serves as a decoy.
At the same time, a malicious script collects various pieces of system information. That includes crucial data such as connect token and hash, video card renderer information, visitor ID, system language, hardware concurrency, device memory, installed browser plugins, OS architecture, and browser window details.
Once the malicious players collect the data, they display a cloned Microsoft 365 login form to the victims. If they enter any passwords or usernames, the attackers receive the details on their servers.
What Makes This Attack Mechanism So Difficult to Detect?
“Microsoft’s built-in phishing protection in Office 365 catches the obvious attacks, but it consistently misses targeted spear phishing and zero-day threats. We see this every day - customers come to us after an incident that Microsoft Defender didn’t catch. Adding a dedicated anti-phishing layer takes five minutes and closes that gap.” - Adam Lundrigan, CTO, DuoCircle
Trustwave researchers explain that the targeted nature of these phishing attacks makes it challenging for cybersecurity experts to detect their operations. Besides, the attackers use trusted cloud services like Microsoft and Adobe to dispatch phishing emails. Furthermore, the hosting content remains on these platforms, which makes the system immune to easy detection.
Trustwave has advised enterprises and businesses to educate their users to mitigate risks associated with phishing attacks. Once the potential victims know the threat’s nature, they can take adequate phishing protection measures to draw their line of defense .
How Should Organizations Brace Themselves to Counter Phishing Attacks?
As phishing techniques continue to evolve, individuals and organizations must remain vigilant. Employees must exercise caution while interacting with emails and keep their security measures current.
Encrypted RPMSG messages present a new challenge for email scanning gateways. Under this new attack model, the phishing content, including URL links, remains concealed . The email body has a single URL link pointing to an encryption service of Microsoft.
However, a potential red flag is the URL’s sender address (e.g., chambless-math.com). The sender address is not related to the email’s apparent sender. This link is likely generated from another compromised Microsoft account.
Cybersecurity experts recommend the following measures to mitigate the risks associated with these phishing attacks.
- Maintain a protective approach against inbound messages with .rpmsg attachments from external sources . Depending on the expected volume and the necessity of receiving such attachments, your employees may choose to block, flag, or manually inspect them.
- Organizations must be watchful of the subject line of incoming emails from the source, MicrosoftOffice365@messaging.microsoft.com . If the subject line reads “Our one-time passcode to view the message,” it may be a phishing attempt. This surveillance can detect users who have received RPMSG messages and have requested a passcode.
- Trustwave also advises the users not to try and unlock or decrypt messages received from unknown sources. They also recommend enabling multi-factor authentication (MFA) for Microsoft 365 accounts. It will erect a robust wall of defense to repel the chances of unauthorized access and boost security.

Final Words
Cybersecurity experts continue to track this RPMSG-based malicious campaign and recommend updated protective measures as necessary. By implementing these mitigation strategies and staying informed about emerging threats, organizations can strengthen their defense against targeted phishing attacks exploiting encrypted RPMSG messages.
Protect Your Organization
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead across DuoCircle's 2,000+ customer base.
LinkedIn Profile →Protect your inbox from phishing attacks
Real-time email security with 60-day free trial. No credit card required.