Phishing remains the top method that cybercriminals use to target individuals and employees worldwide to lure them in and lead them to fake applications, websites, and payment portals to steal information and hard-earned money.
VadeSecure’s latest report highlights how financial services is the most impersonated sector today, along with Facebook and Microsoft taking the crown for the most impersonated brands by phishing criminals. It is imperative to understand the rising threat of phishing, the latest phishing scams, and how you can ensure your organization’s protection against phishing.
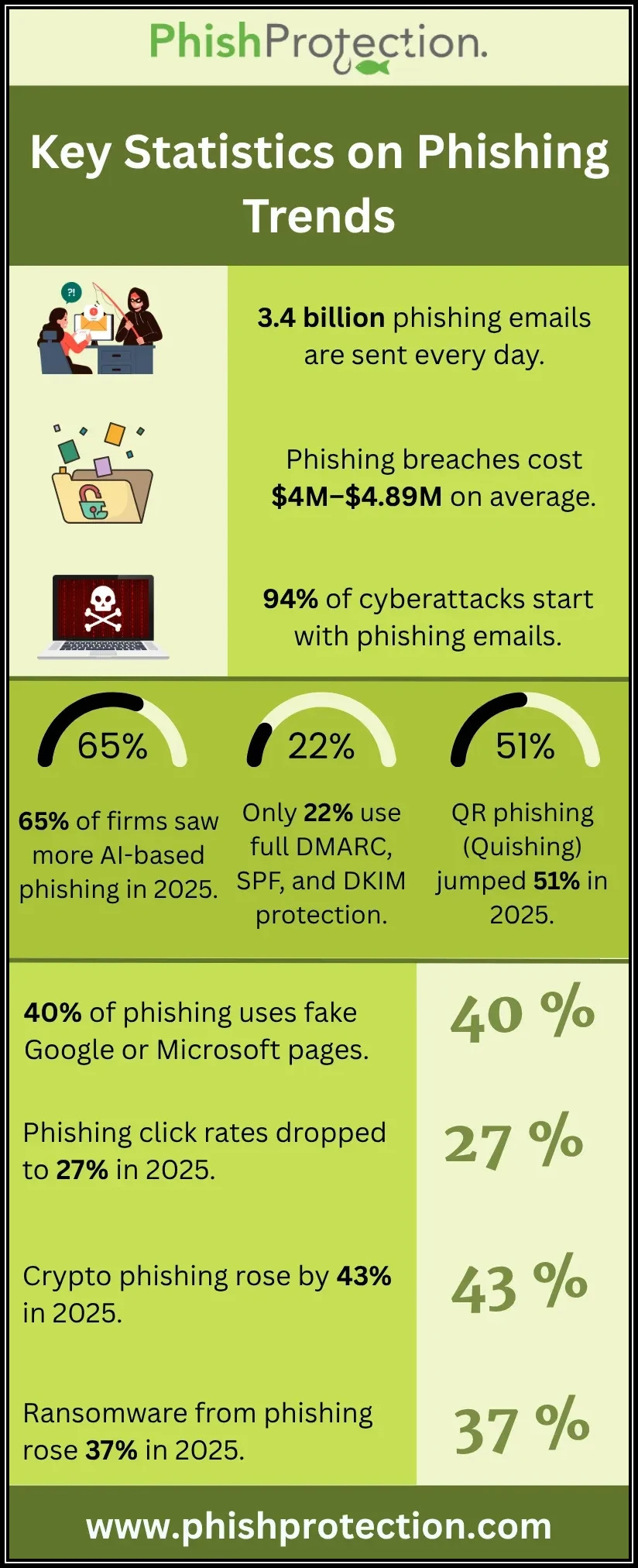
Key Statistics
Nearly 184,977 phishing emails and websites analyzed by Vade in 2021 revealed that:
- The most impersonated social media platform is Facebook, used in 14% of phishing pages.
- The most impersonated corporate brand is Microsoft, at 13%.
- The most impersonated sector is Financial Services, at a substantial 35%, followed by social media at 24%, and Cloud at 19%.
- Credit Agricole, the most impersonated financial service, featured on 13% of phishing websites.
- Phishing is highest during weekdays at 78%, with weekends at 22%, and Tuesday topping the list with the highest phishing attacks.
Why Do Cybercriminals Impersonate Facebook and Microsoft for Phishing?
Facebook is the most widely used social media platform with nearly 2.89 billion monthly active users, making it a prime impersonation brand for harming unsuspecting and innocent users worldwide. Facebook phishing is carried out by malicious actors via emails impersonating Facebook, fake security alerts for password reset recommendations, and post links that redirect to phishing login pages for stealing Facebook account credentials. Cybercriminals can use these credentials to carry out malicious activities, access confidential data and personal information, social engineering, impersonation, and target friend accounts.
Microsoft is the go-to for businesses worldwide owing to its affordable, secure, adaptable, collaborative, and popular services. Microsoft phishing attacks were more sophisticated with automated tools that rendered official corporate logos and images into Microsoft phishing pages with links explicitly designed to work if the particular victim received it, causing them to become inactive for regular users. Cybercriminals validated the targeted individuals utilizing APIs (Application Programming Interface) and user email addresses.
What Makes Financial Services Prime Targets for Phishing?
The financial services sector is a prime target for phishing by malicious actors owing to the significant opportunity of substantial monetary gains. The rise in impersonation of financial services was boosted by Covid-19, with organizations and individuals worldwide rushing for loans from federal-backed banks and credit unions. Financial institutions are returning to standard procedures, with loans and payments becoming active after the expiration of deadlines.
Cybercriminals have a new opportunity to scam and exploit businesses struggling with finances. Financial Institutions are enticing targets for malicious actors as they have a lot of confidential customer information and bank account details. Moreover, the impersonation of financial services with phishing links and payment portals can trick many individuals into submitting payments for dues.
Latest Phishing Scams
Phishing attacks impersonating major brands is not the only revelation of the report, which highlights the latest phishing scams, which are:
- COVID-19 themed phishing: The year also saw business email accounts receive millions of pandemic phishing emails every month, with Vaccine Messages, Vaccine Survey Responses, and Survey Confirmations as the primary subject of the emails. These covid phishing emails were sophisticated enough to bypass detection and employed the usage of random noises in the text concealed under images to avoid email filters. The phishing links also featured the usage of famous and known domains that required an account setup, tricking you into paying delivery charges for receiving a prize when visiting the phony website.
- Tech support: Phishers are also using technical support emails, targeting individuals working from home. These technical support phishing emails were harder to suspect as they featured a phone number instead of an email. The email instructed individuals to call on the phone to renew or cancel their subscriptions, thereby baiting them. Once they reached the number, the cybercriminal on the other side of the call instructed them to install remote desktop access software on their devices and deploy malware or additional malicious tools on the innocent victim’s systems by convincing them of the presence of viruses and malware and the need for a solution.
However, this was the first wave of technical support phishing scams that later transformed into Apple and Amazon impersonation emails containing fake invoices of massive purchases, provided with a phishing phone number for cancellation or assistance.
Defending Against Phishing Attacks
The report has made it clear that cybercriminals are continuously changing their tactics to dupe you out of critical information and finances. However, you can fight back and defend against this latest COVID and technical support phishing, and other all kinds of phishing scams by:
- Automated Protection Tools: AI (Artificial Intelligence) plays a significant role against phishing with specialized algorithms that can identify spear-phishing attack traits and even detect evasive tactics employed by threat actors.
- Staff Training: Organizations should invest in staff training to help them understand the risks of phishing and privy them to the latest phishing tactics and how to avoid them for the best anti-phishing services.
- Identification: Sophisticated attacks might not be caught by the human eye, but you can quickly identify other spear-phishing emails, phishing websites, and scams as they feature grammatical errors or unknown domain names in the links.
- Natural Language Processing (NLP) tools: Along with AI and machine learning algorithms to detect odd emails, NLP can detect phishing emails via the association of common flag words in spear-phishing emails.
- Learning tell-tale signs: You should also educate yourself to the tell-tale signs that a phishing email includes, such as grammatical errors, requests for personal information, unsolicited services or subscriptions, the difference in sender email and signature, multiple recipients of the email, and the emails general content instead of addressing your name.
Final Words
The latest phishing report has made it clear that cybercriminals are evolving their techniques to dupe innocent individuals and organizations with sophisticated phishing campaigns for robbing them of personal information and finances. You can defend against phishing attacks by following the methods mentioned above. Furthermore, staying alert while opening unsolicited emails ensures better protection, so a simple click does not cause significant losses.