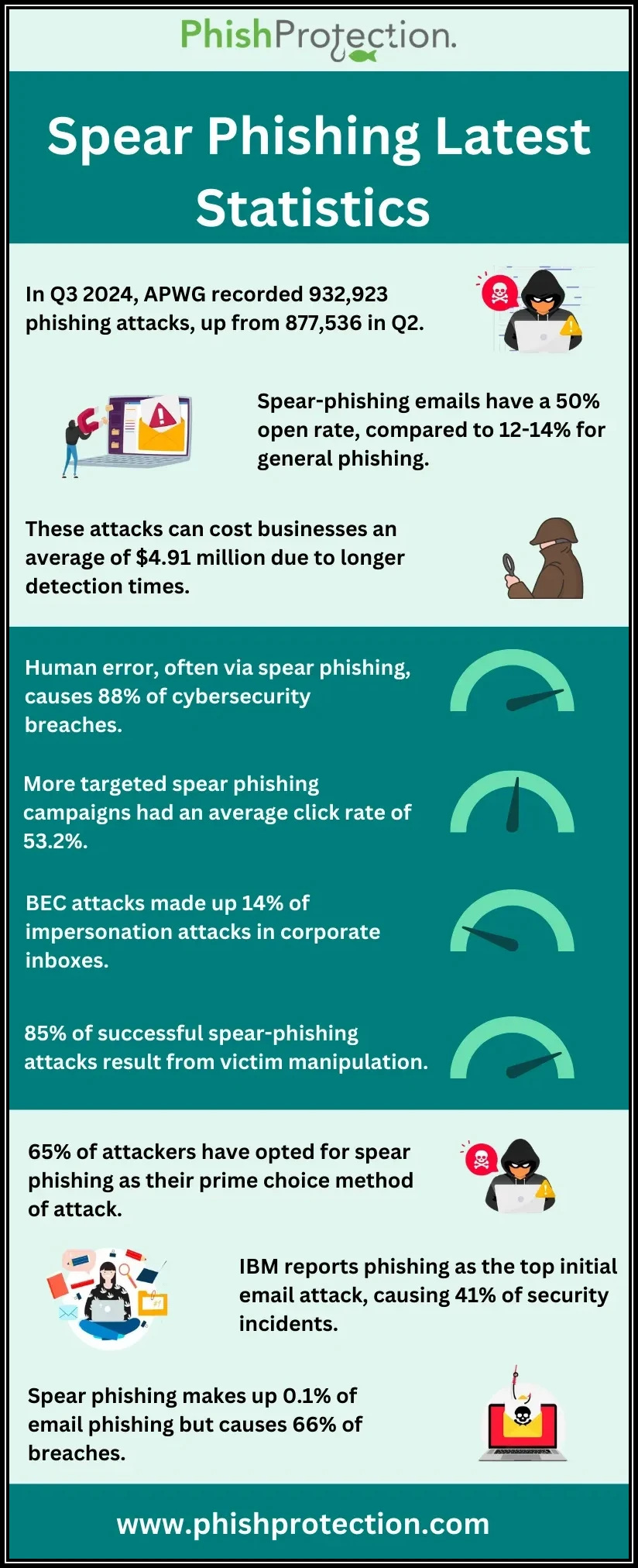
What’s the greatest threat to democracy today? How about election results that can’t be trusted because the election was manipulated by hackers. Hackers who began their attack with a spear phishing campaign. It’s happened before. It will almost certainly happen again.
Manipulating campaigns is now part of the election process. And the number of ways it can be manipulated is scary to think about. It could be as simple as hijacking a social media account to post fake election results. Or, it could be a sinister as hijacking a county website and posting fake voting instructions about where, when and how to vote. And no matter what form it takes, it will almost certainly start with a spear phishing attack.
The problem has attracted a lot of attention. According to Krebs on Security, “a grand jury from San Mateo County in northern California released a report which envisions the havoc that might be wrought on the election process if malicious hackers were able to hijack social media and/or email accounts and disseminate false voting instructions or phony election results. The report notes that concerns about the security is hardly theoretical: In 2010, intruders hijacked election results web page.”
We already know that spear phishing impacted the last presidential election. As I wrote about in the blog post, Mueller Report Unravels Politically Motivated Spear Phishing Cyber Attack, “The Muller Report also claims that the hack compromised the entire email account of the campaign chairholder Podesta. The investigation does establish a particular benefit to the Trump presidency.”
Stop spear phishing and you stop election manipulation. But it’s hard to do, because the hackers are clever and they keep evolving. You can try awareness training, but that’s never 100% successful.
To maintain the sanctity of our elections, it should be required that everyone associated with the election process have advanced email security specifically designed to prevent spear phishing attacks. That means, at a minimum, the email security include:
- Real-time link click protection
- Domain name spoofing protection
- Display name spoofing protection
- Smart quarantine
- Malicious attachment blocking
- Advanced email authentication including SPF, DKIM and DMARC
I know when I go to vote I want my vote to count. If we can maintain the sanctity of our democracy by protecting the voting process with readily-available and easily affordable technology like Phish Protection, then we have to do it.