Are Android devices safe to use? The answer could be ‘Yes’ or ‘No’ given the Guerrilla malware implanted in many Android devices by the Lemon Group. Read on to know more.
Android is easy to use but could also be risky sometimes. The latest update on phishing protection reveals that cyber threat actors known as the Lemon Group are using Guerrilla malware to infect domestic Android devices and create data privacy issues.
The activities include loading additional payloads, intercepting OTPs from SMSs, hijacking WhatsApp sessions, and setting up reverse proxy accounts from infected devices. Besides your smartphone, many other devices, such as TVs, smartwatches, and music players, could be running on Android software.
The Guerrilla Malware
The Guerrilla malware gets its name from guerrilla warfare tactics adopted by yesteryear’s warriors. Threat actors attack the most vulnerable systems, with the owner unaware of how and when the attack occurs.
Threat actors like Lemon Group specialize in infecting Android devices, especially those re-flashed with new ROMs. This malicious group has infected millions of Android smartphones, smartwatches, smart TVs, and other devices working on Android software.
How Does Guerrilla Malware Work?
The Guerrilla infection converts the infected devices into mobile proxies for stealing user credentials, OTPs, SMS messages, social media interactions, and online messaging accounts.
Additionally, the Guerrilla malware enters these devices through supply chain attacks, compromised firmware updating processes, vulnerable third-party software, or through listing the services of third parties on the product manufacturing or distribution chain.
Reports show that new Android smartphones come with the modified firmware already implanted by the Lemon Group. It is possible because of the proliferation of many cheap Chinese Android mobile phone models in the market. Users get excited by attractive sales gimmicks and purchase cheap smartphones from roadside vendors. These devices are the most vulnerable to Guerrilla malware.
The affected devices have a modification on the ‘libandroid_runtime.so’ system that contains an additional code for decrypting and executing a DEX file. The DEX file code loads into the memory and activates the main plugin used by the attackers when the system executes the Android Runtime operation.
The Different Plugins of Guerrilla Malware
The Guerrilla Malware loads the below-mentioned plugins for carrying out malicious activities.
- SMS Plugin – For intercepting OTPs received through SMS
- Cookie Plugin – Dumps cookies from the directory of app data and exfiltrates them to the C2 server. Besides, it hijacks WhatsApp sessions to steal messages
- Proxy Plugin – Sets up a reverse proxy on the target’s phone, enabling malicious actors to exploit the victim’s network resources
- Splash Plugin – For displaying intrusive advertisements when users access legitimate applications
- Silent Plugin – Installs additional APKs received from the C2 server and uninstalls applications as instructed
Lemon Group has established a monetization strategy using such plugins, including selling compromised accounts, offering app installation and proxy services, SMS and PVA services, and hijacking network resources.
Global Impact
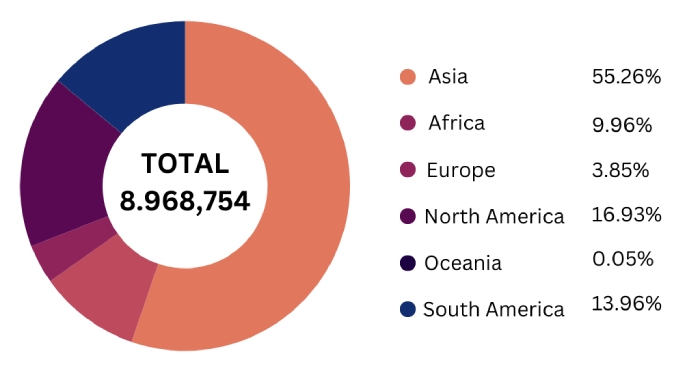
As Asians use the maximum number of Android devices, Asian countries are the most affected by Guerrilla malware. However, devices in the American continent and other Western countries have also been affected.
However, Asia continues to dominate, with nearly 55.26% of the total affected devices found in countries like Indonesia, Thailand, etc. The American continent accounts for 30.89% of the total cases. The Oceania region comprising Australia and New Zealand is the least affected.
These figures are indicative, and the number of affected devices could be higher. Many devices might not have communicated with the attacker’s C2 servers yet, for they might not have yet been purchased.
Final Words
So, is purchasing an Android device unsafe? The answer is ‘No’ if you purchase them from reputed showrooms selling genuine products. However, if you compromise quality for the price and buy cheap models, you might pay a heavy price later by letting the Guerrilla malware into your network systems and allowing it to wreak havoc on your information assets.