Why More and More Phishing Attacks are Going After Mobile Users

Quick Answer
Phishing attacks are hard to stop because hackers are extremely sophisticated and they use every method available. What hackers have discovered is that one of the best methods available is to target mobile devices. As challenging as it is for users to identify well-constructed phishing emails on a desktop, it's much more difficult on mobile devices and hackers know it.
Phishing attacks are hard to stop because hackers are extremely sophisticated and they use every method available. What hackers have discovered is that one of the best methods available is to target mobile devices. As challenging as it is for users to identify well-constructed phishing emails on a desktop, it’s much more difficult on mobile devices and hackers know it. And they’re starting to take advantage of it.
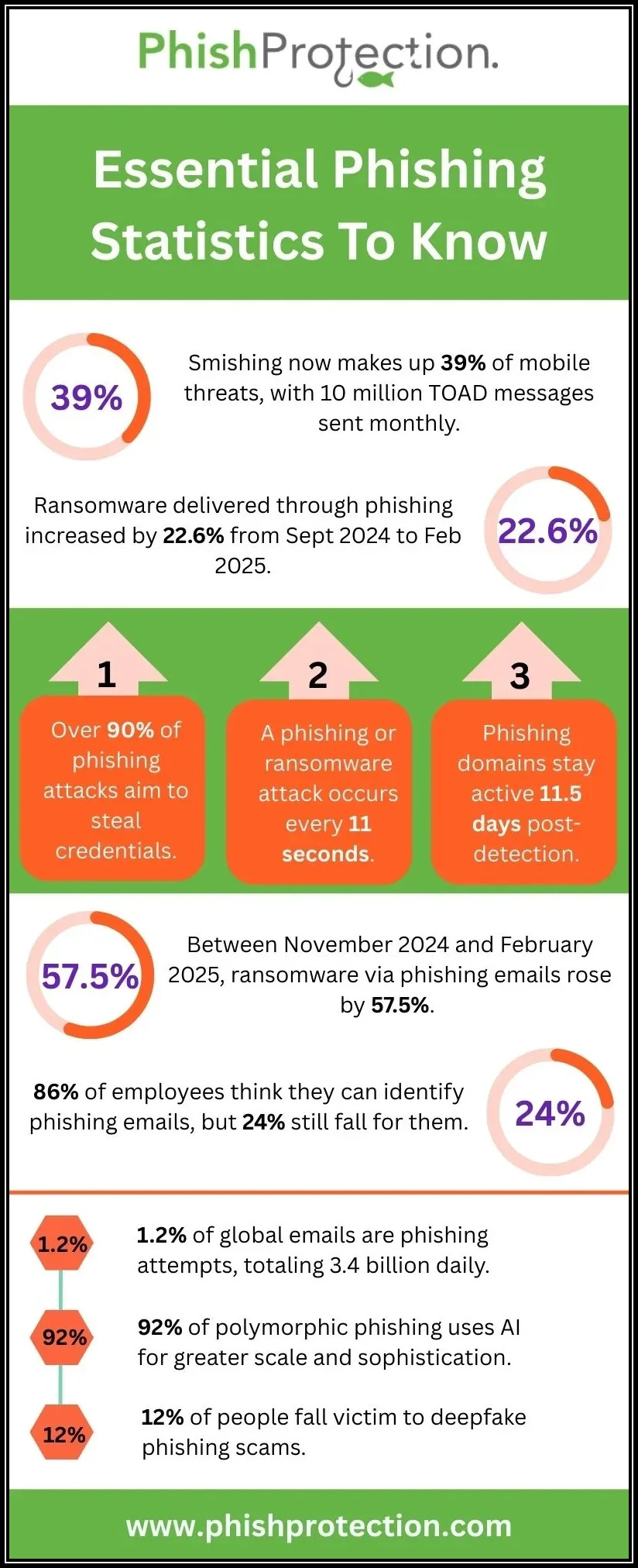
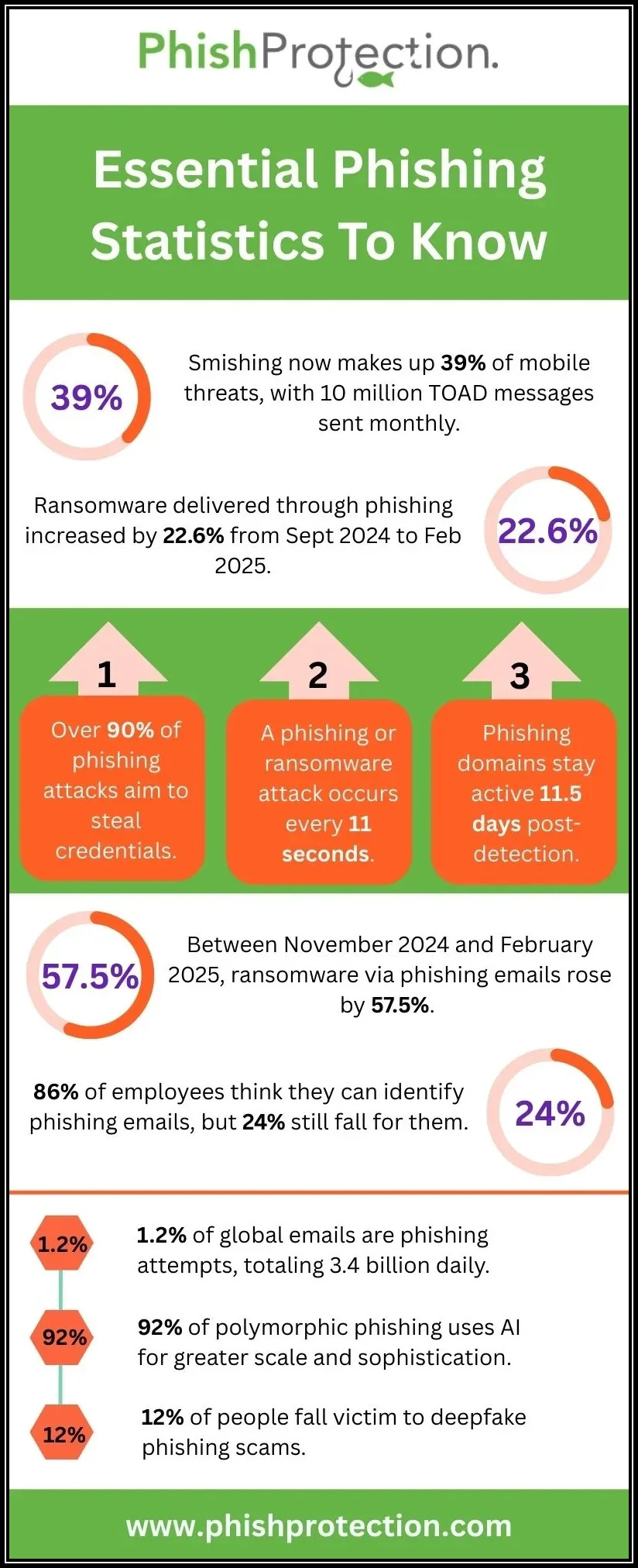
According to an article by security firm cyperscoop ,Phishing attacks against mobile devices rise 85 percent annually**. ** Why is that?
From the article,
“I_t’s harder to spot phishing websites on mobile devices_ compared to a desktop computer which puts the most important device in people’s lives at a distinct disadvantage. As a result, mobile users are historically more likely to fall for phishing attacks.”
It used to be that malware was the big threat to mobile devices. Not anymore . “Though malware has claimed the lion’s share of mobile-related security headlines, phishing is actually a much bigger threat. Users on a mobile device are 18 times more likely to be exposed to phishing, than to malware, according to Dr. Michael J. Covington, VP of Product at Wandera, a mobile security vendor.”
One phishing attack against mobile devices is so good, it fools almost everyone who encounters it because it doesn’t look like a phishing attack at all. This new form of phishing is a type of clickjacking which incorporates an
invisible link. The invisible link is covered by a “bothersome” graphic element that’s made to look like a small hair or a speck of dust. This tricks the user into wiping the hair or dust off the mobile’s screen which activates the link and launches a connection back to a rogue website.
In another recent attack aimed specifically at mobile devices, Google Translate was used to serve fake login pages to Google and Facebook users. According to an article on SecurityWeek ,“The attack started with a basic notification sent to the intended victim’s email address. When viewed on a mobile phone, the message is condensed and seems legitimate. However, if the user switches to a desktop PC, it becomes clear that the email is a phishing attempt.”
Humans are no match for these advanced phishing techniques targeting mobile devices. If enough people at your organization receive one of these emails, someone’s going to get phished.
The only chance you have to protect your users is to deploy cloud-based phishing protection with real-time link scanning.
Unlike humans, link scanners aren’t fooled by misleading and hard to read links. All they see is the underlying HTML code, and there’s no way to fool a link scanner with that. And the protection must be cloud-based . A cloud-based link scanner sits between the mobile device and the malicious website. That gives it a chance to check and block the email before it ever reaches the client’s mobile device.
Phishing attacks are hard to spot on mobile devices. If you’re a small business on a limited budget, but you’d still like to be protected from advanced phishing techniques like these, there’s good news. You can now get advanced phishing technology at a price that fits your budget.
To learn more about how PhishProtection can protect your small or mid-size business from phishing attacks, including those specifically targeting mobile devices.
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead across DuoCircle's 2,000+ customer base.
LinkedIn Profile →Protect your inbox from phishing attacks
Real-time email security with 60-day free trial. No credit card required.